TL;DR: The Key Takeaways
🚀 IDORs (Insecure Direct Object References) are one of the most common and critical vulnerabilities in modern web apps.
💀 They occur when an application trusts user input too much and fails to validate authorization.
🔍 Simple IDs (like
/user/100) are the easiest to exploit, but GUIDs/UUIDs aren't bulletproof.
⚡ Tools like Burp Suite and AuthMatrix are your best friends for spotting these.
💰 Impact is huge: From leaking PII (Personally Identifiable Information) to full Account Takeover.
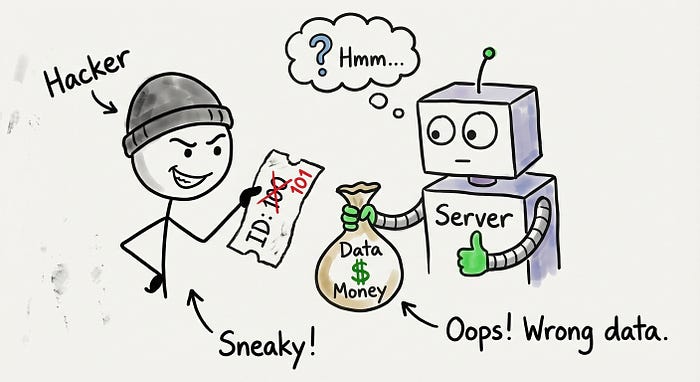
Imagine walking into a bank. You ask to see your balance.
The teller asks for your account number.
You give them your number. They show you your money.
Now, imagine you walk in again. But this time, you give them a random number.
And the teller still shows you the balance for that account.
That is exactly how an IDOR works.
It sounds too stupid to be true, right? Yet, it happens every single day.
Let's dive deep into how this works, how to find it, and how to get paid for it.
💀 What Actually is an IDOR?
In the cybersecurity world, we love fancy acronyms.
IDOR stands for Insecure Direct Object Reference.
It sounds complex, but the concept is incredibly simple.
It happens when a developer exposes a reference to an internal database object (like a file, a user ID, or an invoice number) directly in the URL or API parameters.
Crucially, they forget to check if the person requesting that object is actually allowed to see it.
The Anatomy of the Attack
Let's look at a typical URL structure.
You might see something like this in your browser:
https://example.com/profile?user_id=1050As a hacker, your brain should immediately light up.
Why? Because 1050 looks like a sequential number.
If you are user 1050, what happens if you change that number to 1051?
If the application returns the profile for user 1051, you have just found a vulnerability.
This is a breach of confidentiality. And in the bug bounty world, this pays.
🔍 Phase 1: The Reconnaissance
You can't hack what you can't see.
To find IDORs, you need to understand how the application talks to the server.
This means you need a proxy. Enter Burp Suite.
If you aren't using Burp, you aren't doing bug bounties.
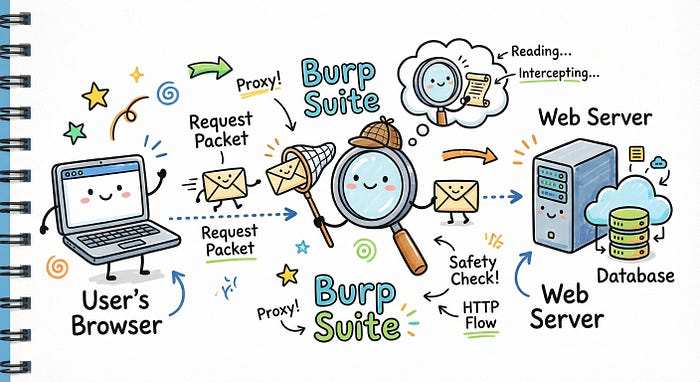
Capturing the Traffic
Open your target application. Click on everything.
Update your profile picture. Change your password. View your past orders.
Every time you click, look at your HTTP history in Burp.
You are looking for parameters that identify resources.
Keep an eye out for these keywords:
- id=
- user_id=
- account=
- pid=
- invoice_ref=
Once you spot one of these, send that request to Repeater.
Repeater is where the magic happens. It allows you to replay the request but change the data.
🚀 Phase 2: The Exploitation
Now comes the fun part.
You have a request that works for your own account.
It looks valid. The server is happy.
Now, we test the boundaries.
Scenario A: The GET Request
Let's say you found an API endpoint that fetches your shipping address.
GET /api/v1/user/address/550 HTTP/1.1
Host: shop.example.com
Cookie: session=YOUR_SESSION_COOKIEThis returns your address.
Now, change 550 to 551.
GET /api/v1/user/address/551 HTTP/1.1
Host: shop.example.com
Cookie: session=YOUR_SESSION_COOKIEIf the response contains someone else's address, boom.
You have a PII leak.
Scenario B: The POST/PUT Request (The Dangerous One)
Reading data is bad. Changing data is worse.
Imagine a request that changes your email address.
POST /api/change-email HTTP/1.1
Host: example.com
Content-Type: application/json
{
"user_id": 550,
"new_email": "hacker@evil.com"
}If you change user_id to 551 (the victim's ID), you might inadvertently change their email address to yours.
Once the email is changed, you can click "Forgot Password".
The reset link goes to your email.
That is a full Account Takeover (ATO).
This is usually a Critical severity bug. We are talking thousands of dollars in bounties.
🛡️ Bypassing Defenses: When It's Not That Easy
Developers aren't always completely asleep at the wheel.
Sometimes they try to obscure the IDs.
They might use UUIDs (Universally Unique Identifiers).
A UUID looks like this: 123e4567-e89b-12d3-a456-426614174000.
You can't just guess the next number. But that doesn't mean it's secure.
1. ID Leakage
Just because you can't guess the ID doesn't mean the app doesn't leak it elsewhere.
Check the source code. Check other API endpoints.
Sometimes, a call to /get-friends-list will return a JSON object containing the UUIDs of all your friends.
Grab one of those UUIDs. Plug it into the vulnerable endpoint.
If it works, you still have an IDOR.

2. HTTP Parameter Pollution
This is a sneaky trick.
Sometimes the application checks the first ID it sees but processes the second one.
Try sending this:
GET /api/messages?id=YOUR_ID&id=VICTIM_IDThe firewall might check YOUR_ID and say "Access Granted."
But the backend code might loop through the parameters and accidentally execute the query for VICTIM_ID.
3. Changing the Request Method
Developers often secure the obvious routes but forget the obscure ones.
If GET /users/100 is blocked, try these variations:
- POST /users/100
- PUT /users/100
- DELETE /users/100
Sometimes switching the verb bypasses the access control check entirely.
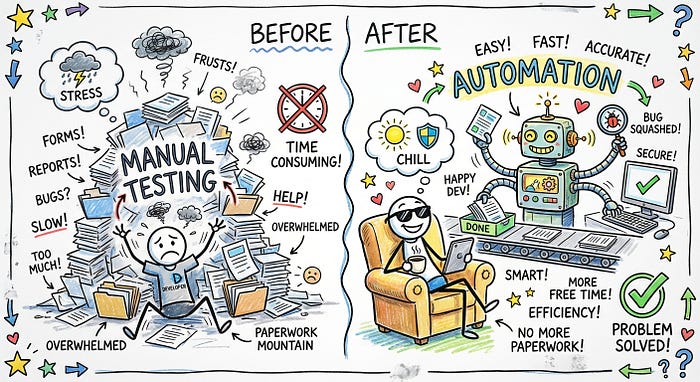
⚡ Automation: Work Smarter, Not Harder
Manually changing numbers is boring.
It's also slow.
To really scale your bug hunting, you need automation.
💡 Pro Tip: Never automate against a target without permission. You might bring down the server or get your IP banned.
Burp Suite Intruder
Send your request to Intruder.
Highlight the ID number.
Set the payload type to "Numbers".
Tell it to range from 1 to 1000.
Click "Start Attack".
Watch the responses. Look for differences in Content-Length or Status Code.
If 999 requests return "403 Forbidden" (Length: 500) and 1 request returns "200 OK" (Length: 2500)…
You just found the needle in the haystack.
AuthMatrix
This is a Burp Suite extension that is absolute gold.
It allows you to manage sessions for multiple users (e.g., User A, User B, and Admin).
You can tell it to run every request you find as every user.
It color-codes the results. If User A can access User B's data, it lights up red.
It saves hours of manual testing.
🐛 How to Fix It (The Developer Perspective)
If you are a developer, you are probably sweating right now.
How do you stop this?
The answer is Access Control.
Never trust the user input.
When a request comes in for /invoice/551, do not just query the database for invoice 551.
You must run a check:
- Who is the currently logged-in user? (Check the session).
- Does this user own invoice 551?
If the answer is no, return a 403 Forbidden.
Don't just hide the ID. Don't just obscure it.
Validate permissions on every single object reference.
🎯 Conclusion
IDORs are pervasive.
They are found in startups. They are found in Fortune 500 companies.
They are arguably the best bug for beginners to look for because they don't require complex coding knowledge.
They just require logic, curiosity, and a little bit of skepticism.
So next time you see a number in a URL, ask yourself the question:
"What happens if I change this?"
The answer might just pay your rent.
Happy Hacking! 💻🏴☠️
