North Korean state-sponsored threat actors have been actively targeting Linux users, particularly software developers, freelancers, and IT professionals, through complex social engineering, supply-chain compromises, and malware delivery.
This targeting has been carried out by groups like Lazarus (also known as HIDDEN COBRA) and others like DeceptiveDevelopment. Scammers posing as recruiters entice users with coding exams or job-related tasks that execute malicious code across Windows, macOS, and Linux are behind campaigns such as Operation Dream Job and Contagious Interview.
These attacks often result in the theft of credentials, the opening of backdoors, the draining of cryptocurrency wallets, and lateral movement. DPRK operations often use cross-platform tools, such as Linux ELF binaries, npm/PyPI supply-chain poisoning, and even eBPF-based techniques in advanced rootkits. However, Linux defenders can greatly lower the risk by using layered defenses that focus on identity verification, code hygiene, isolation, and proactive monitoring. Established threat intelligence on these campaigns and Linux security basics have led to the following best practices.
Vet Job Applicants Thoroughly
If your company is hiring developers or IT workers who work from home, make sure to check their identities very carefully. Instead of using company tools, use personal Signal (or Jitsi Meet) accounts to make live video calls.
Look closely at CVs for things like mismatched college degrees, generic or low-effort project profiles on GitHub, or inconsistent work histories. DPRK actors often use fake identities, stolen identities, deepfakes, and accomplice networks (like "laptop farms") to get past initial checks and get jobs or run code during "interviews."
Never Execute Unverified Code
Don't run binaries, scripts, Docker containers, or any code that comes from people you don't know, "recruiters," or GitHub repositories that you haven't checked out yet. DPRK campaigns often send out malware that looks like coding challenges, bug fixes, or interview projects. These campaigns often go after JavaScript and Python developers who work in crypto or blockchain.
Sandbox Unknown Code
If you need to test new software or a project that seems fishy, do it in a Virtual Machine (VM) that isn't connected to the internet. Tools like VirtualBox, KVM, or GNOME Boxes make this easy and stop any malware from calling home or getting into your host system.
Verify Signatures
Install software only from official, trusted sources, like your distribution's package manager. Before downloading source code or installing packages, always check the GPG signatures and checksums.
Audit Third-Party Packages
Check your installed npm, pip, Cargo, or other language-specific packages for malicious dependencies on a regular basis. Use tools like npm audit, pip-audit, or dependency-check, and think about locking dependency versions or using tools that look for known supply-chain compromises. DPRK actors have poisoned open-source ecosystems many times.
Restrict Downloads
Block unknown or dangerous file types (.exe, .msi, .scr, suspicious scripts like .sh/.py from untrusted sources) in your web browser and at the network perimeter. Browser extensions or proxy rules can enforce this.
Monitor eBPF Usage
Use auditing tools to monitor eBPF load/unload events. Tools like kprobes or tracepoints (via bpftrace, sysdig, or auditd rules) can detect unauthorized eBPF program injection, which advanced Linux rootkits sometimes employ for stealth.
Enable Mandatory Access Control (MAC)
Use SELinux or AppArmor in enforced mode. These confine processes even if they gain root privileges, limiting the blast radius of a successful compromise.
Keep Kernels Patched
Apply security patches immediately. Tools like KernelCare enable live kernel patching without rebooting, covering major enterprise distributions and drastically reducing the window of exposure to kernel vulnerabilities.
Block Known Indicators of Compromise (IOCs)
Actively block IP addresses linked to DPRK campaigns, particularly those identified in threat intelligence reports (e.g., the entire 175.45.176.0/22 range, which is the primary public IP block assigned to North Korea's Star JV network in Pyongyang).
Use Strict Firewalls
Implement strict iptables, nftables, or firewalld rules that whitelist only required outgoing connections. Deny-by-default is the safest posture.
Scan for Unauthorized Backdoors
Monitor for unexpected SOCKS5 proxies or strange network traffic, as DPRK malware often installs these to enable command-and-control and lateral movement. Tools like netstat, ss, lsof, or full network monitoring solutions help spot anomalies.
Additional practical tips include enabling automatic security updates where possible, using full-disk encryption (LUKS), enforcing strong SSH key-only authentication (disable password logins), running services with minimal privileges via systemd, and regularly reviewing logs with tools like journalctl or Fail2Ban. For high-risk environments, consider running browsers in containers (Firejail or Bubblewrap) and avoiding root privileges for daily tasks.
Dedicated Tools for Enhanced Protection
- Little Snitch for Linux (github.com/obdev/littlesnitch-linux) provides open-source eBPF components of the popular macOS outbound firewall, adapted for Linux. It offers per-application network monitoring and control, allowing you to see exactly which processes are attempting outbound connections and block suspicious ones in real time. This is particularly valuable against backdoors and data exfiltration attempts common in DPRK campaigns, as it adds transparency and defense-in-depth at the application layer. The full product includes a user-friendly interface, while the GitHub repo contains the core eBPF programs, shared Rust crates, and web UI under GPL-2.0.
- The SELinux Project (github.com/selinuxproject) is the official upstream GitHub organization for Security-Enhanced Linux. It hosts the core tools, libraries, reference policy, and related resources for this powerful Mandatory Access Control (MAC) framework. Enabling SELinux in enforcing mode (or its counterpart AppArmor) is one of the most effective ways to limit what even a root-compromised process can do — directly countering privilege-escalation tactics seen in advanced persistent threats.
- FleetDM (fleetdm.com) is an open-source device management and security platform built around osquery that provides comprehensive visibility, monitoring, vulnerability management, and compliance enforcement across Linux endpoints. It enables real-time and scheduled SQL-based queries to audit system configurations, track software inventories, detect unpatched vulnerabilities or misconfigurations, and identify unauthorized changes or suspicious activity — directly aiding in the discovery of backdoors, supply-chain compromises, and anomalous behaviors commonly associated with DPRK-linked campaigns. Its transparent, GitOps-friendly design (with the core project hosted at github.com/fleetdm/fleet) makes it ideal for scaling security controls, enforcing policies, and maintaining a strong security posture in Linux environments without relying on proprietary tools.
- Firejail (github.com/netblue30/firejail) is a lightweight, open-source sandboxing tool for Linux that uses Linux namespaces, seccomp-bpf filters, and capabilities to create tightly restricted execution environments for applications. By confining programs — especially web browsers, media players, development tools, or any downloaded binaries/scripts, Firejail limits their access to the filesystem, network, and system calls, significantly reducing the blast radius if the application is compromised by malicious code. This makes it highly effective against DPRK-style threats where attackers trick users into running unverified executables, npm packages, or "interview" scripts. It ships with hundreds of pre-configured security profiles, integrates easily into daily workflows, and serves as excellent defense-in-depth alongside SELinux/AppArmor, VMs, or strict firewalls. While it is not a complete replacement for full isolation solutions (and, as a setuid binary, has faced some past privilege-escalation CVEs), it remains a practical, low-overhead way to safely test or run potentially risky software on desktop Linux systems.
Hardened Linux Distributions for Maximum Security
For users seeking even stronger baseline protection, consider specialized distributions designed with compartmentalization, anonymity, and attack resistance in mind:
- Qubes OS emphasizes security through isolation. It uses Xen-based virtualization to run applications and networks in separate "qubes" (lightweight VMs), so a compromise in one area is contained and cannot easily spread to the rest of the system.
- Tails OS is a live, amnesic operating system that routes all traffic through Tor and leaves no traces on the host machine after shutdown — ideal for sensitive work or evading surveillance.
- Whonix OS provides strong anonymity by running in two VM components (a Tor gateway and a workstation), forcing all network traffic through Tor while isolating the user environment.
- Parrot OS is a Debian-based security-focused distribution that includes pentesting tools, forensic capabilities, and privacy features such as Anonsurf (automatic Tor routing), making it suitable for both defensive and offensive security workflows.
EDR For Linux
There isn't a single "best" EDR (Endpoint Detection and Response) for Linux — it depends on your environment (servers, containers/K8s, cloud workloads, or desktops), priorities (telemetry depth, agent stability/performance, prevention vs. detection, cost, integration), and whether you want commercial, managed, or open-source.
Linux EDR is trickier than Windows because of diverse kernels/distros, headless servers, and containerized setups, so agent compatibility and lightweight design matter a lot.
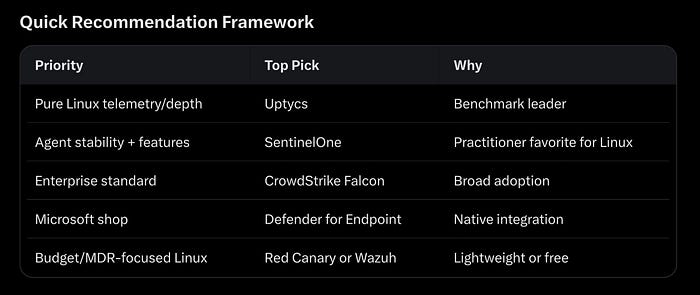
For most Linux-focused use cases in 2026, start with SentinelOne or Uptycs — they lead in practical Linux strengths. Run PoCs in your actual environment (test kernel compatibility, performance overhead, and false positives).
If budget or self-management is key:
- Wazuh — Most mature open-source EDR-like tool (FIM, log analysis, active response, vulnerability detection). Cross-platform and widely used on Linux.
- Elastic Agent (with Elastic Security) or osquery (base for many solutions like Uptycs).
- OpenEDR (from Comodo) — Full open-source EDR with MITRE ATT&CK mapping.
Factors like cost, support, and existing stack (e.g., SIEM) will decide the best solution.
Key Takeaways
By combining these practices, tools, and — if appropriate — distributions, Linux users and organizations can build robust defenses against DPRK-linked threats.
Stay vigilant, keep systems updated, and treat every unsolicited "job opportunity" or code sample with extreme skepticism. Security is an ongoing process, but these layered controls dramatically raise the bar for even the most determined nation-state actors.


