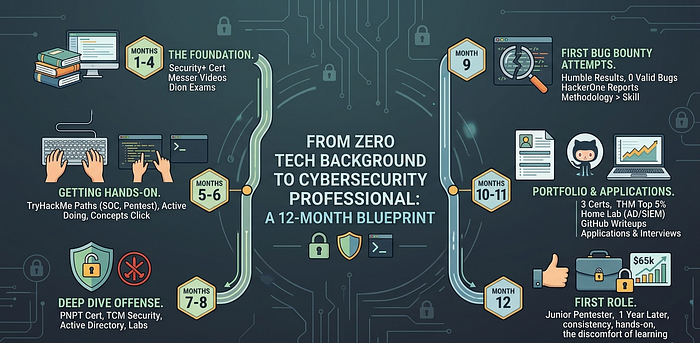
🗓️ Where I Started
Ten months ago I was not a tech person.
My background was in retail management. I knew how to use Excel, send emails, and troubleshoot why the printer wasn't working. That was the full extent of it. No CS degree, no programming experience, no idea what a subnet was.
What I did have was a specific reason to care about security. Our store had a social engineering incident where an attacker called pretending to be IT support and walked an employee through giving away credentials. Watching that happen and realizing nobody in the room knew how to stop it or respond to it properly, that was the moment.
I decided to spend 12 months finding out if I could actually do this. Here's exactly what I did, what worked, and what I'd do differently.
📋 The Honest Overview
Before the breakdown: this took real time. I averaged about two hours on weekdays and four to five hours on weekends. If you have less time available, this same path works but the timeline stretches. If you have more, it compresses.
It also cost money, but not a lot. Total spend across 12 months was under $800, which I'll break down as we go.
🧱 Months 1 and 2: Building the Foundation
- The biggest mistake beginners make is jumping straight into hacking content without understanding how networks and operating systems actually work. I made this mistake for the first two weeks before someone on Reddit talked me out of it.
What I actually learned first:
- Networking fundamentals. How data moves across a network, what IP addresses and ports are, how DNS works, what happens when you type a URL into a browser. This sounds boring. It is not boring once you realize every attack technique maps back to these concepts.
- Linux basics. Most security tools run on Linux. Most servers run Linux. Being comfortable at the command line is non-negotiable. I spent three weeks just getting comfortable with navigation, file permissions, processes, and basic scripting.
- How the web works. HTTP requests and responses, cookies and sessions, how authentication works at a protocol level, what APIs are. Again, foundational and not optional.
Resources that worked:
- Professor Messer's free CompTIA Network+ course covered networking better than anything else I found, and it's free on YouTube. For Linux I used OverTheWire Bandit, which teaches command line through a wargame. For web fundamentals, the MDN Web Docs and a few targeted YouTube searches.
Cost this period: $0
📚 Months 3 and 4: First Certification
- I targeted CompTIA Security+ for two reasons. First, it's genuinely required or preferred on a large percentage of entry-level security job listings. Second, it forced me to build broad foundational knowledge across domains I would have skipped otherwise.
- I want to be clear about what Security+ is and isn't. It's a knowledge cert, not a practical one. Passing it meant I could explain concepts, not necessarily execute them. But it opened doors and gave me a framework for everything that came after.
How I studied:
- Professor Messer's Security+ course again, free on YouTube. Jason Dion's practice exams on Udemy, which I got during a sale for $15. I read each question I got wrong three times and made sure I understood not just the right answer but why the other options were wrong.
- Studied for six weeks, passed on the first attempt.
- Cost this period: $370 for the exam voucher, $15 for practice exams.
💻 Months 5 and 6: Getting Hands-On
- This is where I stopped consuming and started doing. It was uncomfortable and I wanted to go back to tutorials constantly. I didn't, and this period was probably the most valuable of the whole year.
TryHackMe:
- I started with the "Pre-Security" path, which assumed no prior knowledge, then moved to "SOC Level 1" and "Jr Penetration Tester" paths. The key was doing every room without skipping, including the ones that felt too basic.
- TryHackMe costs about $14 a month for the premium tier which gives access to all rooms. Worth every dollar as a learning platform. I spent two full months here almost exclusively.
What clicked during this period:
- Concepts I had memorized for Security+ suddenly made sense when I was actually exploiting them. SQL injection stopped being a definition I'd memorized and became something I understood mechanically because I had executed it. Privilege escalation stopped being a phrase and became a specific sequence of steps I had personally walked through.
Cost this period: $28 for TryHackMe premium.
⚔️ Months 7 and 8: Going Deeper on Offense
- By month seven I had a clear direction: I wanted to do penetration testing. Not every career-changer ends up here. Some go toward SOC work, cloud security, or GRC. But for me the offensive side was what kept me engaged, so I followed that.
The PNPT certification:
- TCM Security's Practical Network Penetration Tester certification is the most beginner-accessible practical cert in offensive security. Unlike OSCP it doesn't require years of experience to approach. The course material is genuinely excellent, the exam is a real penetration test against a small network, and the report you write becomes a portfolio piece.
- I spent two months working through the course material and doing practice labs before attempting the exam.
Active Directory:
- This was the turning point in my technical skill level. Understanding Active Directory attacks, specifically how Kerberoasting, Pass-the-Hash, and BloodHound-based enumeration work, is what separates someone who can hack isolated boxes from someone who can think about real enterprise environments.
- TCM's "Practical Ethical Hacking" course covers AD thoroughly. I also spent a lot of time in TryHackMe's AD rooms and set up my own small AD lab using two Windows VMs.
Cost this period: $30 for TCM Security's course bundle on sale.
🐛 Month 9: First Bug Bounty Attempts
- Before applying for jobs I wanted real-world proof of skill. Bug bounty seemed like the path.
- I'll be honest about my results: in month nine I found zero valid bugs. I found a lot of things I thought were bugs that turned out to be intended behavior or duplicates. This was humbling and also extremely educational.
What I learned from failing at bug bounty:
- Reading disclosed reports on HackerOne's Hacktivity was more valuable than any tutorial. Seeing exactly how other researchers found real vulnerabilities, what methodology they followed, what they looked for and where, compressed months of learning into weeks.
- I also learned that the difference between a bug bounty beginner and someone making real money is usually methodology and scope selection, not raw technical skill. The technical bar for many medium-severity bugs is not that high. The discipline to systematically cover all the attack surface is where most people fall short.
Cost this period: $0
📝 Months 10 and 11: Portfolio and Applications
By month ten I had:
- CompTIA Security+ certification
- PNPT certification
- A TryHackMe profile in the top 5% of users
- A home lab running an AD environment and a SIEM
- A GitHub with a few scripts and writeups
- Two completed HackTheBox machines with published writeups
I started applying at month ten. I applied to 34 positions over six weeks. I got eight responses, five interviews, and two offers.
What I think made the difference:
- Every application I sent linked to my TryHackMe profile, my GitHub, and a specific writeup relevant to the role. My cover letter was always three paragraphs: why this company, one specific thing I'd done that was relevant, a one-sentence ask.
- For roles that asked for experience I didn't have, I was upfront rather than stretching the truth. "I don't have professional experience with X, but I've built and worked with Y which is related, and here's what I learned" reads better than a resume that exaggerates and then can't back it up in an interview.
The interviews:
- Technical questions were mostly scenario-based. "Walk me through how you'd investigate a suspected phishing email." "You find an open S3 bucket during an assessment. What do you do?" The TryHackMe and lab work meant I had real processes to describe rather than theoretical answers.
- One interviewer asked me to explain the difference between a vulnerability and an exploit without using either word in the definition. I still think about that question. I got the job.
🎯 Month 12: First Role
- I accepted a junior penetration tester position at a regional security consultancy. Base salary was $65,000. Not the highest paying offer I received but the team was strong and the engagement variety was exactly what I wanted for continued growth.
- On my first day I was genuinely nervous. Week one was mostly onboarding, tooling setup, and shadowing senior testers. By week three I was contributing to an assessment under supervision. By month two I had led a web application assessment with a senior tester reviewing my work.
- The skills transferred. The lab time was not wasted. The things I learned from failing at bug bounty showed up immediately in real engagement methodology.
💡 What I'd Do Differently
- A few things I'd change if I were starting over:
- Start with Linux more aggressively. I underinvested here initially and paid for it in every lab and every tool installation.
- Do TryHackMe before the Security+ exam, not after. The hands-on context would have made the cert content land much better.
- Start writing publicly earlier. Blog posts, writeups, anything. The discipline of explaining what you're learning out loud accelerates the learning itself, and the artifact is valuable for job applications.
Spend less time on Reddit threads debating which cert to get and more time just doing the thing. Every week spent researching the optimal path is a week not spent walking any path.
🏁 The Point of All This
- Twelve months is not a magic number. Some people move faster, some slower. The point is that the gap between "zero tech background" and "working in cybersecurity" is crossable.
- It requires consistency more than talent. Hands-on practice more than content consumption. And tolerating the discomfort of not knowing things long enough to actually learn them.
- The field needs people who understand how organizations work, how humans make decisions, how risk is communicated, and how teams operate under pressure. Those things don't come from a CS degree. They come from having done other things first.
- Your background is not a liability. It just doesn't feel like an asset yet. 🔐