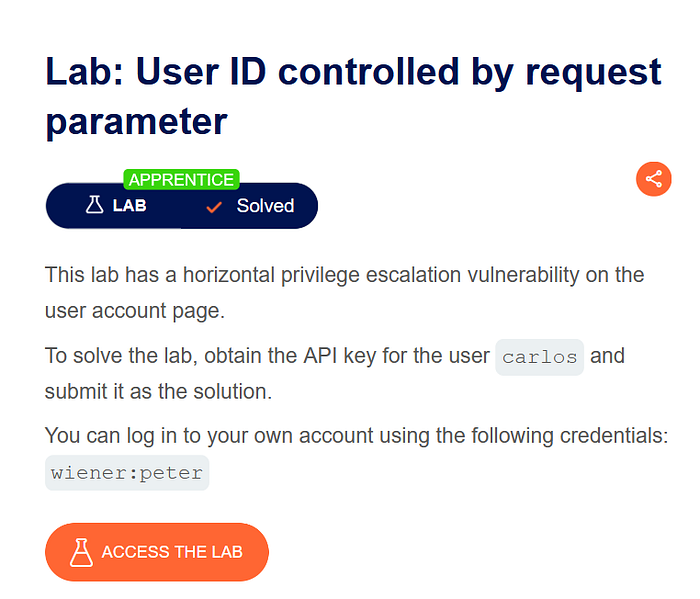
User ID control issues are a classic example of Broken Access Control, where an application trusts user-supplied input too much. In these labs, we explore how changing or discovering a user ID can give access to another user's sensitive data.
Understand how modifying a request parameter can allow unauthorised access to another user's account.
Steps Performed
Logged in using valid credentials:
- Username: wiener
- Password: peter
Opened Burp Suite and intercepted the request while visiting the account page.
Observed the following request:
GET /my-account?id=wiener
The application directly used the id parameter to identify the user.
Modified the request parameter from:
id=wiener
to:
id=carlos
Sent the modified request.
The server responded with Carlos's account details, including the API key.
Submitted the API key to complete the lab.
Result
The lab was successfully solved because the application did not verify whether the logged-in user was authorised to access Carlos's data.
Lab 6: User ID Controlled by Request Parameter (With Unpredictable User IDs)
Lab Objective
Exploit the same vulnerability when user IDs are unpredictable (GUIDs) instead of simple usernames.

Steps Performed
Logged in using valid credentials:
- Username: wiener
- Password: peter
Navigated to the account page and noticed the user ID was a GUID, for example:
GET /my-account?id=8a9f1c2e-xxxx-xxxx-xxxx
Guessing another user's GUID directly was difficult and impractical.
Explored the blog/posts section of the application.
Opened posts written by Carlos.
Observed that Carlos's user ID (GUID) was exposed in the URL when viewing his posts.
Copied Carlos's user ID from the URL.
Replaced the GUID in the account request:
GET /my-account?id=<carlos_guid>
Sent the request using Burp Suite.
Gained access to Carlos's account details, including the API key.
Submitted the API key to solve the lab.
Result
The lab was solved by indirectly discovering the user ID from publicly accessible content.
Conclusion
Both Lab 5 and Lab 6 demonstrate how improper access control can lead to serious security issues. In Lab 5, the vulnerability was straightforward due to predictable user IDs. In Lab 6, even though the IDs were unpredictable, the application still failed because it leaked user identifiers through public content.
These labs clearly show that security does not depend on obscurity. Strong access control must always be enforced on the server side, regardless of how complex or random the user identifiers appear.