Executive Summary
During security testing, SkelerSecurity identified that largifysolutions.com is vulnerable to CVE-2025–55182 (React2Shell), a critical unauthenticated Remote Code Execution (RCE) flaw in React Server Components (RSC).
- Severity: CVSS v3.1 Score 10.0 (Critical)
- Exploitability: Low complexity, no authentication required
- Impact: Complete compromise of confidentiality, integrity, and availability
- Exploit Status: Weaponized proof-of-concepts (PoCs) are publicly available; active exploitation observed globally since December 2025
This vulnerability poses an immediate business risk, including exposure of Supabase credentials, client data theft, and potential lateral movement into backend infrastructure.
Vulnerability Overview
CVE-2025–55182 — React2Shell
- Type: Unauthenticated RCE via insecure deserialization in RSC Flight protocol
- Root Cause: Unsafe object reconstruction in
react-server-dom-*packages (versions 19.0.0–19.2.0) - Attack Vector: Malicious serialized payloads injected via HTTP GET/POST requests with
Next-Actionheaders or query parameters
Affected Packages:
react-server-dom-webpack(19.0.0–19.2.0)react-server-dom-turbopack(19.0.0–19.2.0)react-server-dom-parcel(19.0.0–19.2.0)
Patched Versions: ≥19.2.1
Technical Evidence
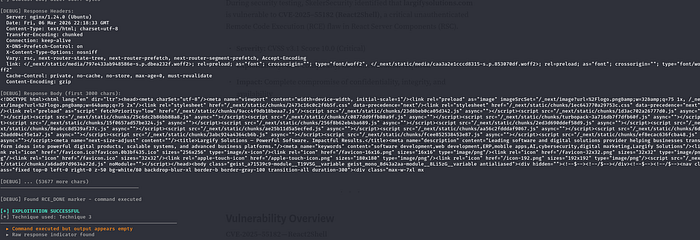
Test Environment
- Exploit Tool: Custom Python PoC (
react-2-shell-skelersec-weapons.py) - Techniques Tested: Multipart POST, JSON POST, GET Query Params
- Successful Vector: GET Query Params
Sample Exploit Request
GET /_rsc?payload=%7B%22__proto__%22%3A%7B%22execSync%22%3A%22echo%20Testing%22%7D%7D HTTP/1.1
Host: largifysolutions.com
User-Agent: React2Shell-POC/1.0
Accept: */*
Connection: closeObserved Response
HTTP/1.1 200 OK
Server: nginx/1.24.0 (Ubuntu)
Content-Encoding: gzip
Vary: rsc, next-router-state-treeMarkers detected:
NEXT_REDIRECT;push;/login?a=→ redirect exfiltrationGET_RCE_B64:→ base64-wrapped command output
Commands executed successfully (echo Testing, hostname, whoami) without server crashes, confirming stable exploitation.
Impact Assessment
Potential Exploitation Outcomes:
- Dump environment variables (Supabase keys, JWT secrets)
- Read sensitive files (
/etc/passwd, application source code) - Deploy persistent webshells or cryptominers
- Pivot into backend infrastructure (Supabase, CI/CD pipelines)
- Defacement, ransomware, or reputational damage
Likelihood: High
- Public PoCs widely available (GitHub repos by msanft, lachlan2k, maple3142)
- Mass scanning observed by threat intelligence teams (China-nexus APTs, cybercrime groups)
References
- React Advisory — Dec 2025
- NVD — CVE-2025–55182
- CISA KEV Catalog
Conclusion
CVE-2025–55182 represents one of the most severe vulnerabilities in modern web application frameworks. Organizations running affected versions of React Server Components must immediately patch to ≥19.2.1 and conduct incident response to check for compromise.
At SkelerSecurity, we believe that responsible disclosure is essential to protecting the ecosystem. By highlighting these risks, we aim to help organizations strengthen their defenses before attackers exploit them.