Let me begin by outlining the current digital environment…
In today's interconnected digital world, the boundaries within which organisations used to operate are no longer well defined. Employees access the organization's network from home networks, airports, and coffee shops. Applications are hosted in public and private clouds. Data is exchanged between servers in the organization's premises, SaaS services, and mobile devices. Now, pause for a moment and think: If everything is connected and accessible from anywhere, can we really assume that anything inside the network is automatically safe?
This paradigm shift in the way businesses are conducted has rendered the traditional security model obsolete. For so long, the concept of cybersecurity was based on the notion of a robust perimeter: a firewall must be built, the perimeter secured, and users trusted once they were inside the network. However, the nature of contemporary cyberattacks has shown that once hackers have penetrated the perimeter, they can move about freely, accessing critical systems without much hindrance. This has led to the adoption of a more intelligent and prudent model known as Zero Trust Architecture.
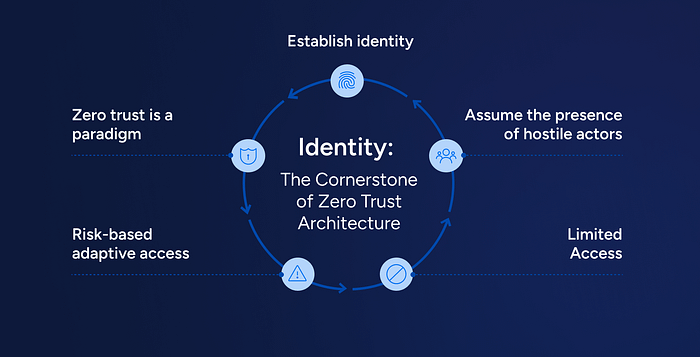
Zero Trust Architecture is a cybersecurity approach that is based on the "never trust, always verify" paradigm. This approach questions the conventional wisdom that says that traffic within a network is trustworthy and proposes that all access requests, whether they come from inside or outside the network, are potentially malicious. In this approach, trust is not presumed based on geography. Rather, trust has to be constantly earned.

Why Traditional Security Is No Longer Enough
To appreciate the value of Zero Trust, let's take a look at how security was done in the past. In the traditional setup, once a user successfully logged in, they were usually given unlimited access to the network. It was as if they had a master key to get into the building. Once inside, many doors were open to them. But what if the master key was stolen? What if a trusted device were infected with malware?
Cybercriminals have become sophisticated in their methods, using phishing, credential attacks, ransomware, and insider attacks. A single compromised account can result in massive data breaches. In fact, many of the biggest security breaches have occurred not because the hackers breached fortified firewalls, but because they exploited trusted credentials. Zero Trust fixes this vulnerability by eliminating the concept of implicit trust. Even if a user has successfully logged in, they are not automatically given unlimited access. Every request for access to a resource is assessed in real-time.
The system asks questions like:
Is this really the genuine user? Is the device secure and compliant? Is the login location unusual? Is the activity consistent with previous behaviour?
If anything looks fishy, access is blocked or restricted.
Let's Break Down the Core Ideas Behind Zero Trust
Zero Trust is not a product or a tool but an architectural approach that is based on sound principles. Let's dive deeper into these principles.
1. Verify explicitly
Each access request has to be authenticated and authorised based on all available information. This includes identity, device health, IP address, geographic location, and even the time of access. Tools such as Multi-Factor Authentication (MFA), biometric authentication, and adaptive access enable this principle. Rather than using a password alone, multiple levels of authentication are required before granting access.
2. Least Privilege Access
Zero Trust also promotes the idea of providing users the least amount of access required to complete their work. For instance, a finance department employee should not have access to software development servers. By doing so, the damage from a breach is limited. If an attacker takes over one account, their scope is also limited.
3. Assume Breach
The Zero Trust approach assumes that attackers are already inside the system rather than thinking that the system is secure. This approach promotes continuous monitoring, segmentation, and quick detection of anomalies. By planning for a possible breach, the damage is limited.
Inside Zero Trust: The Technologies That Make It Work
The Zero Trust Architecture combines various technologies and security processes into a single system. Each element is essential to the process of implementing continuous verification and protection.
1. Identity and Access Management (IAM)
The IAM solution is responsible for allowing only verified users to access certain resources. Effective identity management is the foundation of the Zero Trust Architecture.
2. Multi-Factor Authentication (MFA)
MFAisa process that verifies users by requiring them to provide two or more different authentication factors, such as a password and a verification code or biometric scan, thereby making it difficult for attackers to gain unauthorised access.
3. Micro-Segmentation
The Zero Trust Architecture breaks down the infrastructure into smaller, separate segments. Even if an attacker gains access to one segment, they won't be able to easily access other segments.
4. Continuous Monitoring and Analytics
The security solution continuously monitors user activity and network traffic. Advanced analytics and AI capabilities identify unusual patterns that may be indicative of threats.
5. Encryption Everywhere
The Zero Trust Architecture encrypts data both in transit and at rest. This means that even if the data is intercepted, it will be unintelligible to attackers.

Why ZeroTrust Is Worth the Move
You may be wondering if Zero Trust actually makes a difference. The answer is yes, and in many ways that can be measured.
Companies that implement Zero Trust typically see:
Less risk of large-scale data breaches Better protection against insider threats Better visibility into network traffic Improved compliance with data protection regulations Improved security for remote and hybrid work environments
The attack surface is significantly reduced by continuously verifying access, and it also provides resilience, which ensures that if one layer fails, others still work.
Challenges in Zero Trust Implementation
Although the benefits of Zero Trust are clear, the adoption of this technology is not immediate. There are several steps that need to be taken by businesses to adopt Zero Trust. First, they need to assess and categorize their resources, as well as update old systems that may not be compatible with the latest authentication techniques. There could also be some pushback from employees who may find the extra authentication steps to be a hindrance. This is where the latest Zero Trust technology can help by using adaptive authentication, which is more stringent as the risk increases.
Future of Cybersecurity with Zero Trust
With the pace of digital transformation accelerating and cloud adoption rising, the future of cybersecurity is increasingly defined by Zero Trust Architecture. Governments, businesses, and tech companies around the world are turning to Zero Trust models to tackle the ever-changing nature of cyber threats.
Now, consider this final question: In a world where cyber threats are changing every day, is it better to trust or to check? Zero Trust Architecture is a proactive, intelligent, and adaptive way of thinking about security. It doesn't depend on outdated models or traditional perimeter security. Instead, it is a philosophy of continuous validation, secure access, and constant monitoring. At the end of the day, Zero Trust is not about distrust; it's about smart security. It means that every access, every user, and every system is justified and protected. And in today's digital world, it's no longer a choice; it's a necessity.
This article was authored by Tharusi Manchanayake
