1. What it is (very simple definition)
Authentication means proving who you are to a website or app.
👉 Authentication vulnerabilities happen when a website fails to correctly verify a user's identity, allowing attackers to log in as someone else.
In short:
The app trusts the wrong person.
2. Why it exists (what problem it was created to solve)
Websites needed a way to:
- Know who is logged in
- Protect private data
- Allow different users to see different things
So authentication was created to answer one simple question:
"Are you really who you claim to be?"
To solve this, apps use:
- Username + password
- OTPs
- Tokens
- Sessions
- Cookies
3. How it works (browser → server, step by step)
Let's walk through a normal login flow.
Step-by-step flow
- You open the login page
- Browser loads
/login
2. You enter credentials
- Username + password
- Click "Login."
3. Browser sends a request
POST /login
username=binaryshield
password=Password@1234. Server verifies
- Is the username real?
- Does the password match?
- Is the account active?
5. Server creates a session
- Generates a random session ID
- Stores it server-side
6. The server sends session cookie
Set-Cookie: sessionid=abc123; HttpOnly7. Browser stores the cookie.
- Automatically sends it on every request
8. Server trusts the cookie
- "This request is from BinaryShield."
🔑 Authentication is done once, then remembered via cookies/tokens.
4. Two simple examples (easy to imagine)
Example 1: House key 🏠
- Your key = password
- Door lock = authentication logic
- If the lock opens for any key → vulnerability
Example 2: College ID card 🎓
- The securitySecurity guard checks ID
- If guard never checks photo, anyone can enter
- That's broken authentication
5. Real-world example (modern app or API)
Example: Login API (mobile app/web)
POST /api/login
{
"email": "user@gmail.com",
"password": "password123"
}If the server:
- Accepts weak passwords
- Doesn't limit login attempts
- Reuses tokens
- Trusts client-side values
➡️ Authentication vulnerability exists
Modern failures often happen in:
- JWT tokens
- OAuth logins
- Password reset flows
- OTP verification APIs
6. What can go wrong (misconfigurations)
Common authentication mistakes:
🚨 Password issues
- Weak passwords allowed
- Default passwords not removed
- No password rotation
🚨 Login flow issues
- No rate-limiting
- No account lockout
- No CAPTCHA
🚨 Session/token issues
- Predictable session IDs
- Tokens never expire
- Tokens not invalidated after logout
🚨 Reset & OTP issues
- OTP reusable
- OTP not tied to user
- Password reset token never expires
7. How attackers abuse it (basic → advanced)
🔰 Basic attacks
- Credential stuffing
- Reuse leaked passwords
- Brute force
- Try many passwords
- Default credentials
- admin/admin
⚙️ Intermediate attacks
- OTP brute force
- Password reset token reuse
- Session fixation
🔥 Advanced attacks
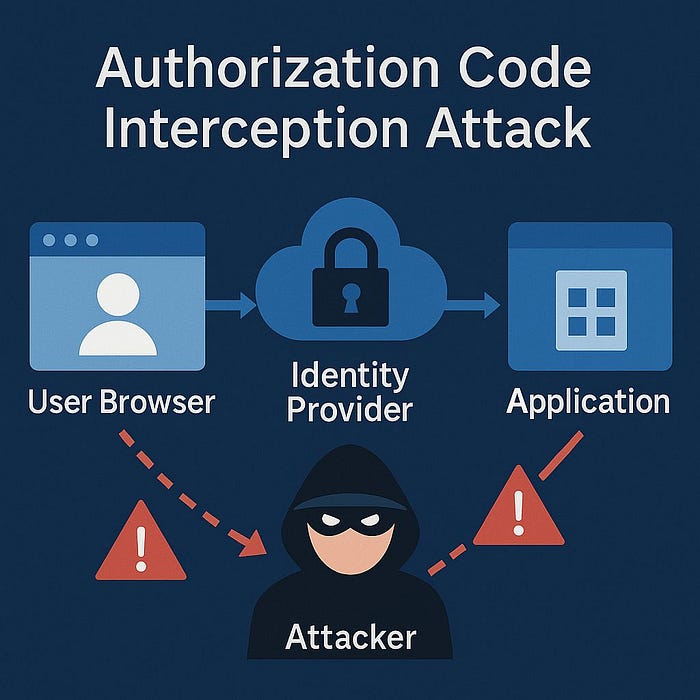
- JWT manipulation
- OAuth misbinding
- Token replay
- Authentication bypass via logic flaws
💡 Most real-world auth bugs are logic issues, not crypto failures.
8. Where and how to test it manually in VAPT
🎯 Where to test
Focus on:
/login/logout/register/forgot-password/reset-password/verify-otp- Token refresh endpoints
🛠️ How to test (manual mindset)
1️⃣ Login testing
- Try invalid passwords
- Observe error messages
- Check response differences
2️⃣ Rate-limit testing
- Multiple login attempts
- Same IP vs different IP
- Same user vs different users
3️⃣ Session handling
- Reuse old cookies
- Logout → reuse cookie
- Login as user A → replace cookie → user B
4️⃣ Password reset testing
- Reuse reset token
- Use token after password change
- Use token for another user
5️⃣ OTP testing
- Reuse OTP
- Change user ID but keep the OTP.
- Brute-force OTP length
🧠 Always ask:
"What is the server trusting that it shouldn't?"
9. Common beginner misunderstandings & false positives
❌ Misunderstanding 1
"Login page exists = vulnerability"
✅ Reality:
- The loginLogin page is normal
- Weak logic is the issue
❌ Misunderstanding 2
"401 Unauthorized = bug"
✅ Reality:
- 401 is expected for failed login
- Vulnerability = unexpected access
❌ Misunderstanding 3
"No CAPTCHA = high severity"
✅ Reality:
- No CAPTCHA alone ≠ vulnerability
- Combined with no rate-limit → real risk
❌ Misunderstanding 4
"JWT visible = insecure"
✅ Reality:
- JWTs are designed to be readable
- The issue is trusting manipulated JWTs
🧠 Key takeaways (think like a pentester)
- Authentication is about trust
- Vulnerabilities come from wrong assumptions
- Manual testing beats automation
- Logic flaws > tool findings
- Always validate impact, not just behavior
Useful Links:
learn = https://www.strongdm.com/blog/authentication-vulnerabilities
lab = https://portswigger.net/web-security/authentication
checklist = https://github.com/Az0x7/vulnerability-Checklist/blob/main/Authentication/authentication.md