📖 Table of Contents
- why is it vital to our business
- integretion whith soc process
- Legal Foundations for Admissible Evidence
- Case Study
💼 Why is it vital to our business?
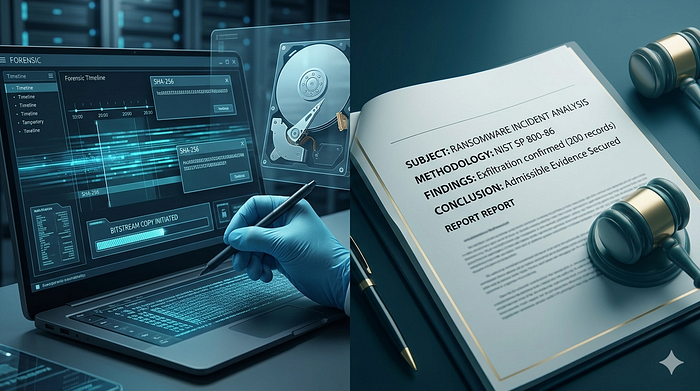
Integrating digital forensics into business processes transforms security from a cost center into a legal and reputational protection asset. ROI: Reduces financial losses by accelerating Root Cause Analysis (RCA) and facilitating the recovery of stolen assets or intellectual property. Compliance: Ensures the organization meets regulatory requirements (such as GDPR or ISO standards) during data breach management, guaranteeing that collected evidence is usable in judicial proceedings. 📌 Concrete Example: A mid-sized European company suffered a ransomware attack that also exfiltrated customer PII. Without a proper forensic investigation, they would have assumed the breach affected 10,000 records — leading to a potential €4M GDPR fine. By conducting a bitstream-level forensic analysis (preserving original evidence), they proved that only 200 records were actually exfiltrated. The forensic report, following NIST guidelines and Daubert standards, was accepted by the supervisory authority. Result: Fine reduced to €80,000 plus legal costs. Forensics saved the company over €3.9M.
🛡️ Integration with SOC Processes
Digital forensics does not operate in isolation; it is the final pillar of security operations: Alert Triage 🔴: Identification of suspicious activity. Incident Response 🛡️: Containment of the threat. Digital Forensics 🔎: Deep post-mortem analysis for legal purposes and future prevention. Key Performance Indicators (KPIs): MTTD: Mean Time to Detect MTTR: Mean Time to Respond MTTI: Mean Time to Investigate
⚖️ Legal Foundations for Admissible Evidence
To be admissible in court, digital evidence must meet specific legal standards: Frye Standard (1923): Requires that the scientific techniques used are "generally accepted" by the relevant scientific community. Forensic hashing (SHA-256) and write-blockers meet this threshold. Daubert Standard (1993): The judge acts as a "gatekeeper" — the method must be testable, peer-reviewed, and have a known error rate. A forensic examiner must document every step to satisfy Daubert. The Forensic Examiner as an Expert Witness: The examiner does not just present data; they interpret it under oath. They must be able to explain why a bitstream copy is identical to the original, how the chain of custody was maintained, and what the metadata means. A poorly documented investigation can be dismissed as "hearsay" or "unreliable opinion." Bitstream Copy vs. Logical Copy: Logical copy: Copies only visible files and folders (like Windows Explorer). Does NOT capture deleted files, unallocated space, or partition metadata. Not forensically sound. Bitstream copy (forensic image): A sector-by-sector replica of the entire storage device, including deleted files, slack space, and hidden partitions. Verified by cryptographic hash (SHA-256). This is the gold standard for court. Security Tip: Always use a write-blocker when acquiring a bitstream copy. Even booting a suspect drive can change MAC timestamps, potentially invalidating the evidence.
📋 Case Study
Insider Threat Investigation Background: A financial analyst was suspected of selling proprietary trading algorithms to a competitor. The only available evidence was the employee's company laptop, which had been used for three days after the alleged theft. Forensic Process (following NIST): Collection: A bitstream copy of the laptop's SSD was created using FTK Imager with a hardware write-blocker. SHA-256 hash recorded. Examination: Deleted file carving recovered 47 .xlsx files from unallocated space. Metadata analysis showed that these files had been created on a USB device (vendor ID traced to a specific brand). Analysis: Timeline reconstruction proved that the files were accessed at 2:00 AM — outside the employee's normal working hours. No corporate VPN log matched that time. Reporting: The forensic report included hash verification, chain of custody forms, and an expert declaration under Daubert standards. Technical Inconsistency Detected: The employee claimed the files were never copied to external media. However, USB device insertion events (Windows Event ID 2003, 2100) contradicted this. The vendor ID of the USB matched a device purchased by the employee's spouse. Case Conclusion: The investigation successfully identified the suspect through metadata analysis and detected technical inconsistencies (USB logs vs. employee statement). By following the NIST framework (Collection, Examination, Analysis, Reporting) and adhering to Daubert standards, we ensured an unassailable Chain of Custody. The suspect was terminated, and criminal charges were pursued. The forensic evidence was admitted in court without objection. This case proves that technical precision is the key to digital justice.