Introduction :
Business logic flaws are arguably some of the most fascinating vulnerabilities in the bug bounty landscape. Unlike standard injection flaws, they cannot be detected by automated scanners; they require a deep understanding of how an application's architecture and backend processes interact.
Modern SaaS platforms rely on complex billing systems and mechanisms like the "Dunning process" (a grace period granted when a payment fails). In this write-up, I will explain how I chained a simple API state manipulation with a grace period abuse to successfully upgrade a free account to the highest "Enterprise" tier — gaining full privileges — using a Virtual Credit Card (VCC) with a $0 balance.
The Reconnaissance :
The target was a SaaS application offering tiered subscription plans (Basic, Pro, Business, Enterprise). I started by proxying my traffic through Burp Suite while navigating my account settings on the free "Basic" plan.
I noticed the web application sending GET requests to fetch the user's license details. The response returned a text payload containing details like "license":"basic" and "is_trial":false.
This sparked a question: What happens if we try to manipulate this state?

The Attack Vector :
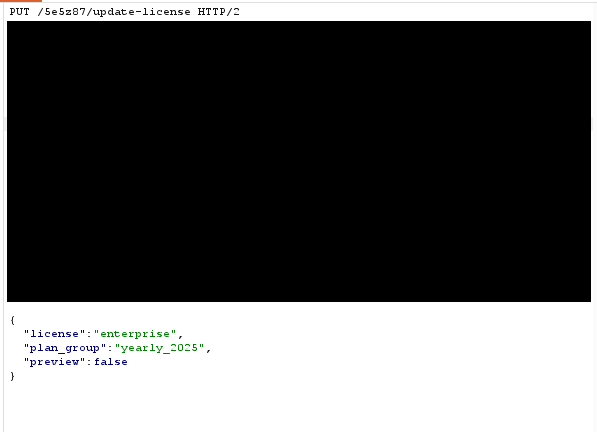
Step 1: Manipulating the API State : Instead of modifying the response (which would only result in a client-side UI spoof), I focused on the PUT request sent to the server when updating the plan.
I intercepted the request to the /api/update-license endpoint and manually altered the payload text to request the Enterprise plan by sending parameters like "license":"enterprise", "plan_group":"yearly_2025", and "preview":false.
The frontend immediately responded to this state change, displaying my plan as "Enterprise (Pending)." However, at this stage, the actual backend privileges remained "Basic" because no payment had been processed.
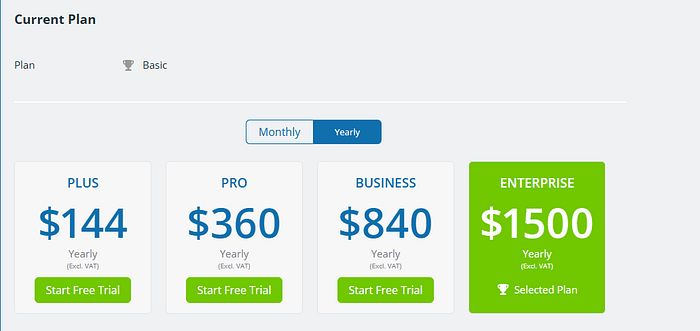
Step 2: The Grace Period Abuse : The server was now waiting for a valid payment method to finalize the upgrade. This is where I decided to test the backend logic: Does the server grant privileges before or after confirming a successful charge?
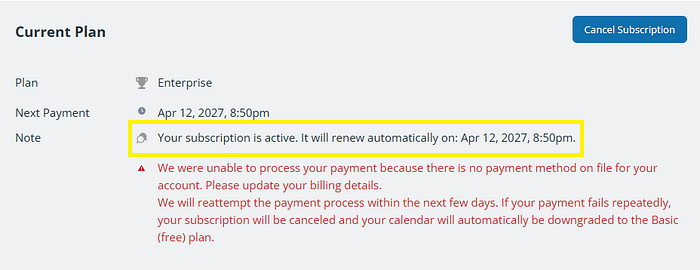
I generated a Virtual Credit Card (VCC) with a strict $0 limit and added it as my billing method. As expected, the payment authorization failed. The system displayed a glaring red warning stating that they were unable to process the payment and the subscription would be canceled if payment fails repeatedly.
However, the critical flaw was that the server — acting on its Dunning/Grace Period logic — temporarily activated the Enterprise plan to give me time to "fix" my payment issue. The backend handed over the keys to the castle before securing the funds.
The Impact (Proof of Concept) :
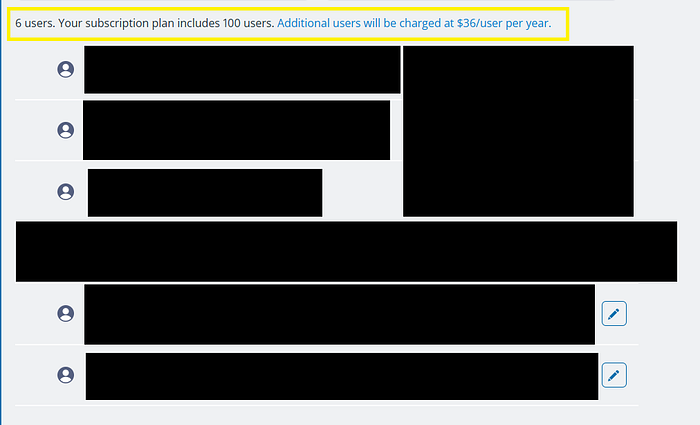
To definitively prove this was a Server-Side Privilege Escalation and not just a UI bug, I had to test the actual limits of the account.
The free Basic plan strictly enforced a maximum limit of 5 users. By exploiting this flaw, I navigated to the User Management section and successfully added 6 users.
Not only did the server accept the 6th user, but the UI also explicitly rendered a message pulled from the backend database stating: "Your subscription plan includes 100 users."
Furthermore, checking the account's storage limits revealed that the account was successfully granted the massive 1000 GB (1 TB) storage quota exclusive to the Enterprise tier, confirming the complete bypass of the free tier restrictions.

This confirmed that the backend database had been successfully overwritten. A malicious actor could easily automate this process, creating new accounts and cycling through empty VCCs to permanently bypass the paywall, indefinitely consuming the highest tier of server resources and features at zero cost.
Takeaways for Developers :
- Never Trust Client-Side Data: Any state or pricing data sent from the client must be strictly validated against the backend database before executing any critical actions.
- Strict Payment Validation: Do not grant premium privileges or expand hard limits during a payment grace period unless a successful initial charge (or authorization hold) has been verified. Grace periods should only apply to existing, previously paying customers, not new upgrades.