They will send you enough to frustrate you to unsubscribe YET the Unsubscribe link is also malicious… Not only this phishing email bypassed the spam filters BUT it also has a psychological catch that you have to fall for even if you are smart — this is creatively engineered and interesting … walk with me during it's analysis.
Fake unsubscribe mechanism the 2026 g.o.a.t:
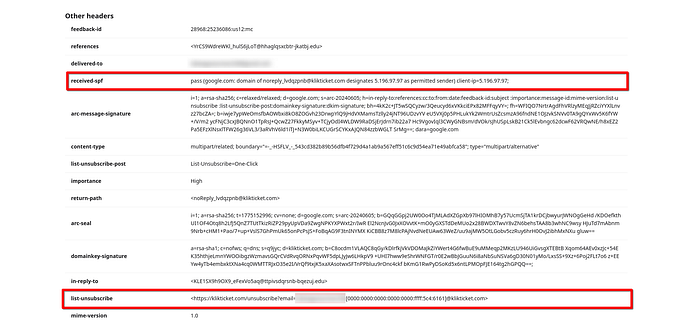
The unsubscribe links also point to the same malicious IP.
Clicking unsubscribe still contacts attacker infrastructure. Now i know that you know this but feel sorry to that frustrated HR or anyone non-technical — this is why we need to defend them!
Malicious infrastructure Embedded URL host
The phishing link points to:
http://[0000:0000:0000:0000:0000:ffff:5c4:6161]/...
This is an IPv4-mapped IPv6 form.
Equivalent IPv4:
5.196.97.97
This direct-IP usage is a strong phishing indicator:
- Avoids domain reputation controls
- Bypasses weak filters
- Hides destination identity
Primary phishing indicators:
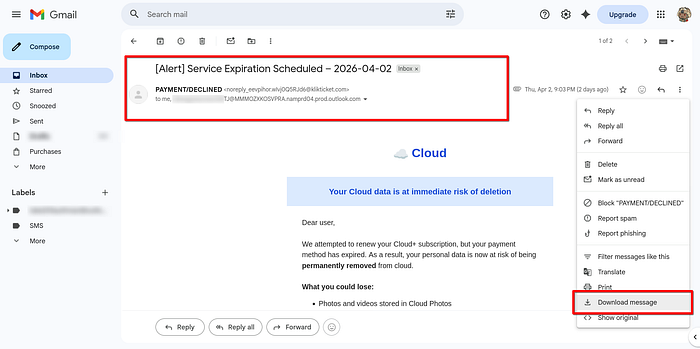
- Fake urgency language
- The body uses strong coercion:
"Your Cloud data is at immediate risk of deletion"
"Final Reminder"
"Update Payment & Secure My Data"
This is classic fear-based payment phishing EML.
No legitimate cloud provider threatens deletion through a generic email like this BUT they used to exist — anyone remembers that cloud elephant app , i lost it's name.
Question: If a legit email frustrates you enough, Do you:
(A) Unsubscribe
(B) Unsubscribe

Verdict:
High-confidence phishing email targeting payment urgency and cloud-account fear.
The EML combines:
- fake billing failure
- fake cloud data deletion threat
- obfuscated infrastructure
- forged sender trust signals
- hidden spam padding
The EML:
Now immediately after an online purchase, You receive an email — it has [Alert]: which would have been caught by the spam filters BUT it did NOT.
The Entity also uses modern phishing deliverability engineering which includes:
+ Authentication
+ Content obfuscation
+ Infrastructure camouflage.
The Strongest Bypass vectors:
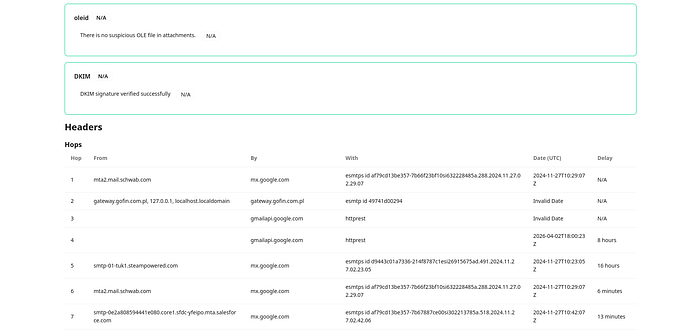
- SPF = pass
- DKIM = pass
- DMARC = pass
Header anomalies:
Suspicious HELO / Received chain
Claimed source:
ftnrvtxnycjltf.edu.pju
Fake relay history
Headers contain unrelated systems:
- Salesforce
- Charles Schwab
- Steam
That indicates header injection / fabricated relay chain.

We have a Sender impersonation mismatch, the Display name:
PAYMENT/DECLINED
Actual sender:
@klikticket.com">noreply_eevpihor…@klikticket.com
The sender domain is KlikTicket — unrelated to any cloud subscription provider.
That mismatch alone is highly suspicious… No SHIT, Sherlock !
" Authentication success only proves domain control, not legitimacy. "

Malicious infrastructure Embedded URL host
The phishing link points to:
http://[0000:0000:0000:0000:0000:ffff:5c4:6161]/...
This is an IPv4-mapped IPv6 form.
Equivalent IPv4:
5.196.97.97
This direct-IP usage is a strong phishing indicator because it:
- avoids domain reputation controls
- bypasses weak filters
- hides destination identity

We have Obfuscated link path:
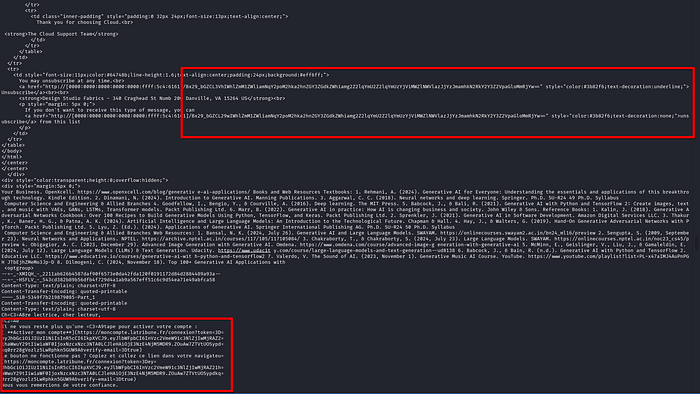
These are:
- Base64-like encoded
- binary after decode
- not human-readable
- likely tracking token / campaign identifier

I personally think they are Used to:
- individualize victims
- track clicks
- evade IOC matching
Hidden content stuffing:
The email contains large unrelated blocks:
- generative AI textbook content
- academic references
- unrelated French email fragments — basically HTML junk
This is content padding / Bayesian filter evasion.
Someone would do this to:
- lower spam score
- confuse scanners
- bypass heuristic engines
If i missed anything, the comments — i'm always active, you can drop me a feedback BUT these phishing EMLs are really getting out of hand especially now we have machine generated payloads. Think of it as now it's machine against machine Era — we need human intervention with God on our side!
Alright, i'm signing 0u7!
Cheers to ALL YOU !!!!
