TL;DR: The Blueprint for Success
🎯 Understand the Game: Bug bounties are legal hacking agreements where companies pay for valid security vulnerabilities. It is not "GTA with a hoodie."
📚 Read First: Start with "Real-World Bug Hunting" by Peter Yaworski to understand how actual vulnerabilities are found and reported.
🏋️ Practice Daily: Use labs like PortSwigger Web Security Academy to build muscle memory before touching live targets.
🧠 Master OWASP: The OWASP Top 10 is your bible. Understand these fundamental flaws inside and out.
🗺️ Recon is King: Follow Jason Haddix's "Bug Hunter's Methodology." Understanding the target's infrastructure is 80% of the battle.
📝 Report Effectively: A bug is only as valuable as your report. Learn to write clear, impactful remediation guides.
Introduction: The Reality Check
So, you want to learn bug bounties? The typical beginner's journey usually looks like this: Step 1, open 47 browser tabs. Step 2, panic. Step 3, read a Reddit thread that unhelpfully suggests you "just learn everything about everything."
This approach is a recipe for burnout. Bug bounty hunting isn't magic, and it certainly isn't the rapid-fire, green-text-scrolling hacking you see in movies. It is a disciplined, technical pursuit that requires a specific methodology.
Instead of wandering the desert of YouTube clickbait and dead blogs, this guide outlines the intelligent, structured path to becoming a successful hunter. We will move away from the "script kiddie" mentality and toward the mindset of a professional security researcher.
What Actually is a Bug Bounty?
Before we dive into the technicalities, let's clarify the objective. Bug bounty programs are initiatives where organizations — from tech giants like Google to financial institutions — pay ethical hackers to find vulnerabilities in their software.
Platforms act as the middlemen, connecting companies with hackers. The major players include:
- HackerOne: The largest platform with a massive variety of programs.
- Bugcrowd: Known for its crowd-sourced approach and triage services.
- Intigriti: A rapidly growing platform with a strong community focus.
- Synack: A more exclusive, vetted platform often used by enterprise clients.
The premise is simple: You sign up, you find a bug, you report it. If it's valid, you get paid. Payouts can range from $50 for a minor configuration issue to $50,000+ for a critical Remote Code Execution (RCE). However, the gap between "signing up" and "getting paid" is vast. Bridging that gap requires a solid foundation.

Phase 1: The Theoretical Foundation
Do not touch a live target yet. If you try to hack Facebook or Tesla without understanding what a vulnerability actually looks like, you are simply wasting your time and their bandwidth.
The Mandatory Reading
Forget the dry, academic textbooks that read like they were written by a compiler. The absolute best starting point is "Real-World Bug Hunting: A Field Guide to Web Hacking" by Peter Yaworski.
This book is a "cheat code" for beginners. Unlike general security books, Yaworski compiles actual, disclosed bug bounty reports. It doesn't just teach you the definition of Cross-Site Scripting (XSS); it shows you a real report where a hacker found XSS in a major application, how they exploited it, and how much they were paid.
💡 Key Insight: Reading real reports teaches you "Hacker Logic." You learn to see not just the code, but the logic errors and business flow bypasses that automated scanners miss.
The book groups bugs by category — Authentication, Logic Flaws, Injection — giving you that "Aha!" moment where abstract concepts become concrete attack vectors.
Phase 2: The Digital Gymnasium
You cannot learn swimming by reading a book about water. Similarly, you cannot learn hacking without touching a keyboard. You need a safe environment to fail, break things, and learn.
The Practice Grounds
Avoid the temptation to start scanning random websites. Instead, utilize purpose-built labs that gamify the learning process:
- PortSwigger Web Security Academy: This is the gold standard. Created by the makers of Burp Suite, it offers free labs for every vulnerability type imaginable, graded from "Apprentice" to "Expert."
- TryHackMe: Excellent for guided learning paths that hold your hand through the basics of networking and web requests.
- HackTheBox: Offers more unguided, "Capture The Flag" (CTF) style challenges that force you to think outside the box.
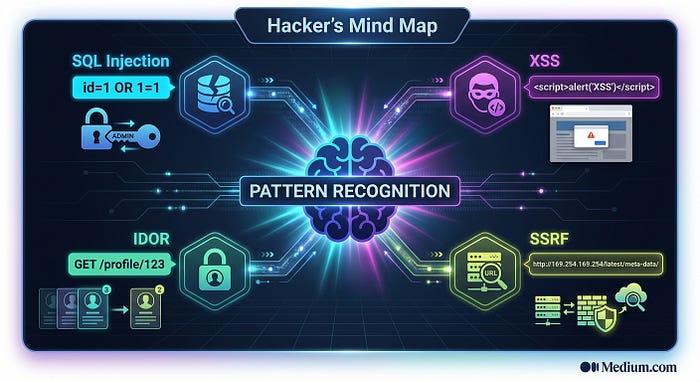
The goal here is Pattern Recognition. By solving 50 XSS labs, your brain starts to recognize the specific code structures and input fields that are susceptible to XSS. When you eventually look at a real target, you won't be guessing; you'll be relying on trained muscle memory.
Phase 3: The Curriculum (OWASP)
If you try to learn every vulnerability exists, you will be studying for a decade before you find your first bug. You need to focus on the high-probability targets.
The OWASP Top 10
The Open Web Application Security Project (OWASP) maintains a list of the 10 most critical web application security risks. This is the "Billboard Top 10" of the hacking world. These are the bugs you will see most often in the wild:
- Broken Access Control: Users acting outside of their intended permissions (e.g., a standard user accessing admin panels).
- Cryptographic Failures: Exposing sensitive data like passwords or credit cards.
- Injection: SQL, NoSQL, or Command Injection where untrusted data is sent to an interpreter.
- Insecure Design: Flaws in the architecture itself, rather than the code.
- Security Misconfiguration: Default passwords, verbose error messages, and open cloud storage.
Study these intensely. Understand how they work, how developers try to fix them, and how those fixes can be bypassed. If you master the OWASP Top 10, you understand 80% of the bug bounty attack surface.
Phase 4: The Workflow
Running a tool like generic scanners and hoping for a bug is not a strategy; it is a lottery ticket. Professional hunters use a methodology. This is where we look to industry legends like Jason Haddix.
The Bug Hunter's Methodology
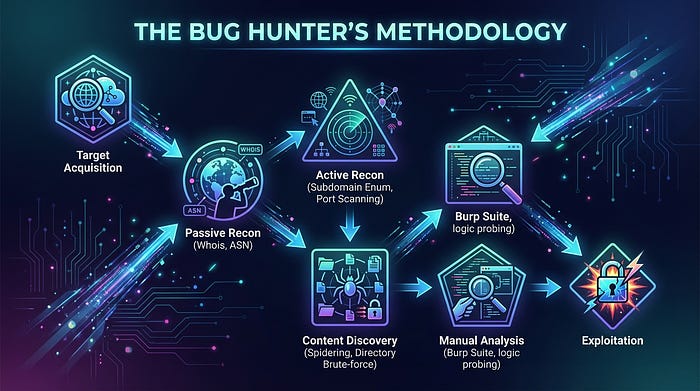
Jason Haddix's talks on "The Bug Hunter's Methodology" are legendary for a reason. He breaks down the hunt into a scientific process, heavily emphasizing Reconnaissance (Recon).
Recon is not just finding a website URL. It involves:
- Subdomain Enumeration: Finding `dev.target.com` or `staging.target.com` where security might be lax.
- Content Discovery: Brute-forcing directories to find hidden files like `/admin` or `/backup`.
- Parameter Analysis: finding hidden API parameters that the frontend doesn't show but the backend accepts.
⚠️ Warning: Don't just collect subdomains to hoard them. You need to understand what the infrastructure looks like. Is it running on AWS? Is it behind a WAF (Web Application Firewall)?
Haddix teaches you to connect the dots. You aren't just throwing tools at a wall; you are mapping the territory to find the weak points that others missed.
Phase 5: The Toolbelt vs. The Craftsman
There is a massive misconception in the beginner community that specific tools find bugs. Let's be clear: Tools do not find bugs. You do.
Tools are force multipliers. They help you find the haystack, but you still have to find the needle.
Essential Tools
- Burp Suite: This is non-negotiable. It is a proxy that sits between your browser and the server, allowing you to pause, inspect, and modify web requests on the fly. You cannot be a web hacker without knowing Burp.
- Nuclei: A powerful template-based scanner. It's great for automation, but if you don't understand why a template is triggering, you won't be able to exploit the finding.
- FFUF / Dirb: Fast tools for directory brute-forcing.
If you rely solely on automation, you will find only what everyone else has found. The bounties are found in the manual logic. Automation helps you clear the low-hanging fruit so you can focus your brain power on the complex logic flaws that scripts can't understand.
Phase 6: The Mindset and The Grind
Bug bounty hunting is a psychological game as much as a technical one. You will face rejection. You will spend three days on a target only to find nothing. You will submit a critical bug only to be told it is a "Duplicate" or "Informational."
The Feedback Loop
Every failure is data. When you get a "Not Applicable" (N/A) on a report, don't get angry — get curious. Ask yourself:
- Did I misunderstand the impact?
- Did I fail to explain the risk clearly?
- Did I miss a mitigation control?
Report Writing is the most underrated skill in the industry. You are not paid for hacking; you are paid for the report. If a security engineer cannot reproduce your bug in 5 minutes based on your report, they will close it.
Structure of a Winning Report:
- Clear Title: e.g., "IDOR in API allows takeover of any user account."
- Executive Summary: A non-technical explanation of the risk.
- Steps to Reproduce: A numbered, foolproof list.
- Impact: What can a malicious actor actually do? (Steal data, delete accounts, etc.)

Conclusion: Just Start
The path to your first bounty is not paved with expensive courses or secret tools. It is paved with persistence. It requires reading the books, doing the labs, and staring at HTTP requests until they make sense.
You will feel stupid. You will feel stuck. That is the feeling of learning. The only difference between a beginner and a top-tier hacker is that the top-tier hacker kept going when they hit a wall.
Don't wait until you feel "ready." You will never feel fully ready. Pick a program, start your recon, and look for the bugs that others aren't looking for.
