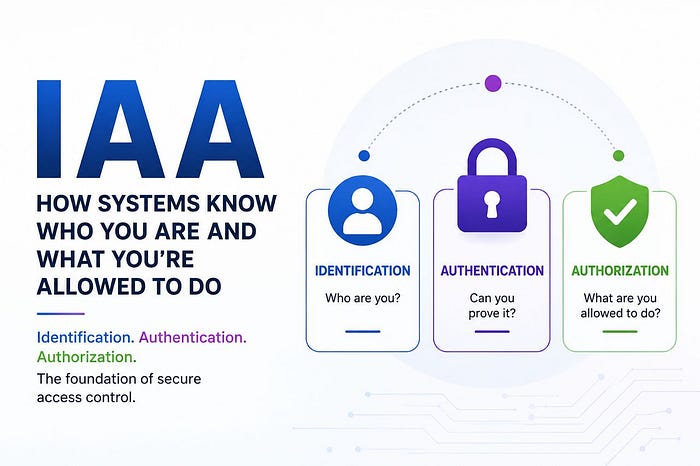
IAA: How Systems Know Who You Are and What You're Allowed to Do.
Every time you log into an application, a security process immediately begins in the background.
The system needs to answer three important questions:
- Who are you?
- Can you prove it?
- What are you allowed to access?
That process is built around three core security concepts:
- Identification
2. Authentication
3. Authorization
Together, they form the foundation of modern access control systems.
What is IAA?
IAA is a security model used to manage and control access to systems, applications, APIs, and data.
It ensures that:
- Users are properly identified,
- Their identity is verified,
- And their permissions are enforced.
Without IAA, secure systems cannot exist.

1. Identification (Claiming an Identity)
Identification is the process where a user claims who they are to a system.
At this stage, the system has not verified anything yet. The user is simply presenting an identity.
Technical Examples
Examples of identifiers include:
- Username
- Email address
- Employee ID
- API key
- Account number
Real-World Analogy
Walking into a bank and saying: "I'm Amarachi." That is identification.
The bank still doesn't know whether you are truly Amarachi.
Where Identification Appears in Systems
- Login forms
- ATM card numbers
- API requests
- SSH usernames
- Email accounts
Common Security Risks
- Username enumeration
- Predictable user IDs
- Exposed account identifiers
- API endpoint leakage
Practical Example
POST /login username=amara
The system now knows: "Someone claims to be amara." But the identity has not been verified yet.
2. Authentication (Verifying Identity)
Authentication is the process of verifying that a user is truly who they claim to be. This is where credentials are checked.
Authentication Factors
Authentication usually relies on one or more factors:
Something You Know such as password and pin
Something You Have such as OTP token, authenticator app, security key
Something You Are such as fingerprint, face recognition and biometrics
Technical Mechanisms
Systems authenticate users using:
Password hashing (bcrypt, Argon2)
- MFA (Multi-Factor Authentication)
- Session tokens
- JWTs
- OAuth flows
- SSO systems
Real-World Analogy
After saying: "I'm Amarachi."
The bank now asks for your ID card, fingerprint, or password.
That is authentication.
Common Authentication Weaknesses
- Weak passwords
- Credential stuffing
- Session hijacking
- MFA bypass
- Broken authentication logic
- Token reuse vulnerabilities
Practical Example
POST /login username=amara, password=P@ssw0rd
The system verifies the credentials.
If correct: Authentication succeeds.
3. Authorization (Controlling Access)
Authorization determines what an authenticated user is allowed to access or do. Even after login, users should not access everything.
Technical Mechanisms
Authorization is enforced using:
- RBAC (Role-Based Access Control)
- ABAC (Attribute-Based Access Control)
- ACLs (Access Control Lists)
- Permission matrices
- API authorization checks
Real-World Analogy
At the bank:
- A customer can view their account
- A cashier can process transactions
- An admin can manage the system
Each role has different permissions. That is authorization.
Common Authorization Vulnerabilities
Most critical access control vulnerabilities occur at the authorization layer.
- IDOR — Accessing resources belonging to other users
- BOLA — Broken object-level authorization in APIs
- Privilege escalation — Gaining higher permissions than intended
- Missing access control — Sensitive resources exposed without proper checks
- Forced browsing — Accessing hidden or restricted endpoints directly
- Insecure admin panels — Administrative interfaces exposed to unauthorized users
Practical Example
GET /api/users/125/profile. If a normal user changes 125 → 126 and accesses another user's data:
Authorization is broken. This is a classic IDOR/BOLA scenario.
How IAA Works Together
The process typically follows this order:
- Identification Claim identity
- Authentication Verify identity
- Authorization Enforce permissions
Real Login Flow Example
Step 1 — Identification
User enters username=amara
Step 2 — Authentication
System verifies password + MFA token
Step 3 — Authorization
System checks is user an admin?, can they access /admin?, can they edit this resource?
IAA is one of the most important concepts in cybersecurity because it controls trust and access inside systems.
A secure system must:
- correctly identify users,
2 Securely authenticate them,
3. And strictly enforce authorization.
If any of these fail: Attackers gain access they should never have had.