Introduction
Hello team,
I hope you're doing well.
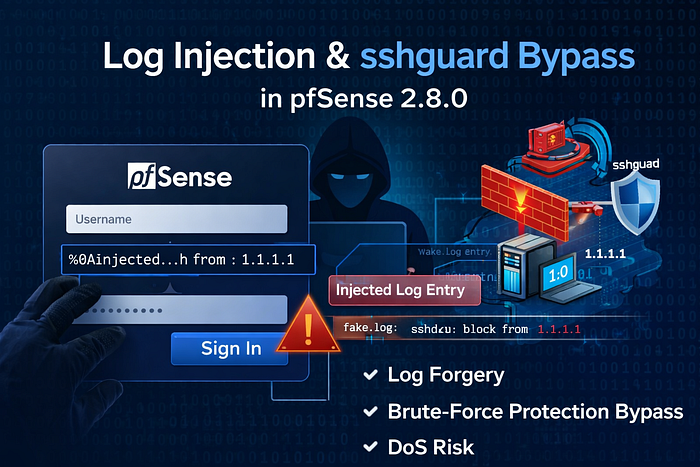
In this write-up, I present a security issue identified in pfSense 2.8.0 (stable version) affecting both log integrity and brute-force protection mechanisms.
The vulnerability combines CRLF injection in login logs with a limitation in sshguard log parsing, creating a scenario where attackers can manipulate logs and potentially bypass security controls.
📌 Vulnerability Overview
The issue exists in the WebGUI administration login panel (/index.php), where an unauthenticated external user can:
- Inject CRLF characters (
%0A) into theusernamefield - Abuse weaknesses in sshguard log parsing rules
This leads to two main security problems:
- Log Injection / Log Forgery
- Brute-force protection bypass (sshguard evasion)
- Potential firewall manipulation (DoS)
🔍 Root Cause
- Improper Input Sanitization
- Control characters (
\r,\n) are preserved - usernamefld parameter is logged with improper sanitization
- This allows log injection via CRLF
2. Weak Pattern Matching in sshguard
[a-zA-Z0-9][-_a-zA-Z0-9]+Limitations:
- Does not match valid usernames containing characters like
. - Some login attempts are not tracked, enabling bypass
🧪 Proof of Concept (PoC)
POST /index.php HTTP/2
Host: <target>
Content-Type: application/x-www-form-urlencoded
__csrf_magic=<valid_token>&usernamefld=testuser%0Aexample_entry%0A&passwordfld=testpass&login=Sign+InInjection Vector :
usernamefld=testuser%0Aexample_entry%0A📷 Observed Behavior
- Logs are split into multiple lines
- Injected content appears as legitimate log entries
- Log integrity is compromised
⚠️ Extended Impact Analysis
1. Log Integrity Violation
- Attackers can forge log entries
- Audit trails become unreliable
- Incident response is impacted
2. sshguard Brute-Force Bypass
- Usernames like
user.nameare ignored - No detection → no blocking
- Enables repeated authentication attempts
3. Log Injection Leading to Firewall Manipulation
By chaining CRLF injection with sshguard parsing behavior, attackers can influence firewall decisions.
💣Exploitation Example (DoS via sshguard)
An attack can force sshguard to block an arbitrary IP address.
Example Payload:
admin\' from: 1.1.1.1\n"exampleExplanation
- The injected newline splits the log entry
- The crafted string mimics sshguard log format
- sshguard interprets it as a real attack source
Result
- sshguard blocks the IP address:
1.1.1.1 - This leads to a denial of service between the firewall and that IP
🛠️ Mitigation Recommendations
Input Validation
- Reject
\rand\ncharacters - Strict validation on username input
Secure Logging
- Escape user input before logging
- Prevent raw log injection
🔐 Additional Reference
https://docs.netgate.com/downloads/pfSense-SA-25_09.sshguard.asc
https://github.com/pfsense/pfsense/commit/03dc855a9e48a8c808880e2db893e30737003e1a
https://github.com/SSHGuard/sshguard/commit/2295182adab901c6808182659a3de59dd012d895