Introduction
Hi everyone,
In this write-up, I will explain an interesting vulnerability I discovered in a private program on HackerOne. The issue allowed me to inject and manipulate unintended fields during form submission due to improper server-side validation.
Application Overview
The target application is an internal community platform used within organizations. It allows employees to:
- Share posts
- Participate in voting
- Submit structured forms
One of the key features is the Forms functionality, where administrators define specific fields (such as name, email, role, and custom attributes) to collect structured data from users.
Ideally, users should only be able to submit values for predefined fields controlled by the form configuration.
Vulnerability Discovery
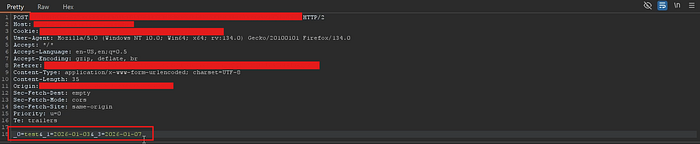
While testing the form submission functionality, I noticed something unusual in the HTTP request structure.
Instead of descriptive parameter names, the application used indexed parameters such as:
_0→ Input field_1→ Date field_3→ Another field
However, I observed that _2 was missing entirely.
This inconsistency suggested that the backend might rely on index-based mapping without strict validation.
Exploitation
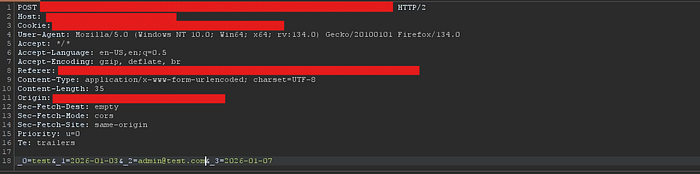
To test this behavior, I intercepted the request using Burp Suite and manually added the missing parameter:
_2 = injected_valueAfter sending the modified request, the server:
- Accepted the new parameter
- Processed it without validation
- Reflected the injected value in the application
Impact
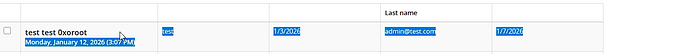
This vulnerability allows an attacker to manipulate form submissions beyond intended restrictions. Specifically, I was able to:
- Modify fields that were not exposed in the original form
- Inject values into hidden or restricted fields
Alter sensitive attributes such as:
- Last Name
- Role
- Additional Information fields
Security Risk
This issue can lead to:
- Data integrity violations
- Unauthorized data manipulation
- Potential privilege escalation (if role-based fields are affected)
In certain scenarios, this could impact business logic and trust in stored data.
Root Cause
The issue occurs due to:
- Reliance on index-based parameter mapping
- Lack of proper server-side validation
- No enforcement of allowed field indices
Conclusion
This vulnerability highlights the risks of relying on weak parameter mapping without proper validation. Even a small inconsistency, such as a missing index, can lead to unauthorized data manipulation.
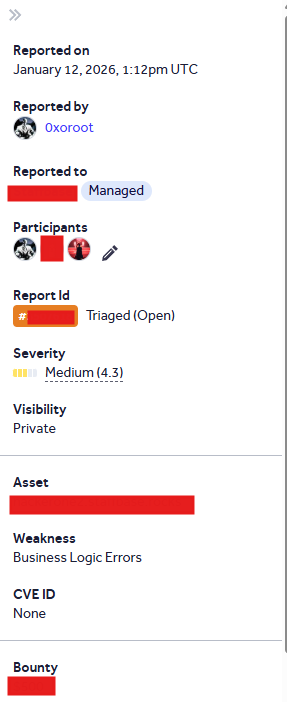
The report was submitted through HackerOne and successfully acknowledged by the program.
Thanks for reading! Feel free to reach out if you have any questions or feedback.
