Why pay for Premium when you can just ask the API nicely?
While testing a web app, I found a business logic flaw: a solid UI paywall protecting a premium feature, but a backend that blindly trusted incoming requests. Here is how a few minutes with Burp Suite unlocked the pro tier on a free account
When hunting for access control flaws, I always start by comparing two user roles:
- The Pro Account — Fully upgraded, to capture how the premium feature works.
- The Free Account — Standard limited account, to see what is blocked.
Targeting "Premium Feature X", the free account showed a "Upgrade to Pro" popup. From a UI perspective, the feature was completely locked.
Now, the moment of truth. I switched to the Free Account in my browser (where the paywall was still staring me in the face). I took the captured : let's call it createPremiumContent request from the Pro account and moved it to Burp Repeater
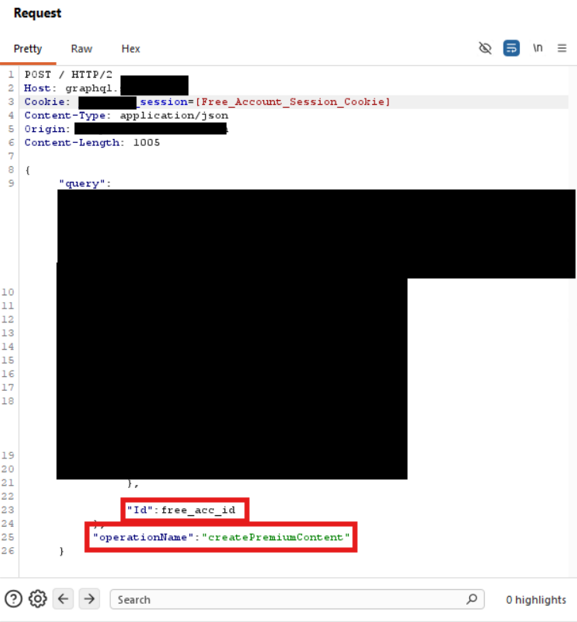
The request contained:
- User inputs (e.g., text, metadata)
- A unique user identifier (
Id) - Session cookies
I switched to the Free account. The UI still blocked me, but I didn't need the UI. I sent the Pro account's captured request to Burp Repeater and made two simple changes:
- Session cookie: Swapped the Pro session with the Free session cookie.
- User ID: Swapped the Pro account's
Idwith the Free account'sId.
then sent…
and BOOM! it works
Instead of a 403 Forbidden error, the server returned a 200 OK.
{
"data": {
"createPremiumContent": {
"id": "123456789",
"status": "SUCCESS"
}
}
}I refreshed the app on my Free account — and there it was: the premium feature, fully functional and saved to my profile, without spending a single cent.
This is a Broken Access Control (BAC). The developers fell into the "Client-Side Security" trap.
- The UI said: "No , pay first" (UX restriction).

- The API said: "You have a valid session? Sure, come on in." (No server-side authorization).
The backend verified who I was (Authentication), but never checked what I was allowed to do (Authorization).
A "paywall" is just a visual barrier. The real question is always:
What does the backend actually allow?
Intercept requests. Replay them. Modify them.
Sometimes the door isn't locked — it's just hidden.
Impact & Remediation
- Business Impact: Revenue loss and feature devaluation, as any free user can bypass the paywall indefinitely.
- The Fix: The backend must be the ultimate source of truth. Enforce authorization at the resolver level by checking the user's subscription status in the database before executing any sensitive mutation.
Never trust the UI. Always capture the "locked" requests from a high-privilege account and replay them using a low-privilege session. If the backend doesn't double-check the permissions, you've got a bug.
