People share screenshots of $500, $1,000, even $10,000 payouts — but no one explains how beginners actually get there.
The truth is simple:
Bug bounty is not about tools. Bug bounty is about understanding how web apps break.
This roadmap will show you exactly what to learn, in order, so you don't waste months jumping randomly between tools.
What is Bug Bounty?

Bug bounty is when companies pay security researchers to find vulnerabilities in their applications.
You legally test:
- Websites
- APIs
- Mobile apps
- Cloud assets
And report security issues like:
- XSS
- Open Redirect
- IDOR
- SQL Injection
- Misconfigurations
If valid → you get paid.
Step 1 — Learn How the Web Actually Works
Before hacking anything, understand:
- HTTP / HTTPS
- Request & Response
- Headers
- Cookies
- Sessions
- Authentication
- Status codes
Without this, bug bounty becomes guessing.
Learn:
- GET vs POST
- Authorization headers
- Tokens
- JSON requests
This is foundation of bug bounty.
Step 2 — Learn Basic Web Vulnerabilities
Start with beginner-friendly bugs:
1. Open Redirect
Easy to find Low risk Great first bug
2. XSS (Cross-Site Scripting)
Most common bug bounty vulnerability.
Types:
- Reflected XSS
- Stored XSS
- DOM XSS
3. Information Disclosure
Look for:
- API keys
- Debug endpoints
- Version leaks
4. Misconfigurations
Check:
- CORS
- Security headers
- Exposed panels
These bugs build your hacker mindset.
Step 3 — Learn Recon (Most Important)
Recon = finding attack surface.
This is where most bugs are found.
Learn:
- Subdomain discovery
- Parameter discovery
- Hidden endpoints
- Admin panels
Tools beginners use:
- Subfinder
- Amass
- Assetfinder
- Waybackurls
- Gau
Manual recon is even more powerful.
Step 4 — Learn Google Dorking for Bug Bounty
Google is powerful for finding:
- Login pages
- Admin panels
- Dev environments
- Exposed files
- Backups
Examples:
site:example.com inurl:admin
site:example.com ext:log
site:example.com inurl:loginThis helps find low hanging bugs.
Step 5 — Learn How to Use Burp Suite
Burp Suite is the main bug bounty tool.
Use it to:
- Intercept requests
- Modify parameters
- Test payloads
- Replay requests
Start with:
- Proxy
- Repeater
- Intruder (basic)
Burp teaches you how apps really behave.
Step 6 — Learn Common Bug Bounty Vulnerabilities
Focus on these first:
- IDOR
- XSS
- Open Redirect
- CSRF
- SSRF (later)
- Access Control Issues
Most beginner bounties come from: 👉 IDOR 👉 Misconfigurations 👉 XSS
Step 7 — Choose Bug Bounty Platforms
Start here:
- HackerOne
- Bugcrowd
- Intigriti
- YesWeHack
Pick one program only at start.
Don't hunt everywhere.
Step 8 — Beginner Bug Hunting Method
Use this workflow:
- Pick target
- Do recon
- Find parameters
- Test access control
- Test redirects
- Test XSS
- Check APIs
- Check hidden endpoints
Repeat.
Bug bounty is pattern recognition.
Step 9 — Realistic Timeline for Beginners

Week 1–2 Learn web basics
Week 3–4 Learn vulnerabilities
Month 2 Start recon
Month 3 Start hunting
Month 4+ First valid bug (typical)
Consistency matters more than tools.
Step 10 — Beginner Mistakes to Avoid
Jumping between tools Copying payloads blindly Testing without understanding Skipping recon Expecting fast money
Bug bounty rewards patience.
Best First Bugs to Hunt
Open Redirect IDOR Information disclosure Misconfigured CORS Debug endpoints
These are beginner friendly.
How Beginners Actually Earn
First bounty usually:
$50 — $300
Then:
$300 — $1000
Then:
$1000+
Focus on learning, not money.
Money follows skills.
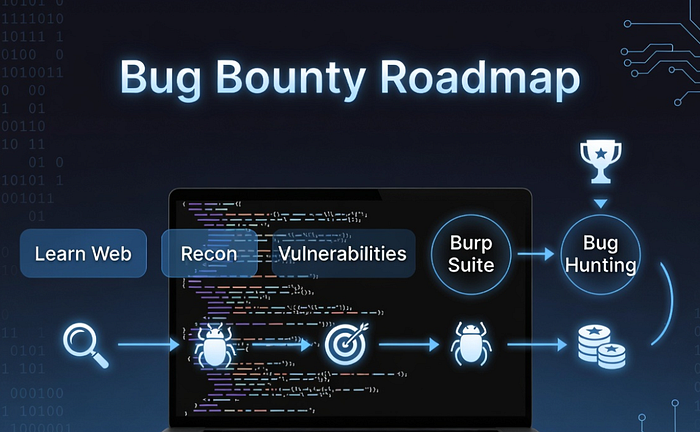
Final Beginner Bug Bounty Roadmap
Learn Web Basics Learn Vulnerabilities Learn Recon Learn Burp Suite Pick Program Start Hunting Stay Consistent
That's it.
No shortcuts.
Just practice.