Hello Amazing Hackers, I hope you all are doing great. This is Akchhat back with another blog. Today We'll be taking a deeper look into the Active Directory Certificate Services Abuse which is also one of the most common misconfiguration that can be found in a real-world AD Pentest.
What is Active Directory Certificate Service?
The Active Directory Certificate Services (AD CS) is a Microsoft Windows server role that provides a public key infrastructure (PKI). It allows you to create, manage, and distribute digital certificates, which are used to secure communication and transactions across a network.
It serves as the foundation of an organization's PKI, making it possible to create, manage, and distribute digital certificates securely. By doing so, it strengthens overall security and enables important features like certificate-based authentication, data encryption, and digital signatures.
The ADCS is also very widely used across the industry as a means of Authentication. ADCS integrates with Active Directory Domain Services (AD DS) to enable automatic enrollment for domain-joined devices.
Common ADCS Misconfigurations
ESC 1
ESC1 turns "any domain user" into Domain Admin. ESC1 doesn't require exotic access or prior privilege escalation. If you have any valid domain credentials, you already meet the only real prerequisite which is authentication. From that foothold, tools like Certipy-ad can enumerate certificate templates exposed by AD CS and identify ones that are dangerously misconfigured.
When a template allows low-privileged users to enroll and lets them supply arbitrary subject information like UPN, the game is basically over. You simply request a certificate impersonating a high-privileged account , such as Domain Admin and authenticate using that certificate.
Whenever you see that there is Certificate Service in the AD environment it is important to check for the common misconfigurations in the service as this small misconfiguration could lead an attacker to a Domain Admin such as in the case of ESC1.
ESC 2
ESC2 is another dangerous misconfiguration in Active Directory Certificate Services (AD CS). It occurs when a certificate template is available to low-privileged users and includes powerful Extended Key Usages (EKUs) such as:
- Client Authentication
- Smart Card Logon
- Any Purpose
At first glance, these EKUs might seem harmless — they're commonly used in enterprise environments. The problem arises when ordinary domain users are allowed to enroll in such templates without strict controls.
These EKUs effectively tell Windows:
"This certificate is valid for authentication."
Once an attacker can request a certificate with one of these authentication capable EKUs, they can use it to log in via Kerberos PKINIT.
If the certificate can be mapped to another account (for example, through UPN or other identity fields), the attacker can authenticate as that user potentially even a highly privileged one.
In short, ESC2 abuses overly permissive authentication enabled templates to bypass traditional credential based security entirely.
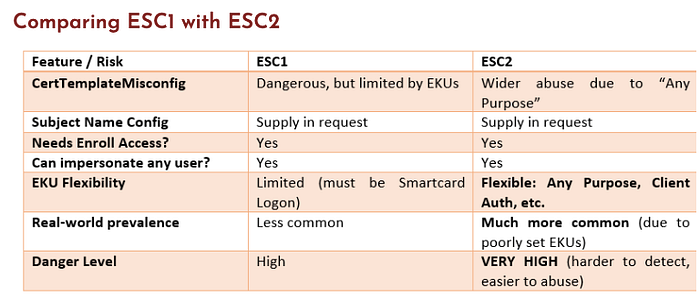
In the ESC2 the core is that the attacker can simply enroll for a certificate and authenticate completely sidestepping MFA and any password complexity policies in place.
ESC3
ESC3 is another powerful AD CS misconfiguration that can quietly lead to full domain compromise.
This escalation path becomes dangerous when a Certificate Request Agent (CRA) template is misconfigured. A CRA certificate is meant to allow trusted accounts (like helpdesk or enrollment services) to request certificates on behalf of other users. In a properly secured environment, this capability is tightly controlled.
However, if low-privileged users are allowed to enroll in a CRA template, the impact is severe.
If not tightly controlled, ADCS can become a powerful tool for lateral movement and privilege escalation in a domain.
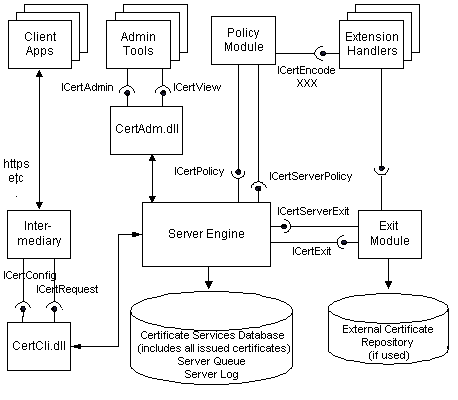
The image above gives an overview on how this actually works in real-world.
ESC4
In a Microsoft environment, Certificate Templates act as blueprints for digital IDs. If a template has weak Access Control Entries (ACEs), an attacker who shouldn't have "Manager" rights suddenly finds they can edit the blueprint.
By exploiting ESC4, an attacker doesn't just steal a certificate; they reconfigure the template itself to remove security restrictions, effectively turning a harmless document into a Golden Ticket for the domain.
The ESC4 attack becomes possible when the following conditions are met
- True — Low-privileged user has Write/Owner/Modify permissions on a certificate template (e.g., WriteOwner, WriteDacl, WriteProperty).
- True — Low-privileged user has Enroll or Autoenroll permission on the vulnerable template.
- True — The template allows specifying a custom Subject Alternative Name (SAN) (e.g., to spoof a Domain Controller FQDN).
- True — The template includes or can be modified to include Server Authentication EKU (3.6.1.5.5.7.3.1).
Prevention and Detection
Here are a few steps you can take to harden your certificate templates.
- Take stock of your certificate templates and determine whether all enabled templates are currently in use. Disable all templates that are unnecessary.
- Make sure that template permissions are as restrictive as possible. Only grant necessary groups/users enrollment permissions.
- Modify the "Issuance Requirements" to require the manual approval of an issued certificate where possible.
- Disable the "Enrollee Supplies Subject" flag where possible.
- Remove "Client Authentication" where possible.
Tools
Below are the tools that can be used to Detect and exploit the Vulnerable Templates and Escalate our privileges from a standard domain user to compromising and becoming a Domain Administrator(or any other user with similar rights).
- Certipy-ad (https://github.com/ly4k/Certipy)
- Bloodhound can be used to detect if the Certificate server is present in the domain and can be utilized to Map out the AD Domain. It is also often referred to as the "Google Maps" for the Active Directory.
- Powershell( even If we have have access as a standard user, it could be very useful as the native powershell commands can be used the certificate authority)
- RUBEUS ( It is another great tool that can be used to take certificates obtained via exploitation and request a Kerberos Ticket Granting Ticket (TGT) for authentication e.g., in ESC1/ESC3).
Final Words
During An Internal Pentest Engagement, It becomes very important to check whether there is a Certificate Server running in the environment as it can be a very crucial attack path for the Attackers.
The AD CS Misconfigurations are one of the most common thing that could be found in the AD environment and this small misconfig could lead to a domain compromise and hence it really comes down to having the Penetration Tests in regular intervals to ensure that these could be patched at the earliest.
References
Below is a List of references that can be used to Study the Active Directory Certificate Services Exploitation in Depth:
If you liked the Blog and want to Discuss in Detail regarding ADCS Abuse or any other Red Teaming Topics, I would love to connect and you can find me by Social Media Links Below:
Linkedin: www.linkedin.com/in/akchhat-701234306
Github: https://github.com/akchhat1211
Instagram: https://www.instagram.com/akchhat_official?utm_source=qr&igsh=MWlidXJmeWVxazk0Yg==
Stay Tuned, Next Blog Post will be coming soon!!
I'll Be happy to have some feedbacks as well so I could improve, until next time, Happy Hacking!!!