Welcome back, hackers! Today we are taking a look at Dancing, one of those Windows boxes that rewards calm enumeration more than flashy exploitation. The setup is straightforward, the attack surface is small, and the path to the flag is hiding in plain sight if you pay attention to what the services are giving you.
It does not ask for a complicated exploit chain. It asks whether you will notice an exposed SMB path, test it properly, and follow the evidence all the way to the end.
That might sound simple, but that is exactly the kind of habit that makes a big difference on larger targets too.
Executive summary
- Target: HTB box
- Initial access vector: SMB (445/tcp) with anonymous access
- Privilege level achieved: Root
- Big idea: Simple services still break environments when permissions are weak
Reconnaissance
I started the same way I always should: scan the target and see what it is willing to show me.
nmap -sC -sV -p- 10.129.48.3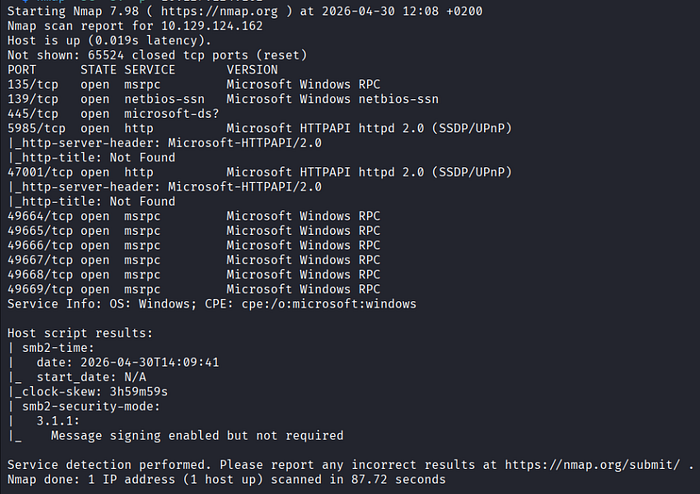
The key results were:
- 135/tcp — MSRPC
- 139/tcp — NetBIOS
- 445/tcp — SMB/microsoft-ds
- 5985/tcp — WinRM
That immediately told me two things:
- This was a Windows box.
- SMB was my first stop.
WinRM is useful once credentials enter the picture. SMB is useful when access control is loose and files are exposed more broadly than they should be. On a box like this, that makes SMB the more natural first choice.
Lesson learned: when you see 騕/tcp' on a Windows box, slow down and enumerate properly before jumping ahead.
Testing SMB
My first question was simple: does SMB allow anonymous access?
I tested that by attempting to list shares without providing credentials:
smbclient -L //10.129.124.162/ -NThe server responded with a list of shares, confirming that unauthenticated access was allowed.
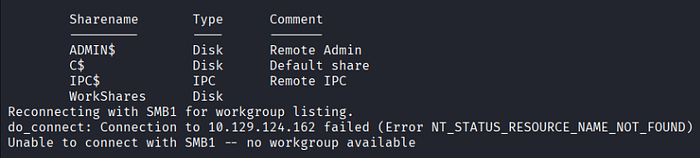
That was the opening I needed.
WorkShares immediately stood out. On a box like this, a readable share with a name like that is usually the whole story.
Inside the share: following the evidence
Next I connected to the exposed share and listed everything recursively:
smbclient //10.129.48.3/WorkShares -N
recurse
ls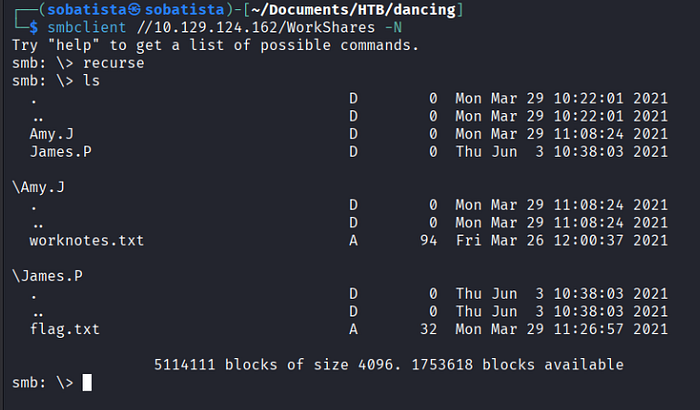
That revealed two user-named directories:
- Amy.J
- Hames.P
And inside them:
- Amy.J/worknotes.txt
- James.P/flag.txt
And there it was the flag.
Reading the file
First, change into the directory:
cd James.PThen getting the file:
get flag.txt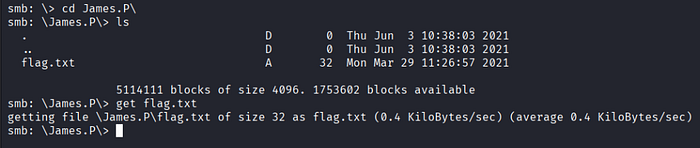
Back on my attacker machine:
cat flag.txtThe challenge Q&A (answers)
If you are doing the Starting Point tasks as you go, here are the key answers:
- What does the 3-letter acronym SMB stand for? Server Message Block
- What port does SMB use to operate at? 445
- What is the service name for port 445 that came up in our Nmap scan? microsoft-ds
- What is the 'flag' or 'switch' that we can use with the smbclient utility to 'list' the available SMB shares on Dancing? -L
- How many shares are there on Dancing? 4
- What is the name of the share we are able to access in the end with a blank password? WorkShares
- What is the command we can use within the SMB shell to download the files we find? get
Final Flag (in base64 encoding)
NWY2MWMxMGRmZmJjNzdhNzA0ZDc2MDE2YTIyZjE2NjQ=
Note: To decode run:
echo -n "encoded_string" | base64 --decodeLessons learned & best practices
This box is a good reminder that the simplest services can still break an environment.
FTP may feel outdated, but it still shows up in real systems, often misconfigured and exposed just like this. Old does not mean safe.
Anonymous login is not a convenience feature, it's a vulnerability. If a service lets anyone in without credentials, access control has already failed.
Once again, the basic tools did all the work. Nmap, a standard FTP client, and a few simple commands. No exploits, no tricks. Just clean enumeration and following what the service gives you.
That's the real takeaway: master your fundamentals. Most boxes, and a lot of real-world issues, don't require anything fancy.
Finally, keep your workflow disciplined. Good notes and clean steps turn a quick solve into something reusable, whether that's for reports, future engagements, or your own learning.
Findings & remediations (for devs & ops)
Finding: SMB share accessible anonymously without proper restriction. Severity: High. Impact: Unauthenticated users can enumerate shares and read internal files, including sensitive operational notes and proof material.
Recommended fixes:
- Disable anonymous SMB access unless it is explicitly required
- Tighten both share permissions and underlying NTFS permissions
- Remove sensitive files from guest-accessible or broadly readable shares
- Audit Windows file shares regularly
Misconfigurations like this are not flashy, but they are dangerous precisely because they are easy to miss and easy to abuse.
Final thoughts
Dancing is a small box, but the lesson behind it is very real: if access control is weak, the attacker may not need an exploit at all. In this case, one exposed share and a few careful enumeration steps were enough.
If there is one takeaway here, it is this:
Do the simple checks well before you go hunting for complicated bugs.
That habit will save you time on CTFs, real pentests, and even your own writeups.
Happy hacking, and I'll see you in the next write-up!
Cheers, SoBatista