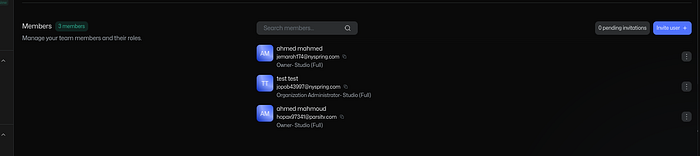
Hi, I'm Ahmed Mahmoud, a penetration tester on HackerOne. Today I'll walk you through how I was able to escalate my privileges and become an Owner in an organization that strictly allows only one owner.
Let's start.

Overview of the Vulnerability:
The application enforces a rule:
Only one Owner is allowed per organization.
However, I discovered a flaw in the invite flow validation.
As a result:
- Direct role escalation is blocked (returns 403)
- But invite requests are not properly validated
- I was able to assign myself the Owner role
- And join the organization as a second Owner
A simple validation inconsistency led to a full privilege escalation.
Steps To Reproduce:
- Create an organization — you are the default Owner
- Add an Admin : Invite another account and assign it the Admin role.
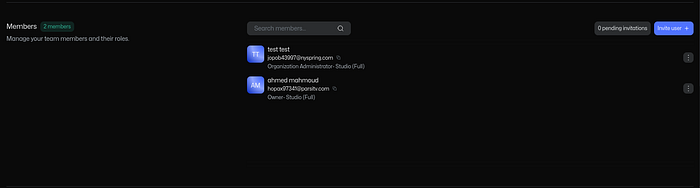
3. Add a Low Privileged User: From the Admin account, invite a third account with role:
Orders Manager(low privilege).
4. From the Admin account, try to update the low-privileged user's role to Owner via a PATCH request.
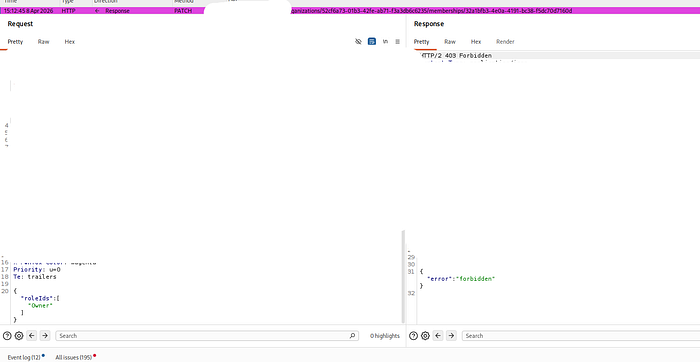
Result: 403 Forbidden This confirms the system correctly blocks direct role escalation.
So… what if we try another way?
Instead of modifying an existing user, let's try to manipulate the invite request itself.
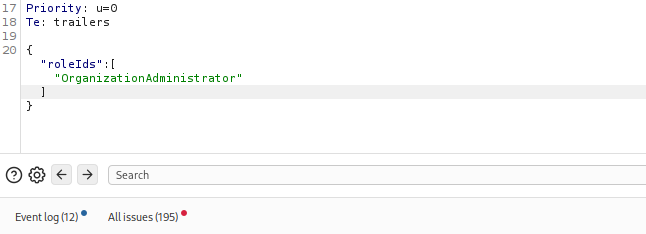
5. From the Admin account: invite new user. 6. Intercept and Modify the Request : Using a proxy tool (like Burp Suite), intercept the request.
Original request:
"roleIds": ["OrdersManager"]Modify it to:
"roleIds": ["OWNER"]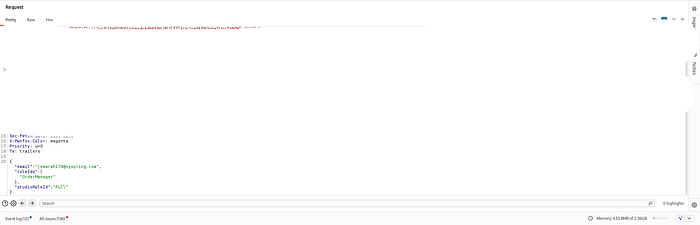
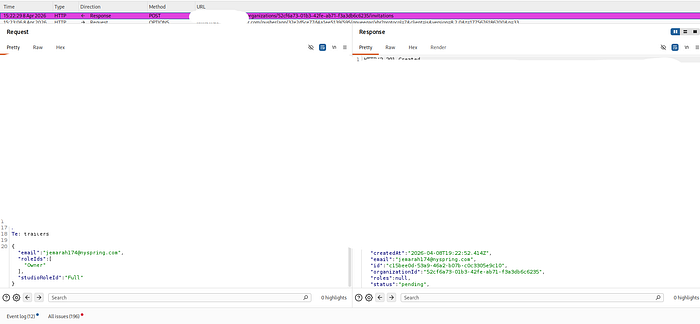
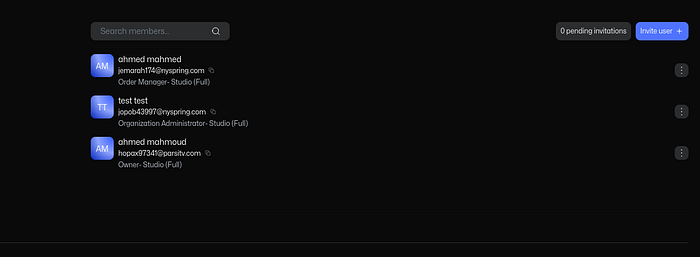
7. Accept the Invitation, log in to the new account.
Boom!
The account is now:Owner Even though the system is supposed to allow only one.
Impact:
- An Admin can escalate privileges to Owner
- Multiple Owners can exist despite restrictions
- Full organization control, including:
- User management
- Access to sensitive data
- Billing and settings control
- Ownership transfer
👉 This leads to full organization takeover
Recommended Fix:
1. Validate roles in invite requests:
Do not allow users to assign roles higher than their own.
2. Block assigning Owner via API:
Owner role should not be set through invites.
3. Enforce single Owner rule:
If an Owner already exists → reject request.
Conclusion
This vulnerability shows how inconsistent validation between different endpoints can lead to critical security issues.
Even though direct privilege escalation was blocked, the invite feature became a hidden attack vector.
Thanks for reading!!
