Table of Contents
Summary of the Vulnerability
A single-endpoint race condition occurs when multiple requests sent to the same HTTP endpoint are processed concurrently without proper synchronization on the server side.
In this lab, the vulnerability exists in the email change functionality, where the server allows multiple simultaneous requests to update the account email address. The application does not correctly lock the account state during the update process, creating a race window where different email values can be submitted at nearly the same time.
The key condition that makes this exploitable is the presence of a pending administrator invitation for the email address carlos@ginandjuice.shop. The system automatically grants admin privileges to any account that successfully registers or claims this email address. Because the email change operation is not atomic, an attacker can send parallel requests attempting to update their email to the target address, increasing the chance that one of the requests succeeds before the system finalizes validation.
By winning this race condition, the attacker can associate their account with the invited email address, inherit administrator privileges, access the admin panel, and perform privileged actions such as deleting users.
Proof of Concept (PoC)
- Open the lab and log in using the provided credentials
wiener:peter. After logging in, the assigned email address will look like this:
wiener@exploit-0a6600340453a1c484dc771e01a300a2.exploit-server.net- Update the email address to a new value, for example:
testing@exploit-0a6600340453a1c484dc771e01a300a2.exploit-server.net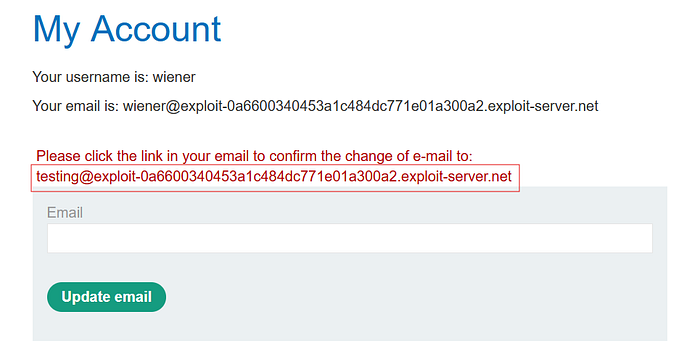
- Open the email client, verify the email confirmation message, then refresh the profile page to ensure the update is applied.
- Inspect the traffic in Burp Suite → HTTP history, locate the request to the
change-emailendpoint, and send the request to Repeater.
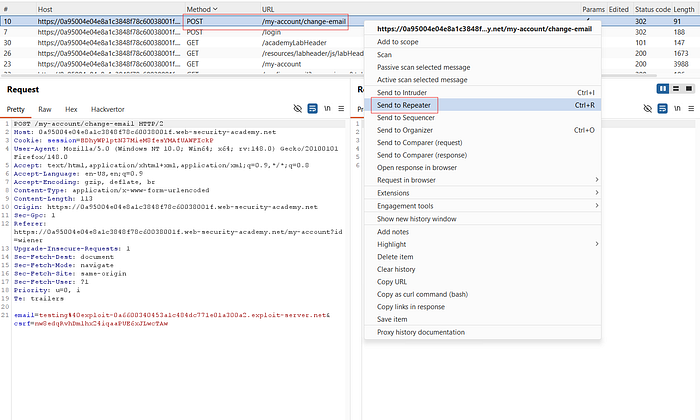
- Duplicate the request tab in Repeater. In this case, use two different email values:
- Tab 1:
testing_one%40exploit-0a6600340453a1c484dc771e01a300a2.exploit-server.net
- Tab 2:
testing_two%40exploit-0a6600340453a1c484dc771e01a300a2.exploit-server.net- Combine both tabs into a single tab group:
Add tab to group → New tab group → Select all → Click Create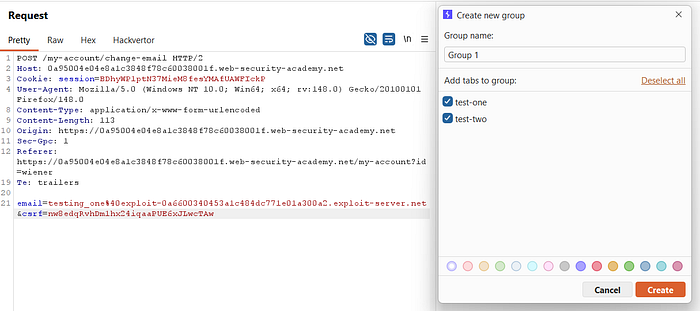
- Change the send method to:
Send group in parallel (single-packet attack)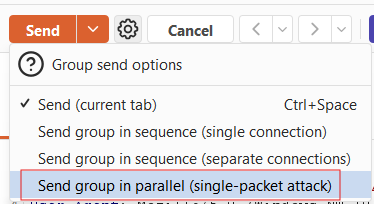
- This forces both requests to reach the server at nearly the same time.
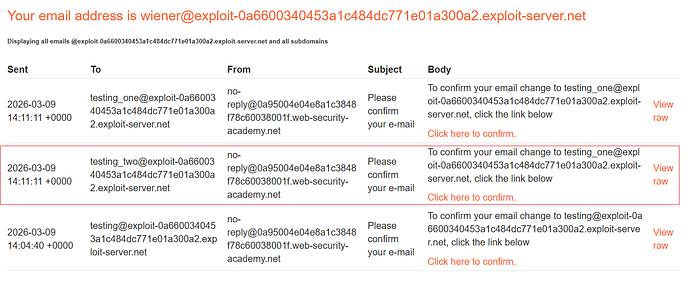
- After sending the grouped request, two confirmation emails will arrive. However, after verification, the profile is updated only with the email from the first request (
testing_one). This behavior indicates a race condition during the email update process.

- The goal is to take over the invited administrator email:
carlos@ginandjuice.shop- Modify the second tab so that it uses the target email:
- Tab 1:
testing_one@exploit-0a6600340453a1c484dc771e01a300a2.exploit-server.net
- Tab 2:
carlos@ginandjuice.shop- Send both requests again using Send group in parallel (single-packet attack).
- Refresh the email client. You will receive a confirmation email for
carlos@ginandjuice.shop.
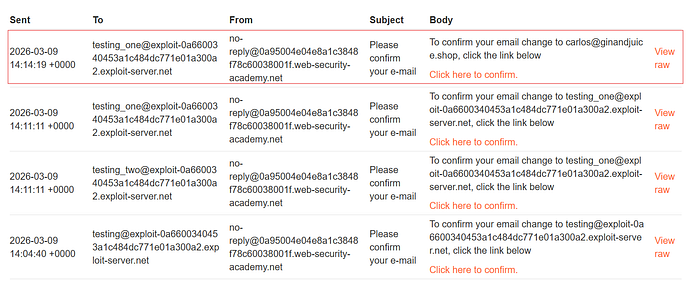
- Confirm the email change.
- Refresh the profile page. The account email is now updated to:
carlos@ginandjuice.shop- Since this email has a pending administrator invitation, the account is automatically granted admin privileges.
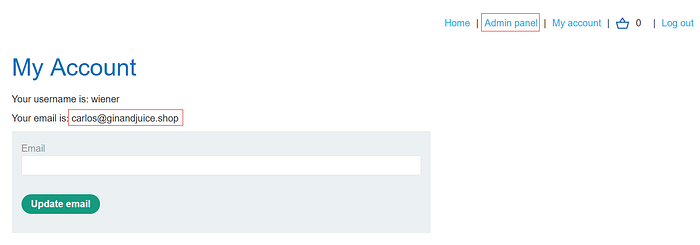
- Access the Admin Panel, then delete the user
carlosto complete the lab.

Impact
If a real application automatically assigns roles based on email address, invitation status, or account state, a race condition could allow an attacker to claim identities that were never intended for them. This could result in unauthorized access to administrative dashboards or restricted functionality.
Potential real-world consequences include:
- Privilege escalation Attackers may gain administrator access by claiming invited or reserved email addresses.
- Account takeover Race conditions in profile update endpoints could allow overwriting another user's identity data.
- Bypassing business logic Systems that rely on sequential validation steps can be broken when requests are processed in parallel.
📢 Enjoyed this post? Stay connected! If you found this article helpful or insightful, consider following me for more:
- 📖 Medium: bashoverflow.medium.com
- 🐦 Twitter / X: @_havij
- </> Github: havij13
- ☕ Coffee: Buymeacoffee
🙏Your support is appreciated.

