Plaintext is readable data; it can be a simple "hello", a cat photo, credit card information, or medical health records — anything. From a cryptography perspective, all of these are "plaintext" messages that are waiting to be encrypted.
Plaintext is passed through an encryption function along with a proper key; the encryption function returns a ciphertext. The encryption function is a part of the cipher; and a cipher is an algorithm that is used to convert plaintext into ciphertext and ciphertext back into plaintext.
- Plaintext:
HELLO - Key:
3 - Encryption Function:
- Move each letter 3 steps forward in the alphabet
Step-by-step Encryption
Plaintext Letter+3Ciphertext LetterH→KE→HL→OL→OO→R
Result
- Plaintext:
HELLO - Key:
3 - Ciphertext:
KHOOR
HELLO + Key(3) → Encryption Function → KHOOR
Decryption (reverse process)
Now, if someone gets the ciphertext KHOOR and knows the key (3):
Decrypted Letter = Ciphertext Letter - Key- K → H
- H → E
- O → L
- O → L
- R → O
We get back again: HELLO
The encryption function takes plaintext and key as input and provides ciphertext as output.
To recover plaintext, we must pass the ciphertext through the decryption function with the correct key, which will give us the original plaintext.
The decryption function takes ciphertext and key as input and provides plaintext as output.
We have now introduced a few new terms, and knowing these terms is extremely important for understanding any writing related to cryptography. Explanations of the terms are given below:
Plaintext:
The original, readable message or data before encryption. It can be a document, image, multimedia file, or any other binary data.
Ciphertext:
The scrambled, unreadable form of the message after encryption. Ideally, it should not be possible to obtain any meaningful information about the original plaintext from the ciphertext, except for an approximate size.
Cipher:
An algorithm or method that converts plaintext into ciphertext and ciphertext back into plaintext. A cipher is usually designed by a mathematician.
Key:
A string of bits that a cipher uses to encrypt or decrypt data. Although commonly used ciphers are public knowledge, the key must remain secret — unless it is a public key in the case of asymmetric encryption. Asymmetric encryption will be discussed in the next task.
Encryption:
A process in which plaintext is converted into ciphertext using a cipher and a key. The key remains secret, while the cipher is usually public.
Decryption:
The reverse process of encryption, in which ciphertext is converted back into plaintext using a cipher and a key. Although the cipher may be public knowledge, without the key, recovering the plaintext should be computationally infeasible.
Two Main Types of Encryption
Encryption is generally divided into two categories:
- Symmetric Encryption
- Asymmetric Encryption
Symmetric Encryption
In Symmetric Encryption, the same key is used to encrypt and decrypt data.
For this reason, it is also called Private Key Cryptography.
🔹 How it works
- Both the sender and the receiver have the same secret key
- Sender → uses the key to turn plaintext into ciphertext
- Receiver → uses the same key to turn ciphertext back into plaintext
If the key is leaked, the entire security is broken
🔹 Key Sharing Problem
Securely sharing the key is the biggest challenge of symmetric encryption.
Real-world example
Suppose —
- You create a password-protected document
- Sending the document by email is easy
- But sending the password by email is risky
Because:
- If someone gains access to the email, they will get both the document and the password
So, sending the password requires a separate secure channel
Often, the solution is telling the password in person
🔹 Problem with Powerful Adversaries
When —
- There are many recipients
- Or there is a powerful adversary like industrial espionage
Then keeping the key secret becomes even more difficult.
🔹 Examples of Symmetric Encryption
DES (Data Encryption Standard)
- Became a standard in 1977
- Key size: 56-bit
- Broken in less than 24 hours in 1999
3DES (Triple DES)
- DES applied three times
- Key size: 168-bit
- Effective security: 112-bit
- Deprecated in 2019 (not recommended for use)
AES (Advanced Encryption Standard)
- Became a standard in 2001
- Key size: 128 / 192 / 256-bit
- Currently the most widely used and secure
Asymmetric Encryption

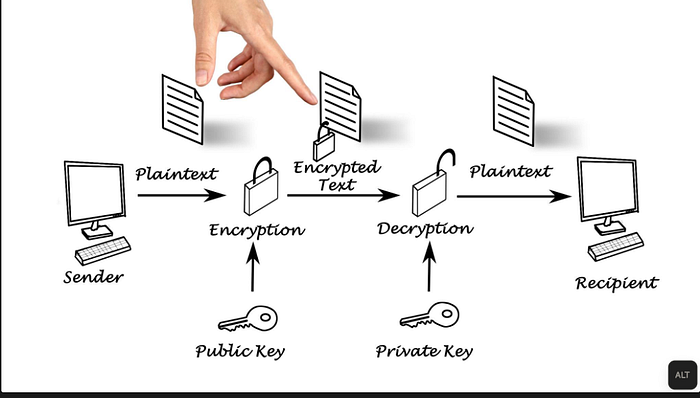
In Asymmetric Encryption, two different keys are used:
- Public Key → For encryption
- Private Key → For decryption
This is called Public Key Cryptography.
🔹 How it works
- The receiver shares their public key with everyone
- Sender → encrypts the message using the public key
- Receiver → decrypts it using their private key
There is no problem if the public key is known to everyone
The private key must be kept secret
🔹 Why is Asymmetric Encryption slow?
- It is mathematically very complex
- Key sizes are very large
- Therefore, it is slow compared to symmetric encryption
🔹 Examples of Asymmetric Encryption
RSA
- Key size: 2048 / 3072 / 4096-bit
- Minimum recommended: 2048-bit
Diffie-Hellman
- Minimum: 2048-bit
- Stronger security: 3072 / 4096-bit
ECC (Elliptic Curve Cryptography)
- Higher security with smaller keys
- 256-bit ECC ≈ 3072-bit RSA
Mathematical Foundation
Asymmetric encryption is based on mathematical problems that are:
- Easy to do in one direction
- Almost impossible to do in the reverse direction
With today's technology, solving these problems could take millions of years
How Asymmetric Encryption Works
Asymmetric Encryption is a method where two different keys are used — one Public Key and the other Private Key.
Roles of the Two Keys
- 🔓 Public Key
- Can be shared with everyone
- Used to encrypt data
- 🔐 Private Key
- Kept only by the owner
- Used to decrypt data
Data encrypted with a public key can be decrypted only with the matching private key.
Step-by-Step Process
Step 1: Key Pair Generation
The receiver (let's say Bob) generates two keys:
- One Public Key
- One Private Key
Step 2: Public Key Sharing
Bob shares his Public Key with everyone
(It can be via the internet, website, email — any medium)
Step 3: Message Encryption
The sender (let's say Alice) —
- Takes Bob's Public Key
- Message (plaintext) → Encrypts → becomes Ciphertext
Step 4: Sending the Encrypted Message
Alice sends the encrypted message to Bob
Even if someone intercepts it in between, they won't understand anything
Step 5: Message Decryption
Bob —
- Uses his Private Key
- Ciphertext → Decrypts → gets the original message
Simple Real-World Example (Box Analogy)
Imagine —
- Bob creates a locked box
- He gives the open lock to everyone (Public Key)
- Alice locks the box using that lock and sends it
- There is only one key to open the box, and it is with Bob alone (Private Key)
Anyone can lock the box
But only Bob can open it
Why Is It Secure?
Asymmetric encryption relies on mathematical problems that are:
- Easy to do in one direction
- Almost impossible to do in the reverse direction
Example:
- Multiplying large numbers is easy
- But breaking them down to find their factors is extremely difficult
