0x0d9, Yieldbox, and Holdstation Exploits: $10.64M Lost to Authorization Bypass, Oracle Manipulation, and Key Compromise
0x0d9 lost $180K after empty signature arrays bypassed authorization checks. Yieldbox lost $10M when a low-liquidity oracle allowed an attacker to inflate collateral prices and overborrow. Holdstation lost $462K after a compromised developer key enabled a malicious contract upgrade. Three different failures — access control, oracle design, and key security — combined to cause over $10.6M in losses.
In Brief
- 0x0d9 lost $180K because of bypassed authorization checks.
- Yieldbox lost $10M after a low-liquidity oracle was manipulated to inflate collateral value.
- Holdstation lost $462K due to a compromised developer key.

Hacks Analysis
0x0d9 | Amount Lost: $180K
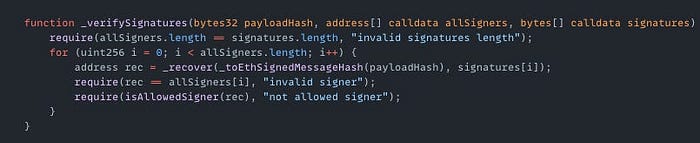
On February 27th, the 0x0d9 contract exploit on the BSC resulted in a $180K loss. The root cause of the exploit was missing access control for non-empty signature inputs in _verifySignatures() function. This function only required allSigners.length == signatures.length. If both arrays were empty, the check passed. The attacker submitted empty allSigners and signatures arrays and the contract treated the request as verified. This bypassed signature authorization and allowed the attacker to withdraw funds.
Exploited Contract (on BNB): 0x79f9b0b81e08efc3690bb78611620cb1b708fccb
Transaction: 0x0d9e4478567aa33dad3bd7c9a79de5f2afc9c7037c026795aa838f5ab834ca80
Yieldbox | Amount Lost: $10M
On February 22nd, the YieldBlox Blend pool exploit on Stellar resulted in a $10M loss. The root cause of the exploit was an price oracle manipulation of a low liquidity USTRY/USDC market. The protocol relied on a VWAP (Volume Weighted Average Price) oracle which calculated the price using recent trades and their volume. Because the market had almost no activity, the attacker was able to increase the USTRY price from $1 to $106 with a single swap. The attacker first deposited 13,003 USTRY, borrowed 1,000,196 USDC, then added 140,000 more USTRY as collateral and borrowed 61,249,278 XLM to make a profit.
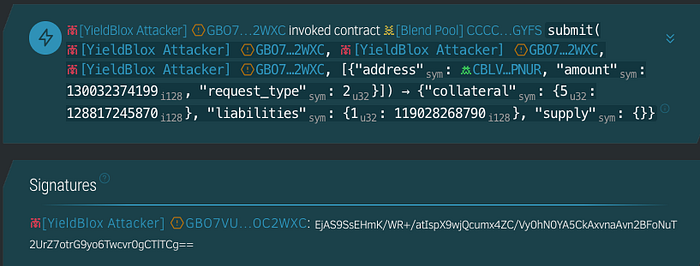
Exploited Contract (on Stellar): CCCCIQSDILITHMM7PBSLVDT5MISSY7R26MNZXCX4H7J5JQ5FPIYOGYFS
Transaction: b810ba4a8d7547bb024f17b58c32cc644533176206d0f8178d4ba0a545cb7597
Holdstation | Amount Lost: $462K
On January 28th, the Holdstation exploit on World Chain and BSC resulted in a $462K loss. The root cause of the exploit was a malicious IDE extension that exposed a private key used to manage protocol upgrades. The attacker gained upgrade permissions on the Vault Proxy contract and upgraded the proxy to point to a malicious contract. This allowed the attacker to withdraw funds and make a profit.
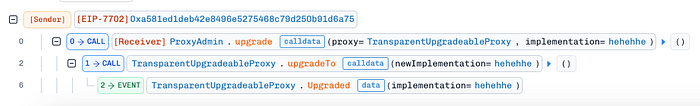
Exploited Contract (on BNB): 0xA581ED1dEB42E8496E5275468C79D250b91d6a75
Transaction (ProxyAdmin upgrade): 0x5e2e02c849356e7837d9bfcd279ebba55a16984c9e17e33123efe625e8777d9b
Olympix: Your Partner in Secure Smart Contracts
Olympix provides advanced Solidity analysis tools to help developers identify and fix vulnerabilities before they become critical exploits.
Get started today to fortify your smart contracts and proactively shield them from exploits in the evolving Web3 security landscape.
Connect with us on:
Twitter | LinkedIn | Discord | Medium | Instagram | Telegram | Newsletter
