The goal of this challenge is to exploit a Broken Access Control vulnerability that allows users to view other users' shopping baskets by manipulating request identifiers. The challenge demonstrates an Insecure Direct Object Reference (IDOR) vulnerability caused by improper authorization checks.
Challenge Overview
Title: View Basket Category: Broken Access Control Difficulty: ⭐⭐ (2/6)
Tools Used
Web browser Burp Suite - For intercepting and modifying HTTP requests
Methodology
Inspecting the basket functionality in Burp Suite shows that the application retrieves basket contents using a user-specific identifier in the request path, which suggests that modifying this identifier may allow access to other users' basket data. Steps to exploit the vulnerability:
- Enable Intercept in Burp Suite and open the basket to capture the request. Observe the request path containing the basket identifier:
/rest/basket/:id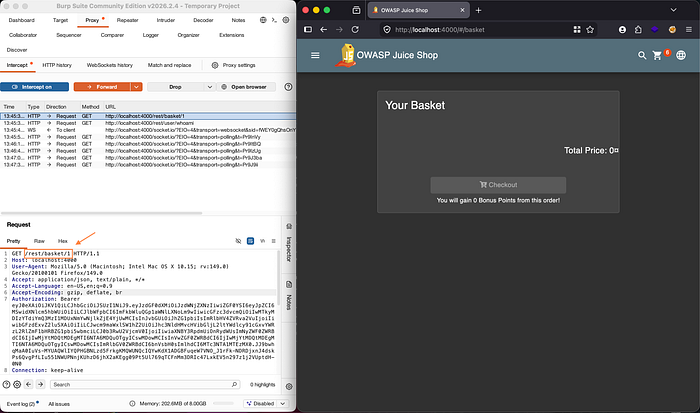
- Forward the request without modifying the ID and observe that the response returns the items in the current user's basket.
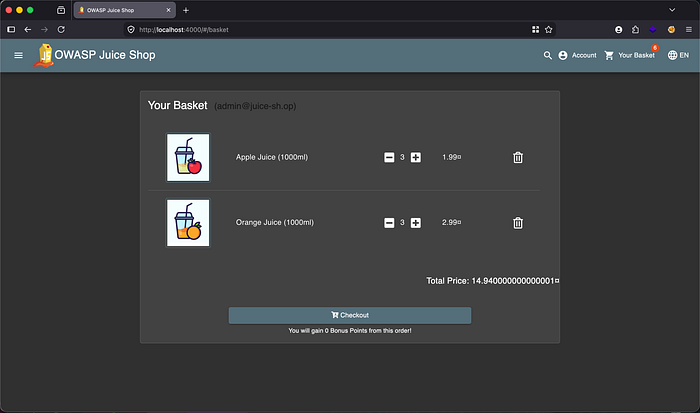
- Return to the homepage, keep intercept enabled, and open the basket again to capture another request.
- Modify the basket ID in the request path to a different value.
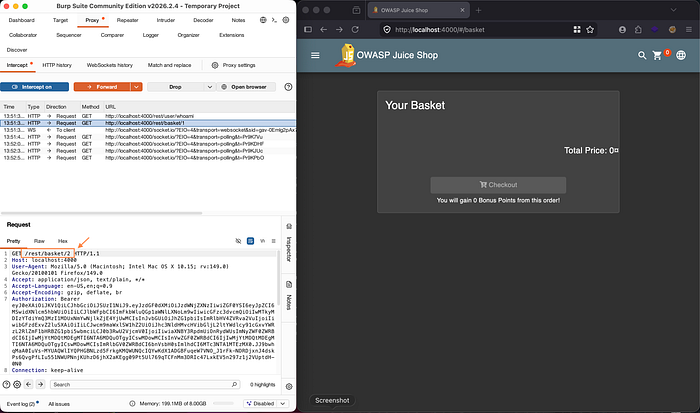
- Forward the modified request and observe that the basket contents change, revealing another user's shopping cart.
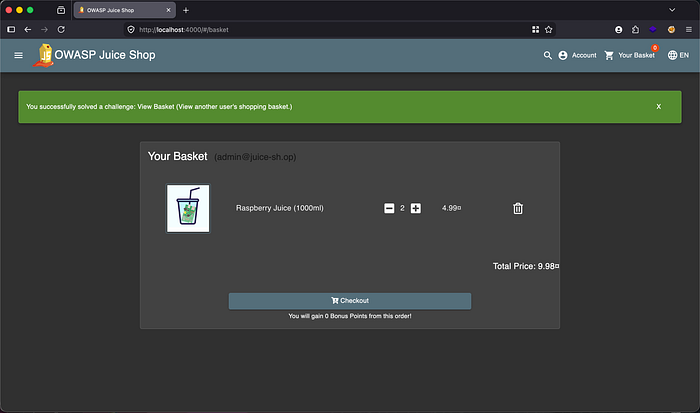
Solution Explained
The solution relies on manipulating the basket ID in the request path to access data belonging to other users. The application retrieves basket information based solely on the identifier provided in the request without verifying whether the user is authorized to access that basket.
This results in an IDOR vulnerability, where changing the object identifier grants access to sensitive user data due to missing access control validation.
Remediation
- Validate every request for sensitive data against the authenticated user session to ensure users can only access their own resources.
- Implement strong access control mechanisms such as role-based or attribute-based access control.
- Avoid relying on direct object identifiers without proper authorization checks.
- Conduct regular security testing to identify and fix broken access control vulnerabilities.

