This lab contains a simple reflected cross-site scripting vulnerability in the search functionality.
To solve the lab, perform a cross-site scripting attack that calls the alert function.
Link: https://portswigger.net/web-security/cross-site-scripting/reflected/lab-html-context-nothing-encoded
Approach: Firstly i am looking for reflected box where which i will giving input and after hit a button this same thing should show anywhere in the page.
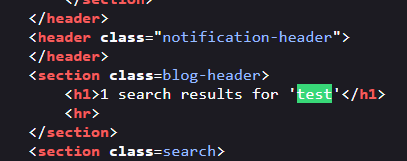
i notice the seach box and search some random things. and found which is i am searching is showing in the page…

then i go to source code and want to where the 'test' is occur.
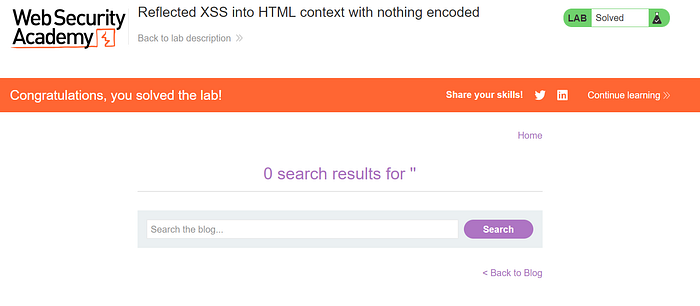
so, now i try the basic payload in search box:
<script>alert('XSS')</script>and after click enter the XSS worked..
and now i go to the source code again and want to how this works..
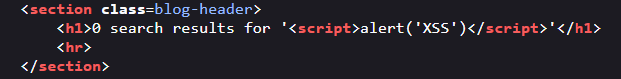
so the searched thing become a script of html because there was not any sanitization.
Thank you. keep coding, keep hacking.