What if the badge your security system uses to identify every employee could be forged by anyone with basic knowledge, and the system would still accept it as genuine? That is not a hypothetical. It is what happens when JSON Web Tokens are implemented incorrectly.
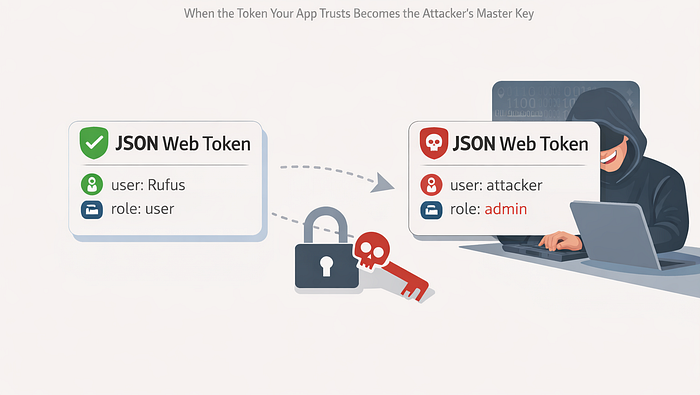
Think of a JWT like a signed permission slip. When you log into an app, the server hands you a note that says, "This is Rufus, he is a verified customer, he logged in at 2 pm0." The app trusts that note on every subsequent request instead of asking you to log in again. Convenient, fast, and efficient, until someone figures out how to forge the note, and the app cannot tell the difference between yours and theirs.
This is not exclusive to financial apps. Any modern web or mobile application using token-based authentication is in scope. SaaS platforms, healthcare portals, logistics systems, HR tools, e-commerce backends, etc, all use JWTs widely. The vulnerability is in how developers implement them, not in the standard itself.
In fintech, the exposure is severe. A forged or manipulated JWT in a payment platform can mean an attacker authenticates as another user, elevates their own role to admin, bypasses transaction authorization checks, or maintains persistent access long after a legitimate session should have expired. All without ever knowing the victim's password.
Technically, JWTs have three parts: 1. Header 2. Payload 3. signature The signature is what makes them trustworthy; it proves the server issued the token and nothing was changed.
The vulnerabilities appear in several well-documented ways. 1. The "none" algorithm attack: JWT headers specify which algorithm was used to sign the token. Some libraries, when they see the algorithm set to "none," skip signature verification entirely. An attacker changes their token's algorithm to "none," modifies the payload to claim admin privileges, and the server accepts it without question. 2. Weak secret keys: If the server signs tokens using HS256 with a short or guessable secret, "secret", "password", or "dev123", an attacker can brute force the signing key offline, then forge any token they want. 3. Algorithm confusion attacks: Some implementations accept both symmetric and asymmetric algorithms. An attacker can switch from RS256 to HS256 and sign the token using the server's public key, which is, by nature, publicly available, tricking the server into accepting a token it never actually issued. 4. No expiry enforcement: A token with no expiration or an expiration set years into the future means a stolen token is valid indefinitely. There is no natural window where the damage stops.
A realistic attack scenario: a developer builds a fintech API during a tight sprint. They use a JWT library with default settings, set the signing secret to the app name, and skip expiry validation because "they will fix it later." An attacker registers, captures their own token, decodes the payload, JWTs are base64 encoded, not encrypted, so anyone can read them, spots a field called "role": "user", brute forces the weak secret in under an hour using freely available tools, re-signs a modified token claiming "role": "admin", and sends it to the API. The server validates the signature, trusts the payload, and grants full administrative access.
Prevention requires getting several things right simultaneously. 1. Always validate the algorithm server-side and explicitly reject "none". 2. Use strong, randomly generated secrets of at least 256 bits for HS256, or prefer RS256 with properly managed key pairs for distributed systems. 3. Set short expiry windows, fifteen to sixty minutes for access tokens, and implement refresh token rotation. 4. Never store sensitive authorization data in the payload without understanding that it is readable by anyone who holds the token. 5. Maintain a token revocation mechanism or blacklist for logout and compromise scenarios. And keep your JWT library updated; several critical vulnerabilities in this space have been patched in popular libraries over the years.
A JWT is only as trustworthy as the implementation behind it. The standard is sound. The shortcuts taken during implementation are where systems break.
Trust in software has to be earned by the architecture, not assumed because a token showed up in the header.
#CyberSecurity #JWT #TokenSecurity #APISecurity #WebSecurity #ApplicationSecurity #FintechSecurity #AuthenticationSecurity #SecureByDesign #OWASP #DevSecOps #SoftwareEngineering #SecurityEngineering #30DaysOfSecurity #CTOInsights