If you use Adobe Acrobat or Reader — and statistically, you almost certainly do — there's a critical vulnerability you need to patch right now. Not next week. Not at the next maintenance window. Today.
The Short Version
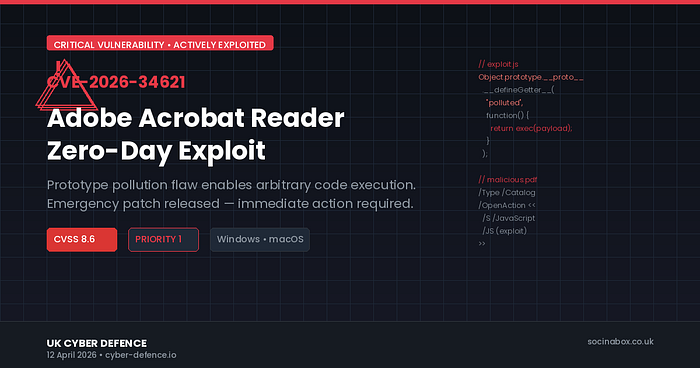
Adobe has issued an emergency security update to address CVE-2026–34621, a prototype pollution vulnerability in Acrobat Reader's JavaScript engine. It carries a CVSS score of 8.6 and allows attackers to execute arbitrary code on your machine simply by getting you to open a malicious PDF.
The critical detail: this vulnerability is being actively exploited in the wild, and evidence suggests attackers have been using it since December 2025.
What Is Prototype Pollution?
For the non-technical reader: PDF files can contain JavaScript code (it's how interactive forms work). Prototype pollution is a technique that lets an attacker manipulate how JavaScript objects behave at a fundamental level. In this case, a carefully crafted PDF can hijack Acrobat's internal processing to run whatever code the attacker wants.
For the technical reader: the flaw (CWE-1321) enables injection of properties into the prototype chain of core objects within Acrobat's JS runtime, which can be leveraged to achieve code execution in the context of the current user.
Who's Affected?
Everyone running unpatched versions of:
- Acrobat DC or Acrobat Reader DC — versions 26.001.21367 and earlier
- Acrobat 2024 — versions 24.001.30356 and earlier
Both Windows and macOS are affected.
What to Do
- Open Acrobat or Reader, go to Help > Check for Updates, and install immediately
- Verify you're on version 26.001.21411 (DC) or 24.001.30362/30360 (2024 track)
- Be cautious with PDF attachments from unknown senders
- Consider disabling JavaScript in Acrobat if you don't need it (Edit > Preferences > JavaScript)
Why This Matters
PDF-based attacks remain one of the most effective entry points for threat actors. We trust PDFs implicitly — invoices, contracts, reports all arrive as PDFs — and that trust is exactly what attackers exploit. This particular vulnerability is especially concerning because of the extended period it was used before a patch was available.
Further Reading
We've published detailed analyses tailored to different audiences:
- Adobe Acrobat Under Attack: What Every Small Business Needs to Do Right Now — practical, risk-focused guidance without the jargon.
Stay safe out there. Patch your software, question unexpected attachments, and remember that the most dangerous threats are often hiding inside the files you trust the most.