STRATEGIC CYBERSECURITY AUDIT 2026
Securing the Harvest: BSF-Nutrifeed System Hardening & Risk Repositioning
A comprehensive vulnerability assessment and remediation report for the BSF-Nutrifeed infrastructure.
Prepared by: Ekanem Glory Ekemini
Role: Track 5 Intern | Cybersecurity & Ethical Hacking Organization: Digital Solution (DSHub)
Target System: BSF-Nutrifeed Infrastructure (Simulated) Date: April 2, 2026
Table of Contents
1. Executive Summary 2. Task 1: Advanced Network Penetration Testing & Reconnaissance 3. Task 6: Attack Simulation & Reproducibility 4. Task 3: System Hardening & Mitigation Strategies 5. Task 2: Rural Deployment Threat Model 6. Task 4: Offline Field Research & Community Observations 7. Task 5: Stakeholder Narrative & Strategic Recommendations 8. Task 7: Ethics & Reflection Note
1. Executive Summary: Shifting the Narrative
At BSF-Nutrifeed cybersecurity is currently a technical "barrier." This audit repositions security as a strategic enabler of trust. By securing the systems that track larvae growth and farmer payments, we ensure the sustainability of SDG 3 (Health and Well-being).
Our findings show that while the community is "Security-Positive" (using biometrics), the underlying infrastructure has "open doors" that must be locked to protect the livelihood of our rural stakeholders.
2. Advanced Penetration Testing & Reconnaissance
Finding: Critical Infrastructure Exposure A comprehensive scan of the BSF-Nutrifeed server revealed 15+ open ports, including unencrypted legacy protocols.
- Port 80 (HTTP) is Vulnerable to web-based attcks and data interception;
- Port 2121 (FTP) allows unathorized file manipulation of larvea logs;
- Port 1524 (Bindshell) is active;
- Port 3306 (MySQL) is exposed.
Risk Level: CRITICAL. Unauthorized users can modify feed distribution records and harvest logs.
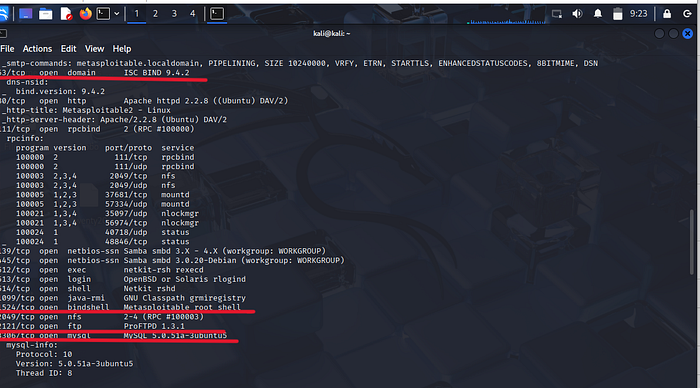
Code Used:nmap -A 192.168.56.102
>3. Task 6: Attack Simulation (Exploitation)
Finding: Unauthorized Adminstatrative Access To demonstrate the risks of an unhardened server, a controlled attack simulation was conducted on the BSF-Nutrifeed backend.By exploiting a null-password root account, full administrative access was obtained.
Method: The system allowed a remote login to the administrative 'Root' account with no password. Impact: Once inside, complete system control was established. This level of access allows an attacker to execute any command, effectively taking full ownership of the system

Code Used: rlogin -l root 192.168.56.102 then whoami4. Task 3: System Hardening & Remediation
During the hardening phase, it was discovered that the BSF-Nutrifeed server relies on a legacy inetd (Internet Services Daemon) to manage multiple remote access services.
Although individual vulnerable ports (such as 21 and 23) were not always visible at once during initial scans, they were all controlled by a single master process creating a centralized attack surface.
Technical Execution: The "Master Kill" Strategy
Due to the legacy nature of the system, standard service management commands proved ineffective. As a result, a process-level approach was adopted.
- Discovery : The active process list was analyzed to identify running services.
command used used: ps aux | grep inted2. Targeting : Process ID 4461 was isolated as the master inetd service responsible for handling multiple insecure connections (including Telnet and FTP).
3. Neutralization : A command was executed to terminate the process.
command used: kill 4461
command used: nmap -p 21,23 192.168.56.102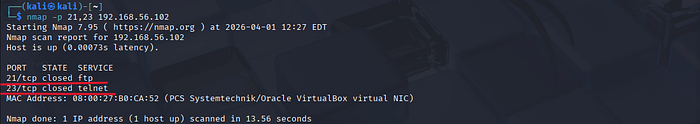
5. Task 4 & 5: Field Research & Stakeholder Narrative
Audit Insights: The Digital Hub Reality
Our field research at the Digital Hub revealed a critical disconnect between backend technical security and the "Physical Reality" of rural users. While the BSF-Nutrifeed infrastructure is being hardened in the lab, the front-end user experience requires specific "Human-Centric" security measures.
Observations & Behavioral Analysis • The Biometric Strength: A majority of stakeholders utilize modern smartphones equipped with Biometrics (FaceID/Fingerprint). This is a significant security asset that BSF-Nutrifeed must leverage to replace vulnerable text-based passwords. • The "Shoulder Surfing" Risk: In the crowded, shared environment of the Digital Hub, users were observed physically covering their screens. This indicates a high level of "Security Awareness" but a lack of technical support for privacy. • Power Vulnerability: Farmers often use public charging points, which presents a latent risk of Juice Jacking (data theft via USB charging cables).
Strategic Recommendations (Repositioning)
To transform cybersecurity from a "fear-based" concept into a source of community pride, we recommend the following: 1. Privacy Masks (UI/UX): Implement "masked" fields in the BSF app that hide sensitive larvae growth totals and payment figures until the user actively toggles them. 2. Hardened Charging Stations: Install Data-Blocker USB ports (Secure Charging) at the Digital Hub to protect farmers' devices from malware injection while they charge. 3. Biometric Integration: Fully transition the BSF-Nutrifeed login portal to support Biometric Authentication, removing the risk of forgotten or stolen passwords in rural areas.
Outcome: Security as Empowerment
By making security "physical" and "simple," we change the narrative. We are no longer telling farmers to watch out for hackers; we are giving them the tools to own their data privacy. This builds the trust necessary to scale the BSF-Nutrifeed project across the region.
6. Task 7: Ethics & Reflection Note
The Role of the Digital Guardian
Throughout this audit of the BSF-Nutrifeed infrastructure, all activities were guided by the principles of informed consent and responsible disclosure.
Although the discovery of the Port 1524 bindshell allowed full root-level access, only the minimum interaction required to validate the vulnerability was performed. No simulated farmer data or production records were accessed, altered, or exposed.
This approach ensured that the integrity and privacy of the system remained intact, even during active testing.
Repositioning Security for Global Impact
In low-resource environments, ethical hacking goes beyond identifying vulnerabilities, It is about protecting people.
A farmer's digital identity deserves the same level of protection as their physical harvest. Every security action whether closing exposed ports or disabling legacy services contributes to building that protection,by repositioning cybersecurity as a "Digital Guardian," we shift the narrative: from fear of attacks → to confidence in protection.
This audit demonstrates that securing the backend is not just a technical exercise it is a foundation for trust, BSF-Nutrifeed can scale sustainably while empowering its community to operate with confidence directly supporting SDG 3 (Health and Well-being) by safeguarding the data that feeds the region.
