A Forensic Journey from Legacy Shared Hosting to the CKA Path
It started late one evening. Several sites had just launched when the nightmare began: our WordPress sites turned into the "White Screen of Death" and began redirecting visitors to shady shopping sites. As a Web Server Admin, I knew this wasn't a simple glitch — it was a coordinated attack.🚩
Leveraging my background from the Google Cybersecurity Professional Certificate, I dove into the forensic investigation to uncover what I now call "Zombie" behavior.🧟♂️
☣️ 1. The Anatomy of the Attack
The malware wasn't just malicious; it was resilient. Here is what I uncovered during the investigation:
<?php
goto T7Bkn; foHGP: $_SESSION["\x64\x6f\x61\143\x74"] = $hmH20;
goto TQt0_; K0ZxZ: nRhhK(array("\167\x65\142" => $EuisC));
goto q1fwC; AE8KZ: BD64p:
/* ... 2,000+ lines of obfuscated code omitted ... */"I found this 'Spaghetti Code' inside a core WordPress file. Notice the heavy use of goto and hex encoding—classic signs of an obfuscated backdoor."
- Zombie Persistence🔄 (Self-Healing): The malware used a "Guardian Script." Every time I deleted
.htaccessorindex.php, they were reborn instantly. - Kernel-Level Lock🔒 (
chattr +i): The attacker used the Immutable attribute to lock the malware files. Even as the file owner, I received "Permission Denied" when trying to delete them. - Lateral Movement🦠: It started from one "Patient Zero" (the weakest site) and spread horizontally across all 22 domains in the shared hosting environment.
- Cloaking & Stealth🕵️♂️: The payloads were hidden inside
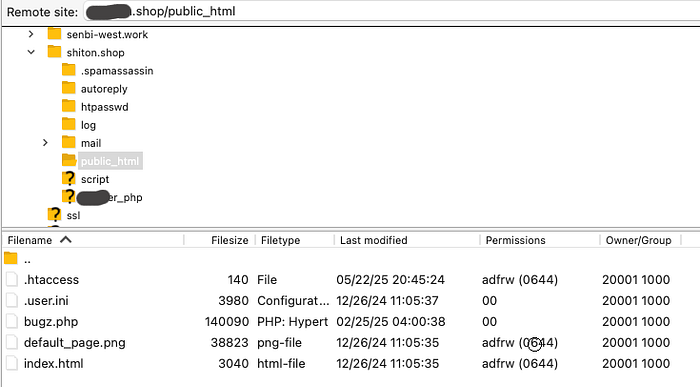
.pngfiles, fake CSS, and used typosquatting (e.g.,wp-confiq.php) to bypass standard scanners.
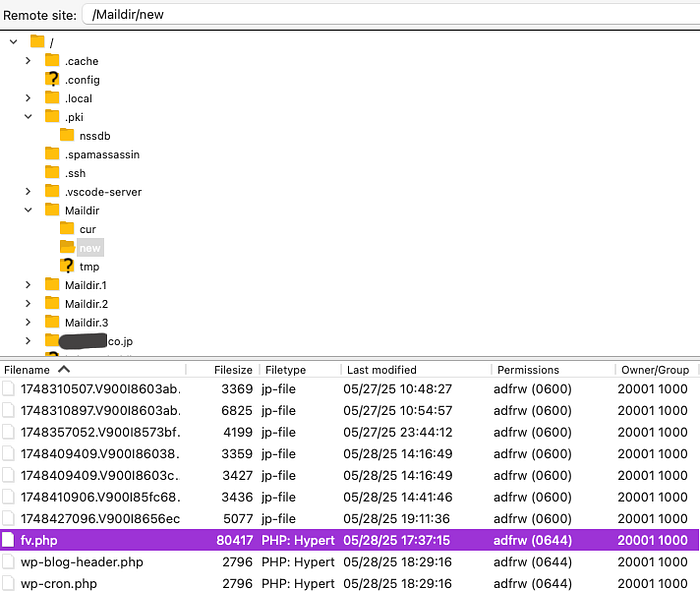
The attacker's command center found hidden within the directory. It provides full control over the server environment.
💡 The AI Advantage: To speed up the investigation, I used Gemini Thinking to help scan and analyze suspicious code patterns. It acted as a "Force Multiplier," helping me identify obfuscated PHP backdoors and unauthorized SSH keys hidden within thousands of lines of code that automated scanners had missed.
🛠️ 2. The Tactical Response: Breaking the Loop
Since I lacked Root Permission on this shared hosting , I had to get creative with the tools available:
- The Freeze Strategy (Neutralization)❄️: Since I couldn't unlock the files immediately, I "froze" them. I applied
chmod 0000to the malicious scripts, stripping all permissions. This broke the Guardian Script's execution loop and stopped the self-healing process. - The Nuclear Option (Eradication)☢️: Because the infection was so widespread, manual cleanup wasn't enough. I executed a "Domain Initialization" to wipe the environment and reset it to a verified Clean Baseline.
- Credential Purge🔑: To ensure the actor was completely locked out, I performed a 100% Credential Rotation, refreshing all Database passwords, FTP accounts, and WordPress Security Salts to kill any active sessions.
🛡️ 3. The Path Forward: From Shared Hosting to Cloud-Native
This incident was my "Catalyst."⚡ It exposed the inherent limitations of shared hosting — specifically the lack of Root access and network-level control.
- Immediate Hardening🛡️: I have since enforced Zero-Trust at the application level, disabling file editors and using strict
.htaccesspolicies to block PHP execution in high-risk directories. - The CKA Roadmap☸️: This experience pushed me toward the Certified Kubernetes Administrator (CKA) path. My goal is to move our infrastructure to a hardened AWS/Kubernetes environment.
- Policy-Driven Security⚖️: I am shifting from "manual file-chasing" to Policy-Driven Security. By mastering Kubernetes NetworkPolicies, I am preparing to build a future where we can programmatically isolate compromised workloads and block malicious traffic at the source.
"The Malware had its Guardian Script, but I had a plan, Gemini, and the determination to build something better."
#Cybersecurity #MalwareRemoval #WordPress #CloudNative #AIinSecurity
Disclaimer:
This article summarizes my real-world hands-on experience as a Web Server Admin. To ensure technical accuracy and provide the best reading experience, AI assistance (Gemini) was utilized for scanning malicious code patterns during the actual incident, as well as for grammatical polishing and structural organization of this article.