When people see bug bounty payouts on social media, it often looks like researchers start hunting and immediately begin earning. The reality is very different.
Behind every bounty there are months of learning, failed reports, duplicates, and a lot of frustration.
This is the honest story of my journey, from attending security meetups and learning from the community to finally earning my first 3-digit bounty.
How My Cybersecurity Journey Started
I am currently pursuing BCA (Hons.) in Computer and Information Science in Ahmedabad and have been deeply interested in offensive security and web application testing.
In the beginning, cybersecurity felt overwhelming. There were:
- Too many tools
- Too many vulnerabilities
- Too many tutorials
Instead of jumping directly into bug bounty programs, I decided to focus on understanding the fundamentals of web security first. I started learning about:
- HTTP requests and responses
- Authentication and session handling
- Access control logic
- Common web vulnerabilities
To practice these concepts, I spent a lot of time solving labs on platforms like PortSwigger Web Security Academy and PentesterLab, which helped me understand vulnerabilities such as XSS, access control issues, IDOR, web cache related attacks, and more.
At this stage I realized an important truth:
Bug bounty hunting is not about tools. It is about understanding how applications work and where developers make mistakes.
Learning Through Practice
To strengthen my practical skills, I also practiced on multiple hands-on platforms. On PentesterLab, I completed badges including:
- UNIX
- HTTP
- Essentials
- Recon
These labs helped me understand how HTTP works in real environments, how APIs behave, and how authentication or authorization flaws appear in applications.
I also spent time solving HackTheBox machines, which helped me practice enumeration, exploitation, and privilege escalation techniques.
All of this practice helped build the mindset needed for real security testing.
My First Security Conference - BSides Ahmedabad 2024
One of the most important moments in my journey was attending BSides Ahmedabad in October 2024. It was my first time attending a cybersecurity conference and meeting real researchers from the community.
I met many amazing people and had the opportunity to interact with @GodfatherOrwa, whose insights into bug bounty and security research were incredibly valuable.
Events like this made me realize how strong and supportive the cybersecurity community can be. Meeting researchers in person, listening to their experiences, and discussing ideas gave me a lot of motivation to continue learning.
The NULL Ahmedabad Meetup That Changed Everything
Another major turning point came on 4 September 2025, when I attended a NULL Ahmedabad monthly meetup.
During this meetup, the Barracks team organized a live hacking event called "Warzone." This event was extremely valuable for beginners like me.
During the session, they explained how real bug bounty hunting works, including:
- How to approach targets
- How to properly validate vulnerabilities
- How to write clear and effective bug reports
- Why impact matters more than just finding a bug
Until then, I already knew several vulnerabilities like:
- Cross-Site Scripting (XSS)
- Insecure Direct Object Reference (IDOR)
- Information Disclosure
- Other common web vulnerabilities
But the event helped me understand something much more important: How to turn a vulnerability into a proper bug bounty report.
Going Home and Starting the Hunt
As soon as the NULL meetup ended, I went back home and immediately started hunting.
I applied what I had learned during the event and started testing different targets. Within a short time, I discovered multiple vulnerabilities including:
- Cross-Site Scripting
- IDOR
- Information disclosure issues
- Other security misconfigurations
In total, I found around 12–13 vulnerabilities. However, bug bounty reality quickly showed up again. Some reports were marked as:
- Duplicate
- Already known issues
But that's part of the process. Every report teaches you something.
Winning the Barracks Warzone Challenge
On 6 September 2025, the results of the Barracks Warzone challenge were announced.
To my surprise, I secured Rank #1.
Winning the challenge earned me a student pass for BSides Ahmedabad 2025, which was an amazing opportunity to attend the conference again and connect with more researchers.
I am truly grateful to the Barracks team for organizing such an event and giving beginners like us a chance to learn and compete.
BSides Ahmedabad 2025
In 2025, I attended BSides Ahmedabad again.
During the event, I had another great opportunity to meet @GodfatherOrwa and had an interesting conversation about bug bounty and startups.
His talk on AI and the Internet was particularly insightful and gave a new perspective on how security and technology are evolving.
The event ended with the Standoff Bug Bounty Hacks party, and the overall experience was incredible. These community experiences played a huge role in shaping my cybersecurity journey.
Growing Through Professional Experience
During my learning journey, I also got the opportunity to work as an Offensive Security Trainee at Sudarshana Labs.
The Sudarshana blog contains deep technical writeups, real-world security research, and insights into offensive security practices. It covers topics such as vulnerability discovery, attack surface exploration, bug bounty case studies, and practical security experimentation.
Being part of a professional security environment helped me strengthen my practical understanding of real-world web application security testing.
At Sudarshana Labs, I upskilled myself on:
- Web application security testing
- BurpSuite Professional
- Walking through real-world findings from mentors
- Reporting Standards
This experience helped me better understand how structured security assessments are performed in production-like environments and how professional teams approach vulnerability discovery.
I am proud to be part of Sudarshana Labs and grateful for the opportunity to learn under such guidance.
The Reality of Bug Bounty Hunting
Before getting my first bounty, I submitted multiple vulnerability reports. Many of them were rejected as:
- Duplicate
- Informational
- Not applicable
At one point I had 4–5 rejected reports in a row. That stage is where many beginners quit bug bounty. But those failures taught me something extremely important: Finding a vulnerability is not enough.
You must clearly demonstrate:
- The impact
- How it can be exploited with proof
- Clear reproduction steps
Bug bounty programs reward clear thinking and strong reporting, not just random findings.
Finally… My First 3-Digit Bounty
After months of learning, practicing, submitting reports, and facing rejections…
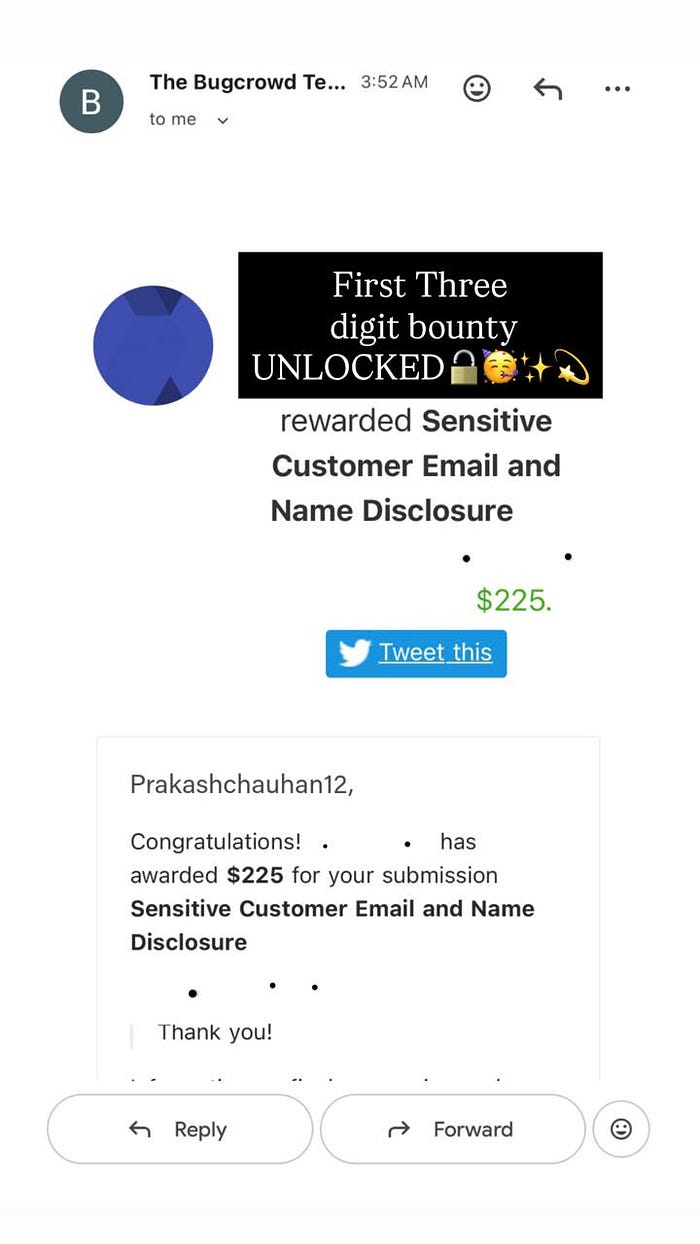
One report finally worked.
The vulnerability was validated by the program and resulted in my first 3-digit bug bounty reward.
That moment felt amazing not just because of the reward, but because it proved that all the effort and persistence were worth it.
Lessons From My Journey
If you are starting bug bounty today, here are a few lessons from my experience:
- Focus on fundamentals first Understanding HTTP and application logic is more important than tools.
- Practice on labs Platforms like PortSwigger and PentesterLab are extremely valuable.
- Expect rejections Duplicates and "Not Applicable" responses are normal.
- Engage with the community Meetups, conferences, and CTFs can accelerate learning dramatically.
- Persistence matters the most Bug bounty rewards people who keep going even after failures.
Final Thoughts
Your first bounty might take longer than you expect. But if you continue learning, testing, and improving your reports, the results will eventually come.
For me, that result was my first 3-digit bounty.
And this is just the beginning of the journey.
