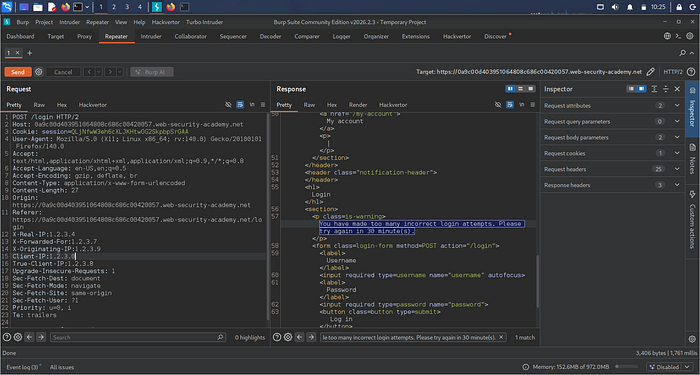
After multiple failed login attempts, the application responded with:
"You have made too many incorrect login attempts. Please try again in 30 minute(s)."
At first glance, the control appeared effective. The system enforced a lockout and prevented further attempts.
However, after modifying a small part of the request, the restriction no longer applied.
This raised a critical question:
How reliable is rate limiting if request attribution can be manipulated?
Rate limiting is a widely adopted defense mechanism in authentication systems. It is designed to reduce the effectiveness of brute-force and credential stuffing attacks by restricting repeated login attempts.
In this analysis, conducted within a controlled lab environment using Burp Suite, I evaluated how a rate-limiting control behaves under adversarial conditions and whether it can be bypassed through manipulation of request metadata.
The Observed Control
The application implemented a lockout mechanism triggered after multiple failed login attempts. The behavior was consistent:
- Repeated failed attempts resulted in a temporary account restriction
- A defined cooldown period was enforced
- The system returned a clear lockout message
At a functional level, this aligns with standard rate-limiting practices.
Visual Analysis

Analytical Approach
To understand how the system enforced rate limiting, I focused on identifying the parameter used to track repeated requests.
In many web architectures, especially those involving reverse proxies or load balancers, applications rely on HTTP headers to determine the client's originating IP address.
This led to the hypothesis that the system might depend on client-supplied headers for request attribution.
Testing Request Attribution
The following headers were introduced and modified during testing:
X-Forwarded-ForX-Real-IPX-Originating-IPClient-IPTrue-Client-IP

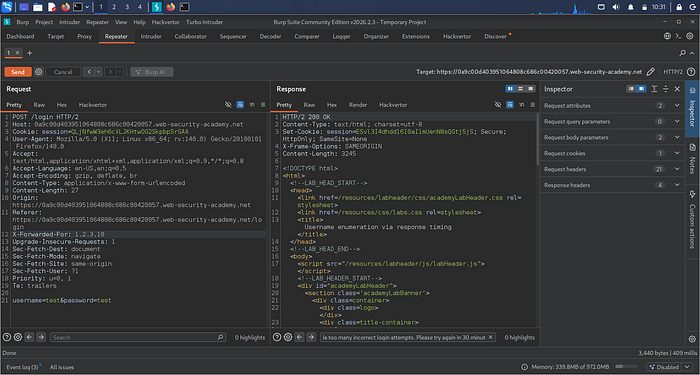
These headers are commonly used to forward client IP information across intermediary systems. However, they are part of the HTTP request and can be altered if not properly validated.
Key Finding
After modifying these headers, the application responded differently to subsequent requests.
The rate-limiting restriction no longer applies under certain conditions, indicating that:
- The application relied on header values to determine the request origin
- These values were not strictly validated
- Request attribution could be influenced by client-controlled input
This demonstrates a fundamental issue: Security decisions were based on untrusted data.
Security Implications
This behavior introduces several risks:
1. Trust Boundary Violation
The system trusted data originating from the client rather than enforcing validation at a trusted layer.
2. Ineffective Rate Limiting
If the request origin can be altered, rate limiting cannot reliably restrict repeated attempts.
3. Increased Attack Surface
Attackers can manipulate request metadata to test and potentially evade security controls.
Recommended Mitigations
To strengthen rate-limiting implementations:
Enforce Trusted Attribution
- Use server-observed IP addresses
- Only trust forwarded headers from verified proxies
- Sanitize and validate all incoming header values
Apply Layered Controls
- Combine IP-based and account-based rate limiting
- Implement progressive delays (e.g., exponential backoff)
- Enforce Multi-Factor Authentication (MFA)
Improve Monitoring
- Detect inconsistent or rapidly changing client identifiers
- Log and analyze anomalous authentication patterns
- Trigger alerts on suspicious behavior
Who This Is For
This analysis is particularly relevant for:
- Backend developers implementing authentication systems
- Security engineers reviewing access control mechanisms
- Students and practitioners learning web application security
Key Takeaway
The effectiveness of rate limiting depends on the integrity of the data used to enforce it.
If the request attribution relies on untrusted input, the control becomes unreliable and susceptible to bypass.
This case highlights an important principle in application security:
Controls must not only exist, but they must also be implemented within the correct trust boundaries.
Rate limiting remains a critical defense mechanism, but without proper validation of request origin, its effectiveness can be significantly reduced.