Your bank account, your medical records, your private messages all protected by encryption that quantum computers will shatter. Here's how today's encryption works, why it's about to fail, and what replaces it.
Every password you've ever entered, every credit card transaction, every "secure" message you've sent all of it is protected by encryption that will become obsolete the moment quantum computers become powerful enough. And here's the truly terrifying part: adversaries are already collecting your encrypted data today, betting they'll be able to decrypt it tomorrow.
The Ticking Time Bomb Nobody's Talking About
Imagine you're storing your most valuable possessions in a vault. The lock is so complex that it would take every computer on Earth working together for billions of years to crack it. You sleep soundly, knowing your secrets are safe. Now imagine someone tells you: "In about 10 years, someone will invent a tool that can open that lock in 10 seconds." That's not science fiction. That's the reality of our digital world right now.
This isn't a theoretical worry discussed only at academic conferences. Right now, today, every piece of data you send over the internet your banking credentials, your health records, your company's trade secrets is protected by mathematical problems that quantum computers will solve trivially. The strategy adversaries are already executing is called "Harvest Now, Decrypt Later": capture encrypted traffic today, store it cheaply, and wait for quantum computers to hand you the keys.
Before we can understand why everything is about to break, we need to understand how the encryption protecting you right now actually works. Let's build that foundation step by step.

RSA Encryption: The Mathematical Padlock
RSA is the workhorse of modern internet security. Invented in 1977 by Rivest, Shamir, and Adleman, it underpins everything from HTTPS to secure email. To understand RSA, think of it as a magical padlock that anyone can snap shut but only you have the key to open.
How the Public-Private Key Pair Works
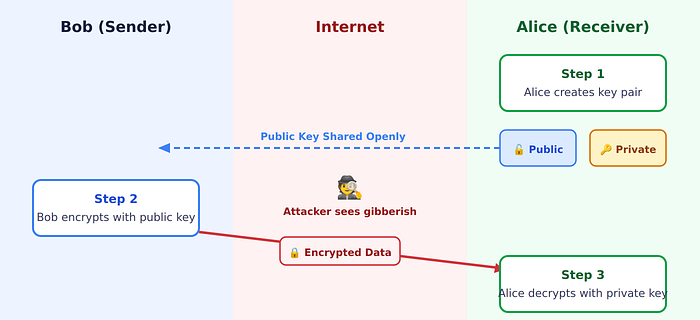
Imagine you want someone to send you a secret message. You create two mathematically linked keys: a Public Key (the open padlock you give to everyone anyone can use it to lock a box containing their secret) and a Private Key (the unique key you guard with your life only this key can open boxes locked with your public key).
The Maths That Makes It Work
The genius of RSA lies in a deceptively simple mathematical truth: multiplying two large prime numbers is trivial, but factoring the product back into those primes is astronomically hard. This asymmetry is called a "trapdoor function" easy in one direction, nearly impossible in reverse.
Consider a quick example to build intuition. Multiplying 3 × 5 = 15 is instant. Asking "what two primes multiply to give 15?" is still easy because the number is small. But now try: what two primes multiply to give 2,329? That's already harder you'd need to try many combinations (the answer is 17 × 137). Now scale this to a 617-digit number, and even all the world's classical computers working together would need longer than the age of the universe to factor it.
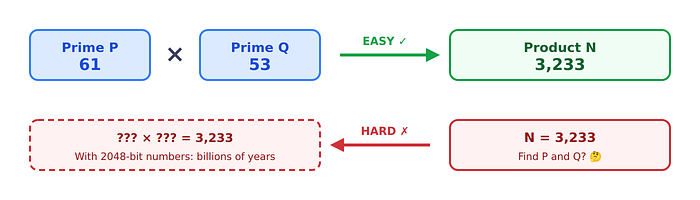
RSA uses numbers that are typically 2048 or 4096 bits long numbers so colossal that factoring them is computationally impossible for any classical computer. Your online banking, every HTTPS website, and most secure email protocols all rely on RSA or closely related schemes. It's been the bedrock of internet security for nearly 50 years.
Elliptic Curve Cryptography (ECC): The Elegant Alternative
If RSA is the reliable sedan of cryptography, ECC is the sports car achieving the same security level with dramatically smaller keys, faster operations, and lower power consumption. Instead of relying on prime factorization, ECC is built on the mathematics of elliptic curves: special curved lines described by equations of the form y² = x³ + ax + b.
The Twisty Slide Analogy: Imagine a curved slide at a playground. If I tell you "start at point A and slide down to point B," that's straightforward. But if I only show you point B and ask "where was point A?" that's nearly impossible because the slide is so twisty. This is the Elliptic Curve Discrete Logarithm Problem (ECDLP): going forward (point multiplication) is easy, but going backward is computationally infeasible.
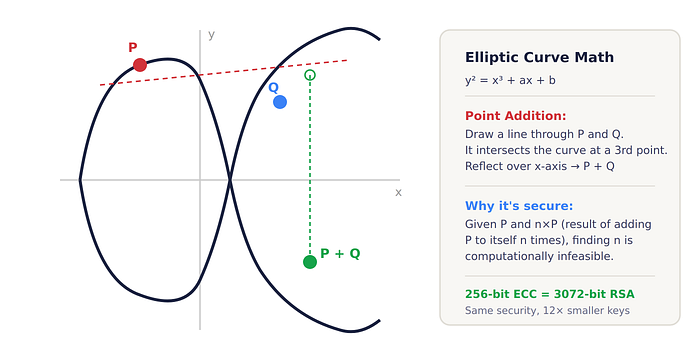
The beauty of ECC is efficiency: a 256-bit ECC key provides equivalent security to a 3072-bit RSA key. This means smaller key sizes, faster computations, and lower power consumption which is why ECC powers most modern secure protocols including Signal messaging, Bitcoin wallets, the TLS that secures every HTTPS connection, and (until recently) Apple iMessage.
AES: The Symmetric Encryption Workhorse
While RSA and ECC are asymmetric (different keys to lock and unlock), AES (Advanced Encryption Standard) is symmetric the same key both encrypts and decrypts. Think of it like a traditional physical key: if you and I both have copies of the same key, we can both lock and unlock the same door.
AES is blazing fast and is used to encrypt virtually all bulk data: your files, your hard drive (BitLocker, FileVault), VPN traffic, and Wi-Fi connections (WPA2/WPA3). But if both parties need the same key, how do they securely share it across the internet without someone intercepting it?
The Hybrid Approach: Best of Both Worlds
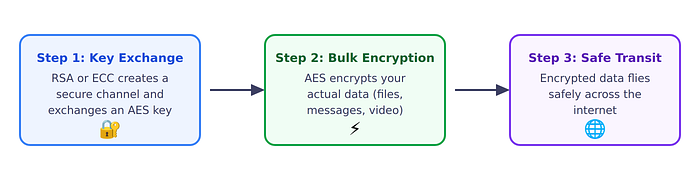
This hybrid approach gives you the best of both worlds: the secure key-exchange capability of asymmetric encryption (RSA/ECC) and the raw speed of symmetric encryption (AES). It's elegant, efficient, and has served us well for decades. But here's the problem: the entire security of this system depends on RSA or ECC remaining unbreakable. And that's about to change.
The Quantum Threat: Why Everything Is About to Break
Classical Bits vs. Quantum Qubits
Classical computers use bits switches that are either 0 or 1, like a coin showing heads or tails. Quantum computers use qubits (quantum bits), which exploit a property called superposition to exist as 0, 1, or both simultaneously. Combined with entanglement (where qubits become correlated across distance), this allows quantum computers to explore many computational paths in parallel.
The Library Analogy: Imagine searching for a specific book in a massive library. A classical computer checks each book one at a time it might get lucky, but worst case it checks every single shelf. A quantum computer can effectively explore many shelves simultaneously, finding the answer exponentially faster for certain types of problems. Crucially, factoring large numbers is exactly one of those problem types.

Shor's Algorithm: The RSA and ECC Killer
In 1994, mathematician Peter Shor at Bell Labs published what would become the most consequential algorithm in the history of cryptography. Shor's algorithm, when run on a sufficiently powerful quantum computer, can factor large numbers exponentially faster than any known classical algorithm. It doesn't just make factoring "a bit faster" it transforms the problem from one requiring billions of years into one requiring hours or days.
To appreciate why this is devastating, recall the trapdoor function that RSA depends on: multiplying two large primes is easy, but factoring the product back into those primes is astronomically hard. Shor's algorithm blows that door wide open. And it doesn't stop at RSA the algorithm (with slight modifications) also solves the discrete logarithm problem, which means ECC is equally doomed.
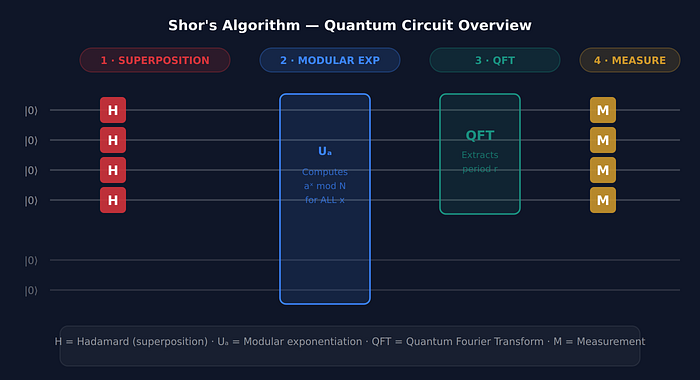
The Quantum Circuit Inside Shor's Algorithm
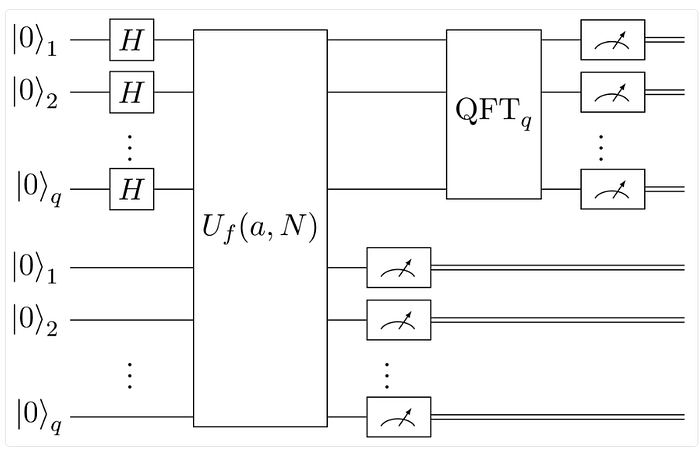
Breaking down the circuit:
- Hadamard Gates (H): Put qubits into superposition (0 and 1 simultaneously)
- Modular Exponentiation (Uf): The mathematical heart calculates a^x mod N
- Inverse Quantum Fourier Transform (QFT^-1): Extracts the hidden period from quantum interference
- Measurement: Collapses the quantum state to give us the period
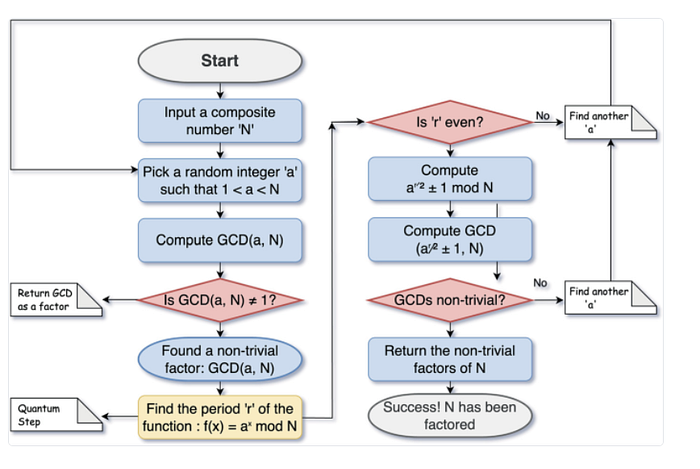
How Shor's Algorithm Actually Works Step by Step
Shor's algorithm is a beautiful piece of mathematics that combines classical number theory with quantum mechanics. The core insight is this: factoring a large number N can be reduced to the problem of finding the period of a function and quantum computers are extraordinarily good at finding periods. Let's walk through the process in plain language, then visualize each stage.
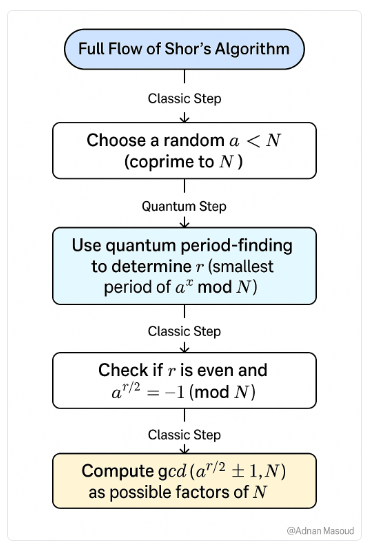
Step 1: Reduce Factoring to Period-Finding
Suppose we want to factor the number N (say, N = 15 for simplicity). Shor's algorithm starts by picking a random number a that's less than N and shares no common factors with it (for example, a = 7). Now consider the function f(x) = aˣ mod N that is, raise 7 to increasing powers and take the remainder when dividing by 15. The results cycle: 7, 4, 13, 1, 7, 4, 13, 1, ... The sequence repeats with a period r = 4. This periodicity is the key that unlocks factoring.
The Musical Analogy: Think of period-finding like identifying the tempo of a song. If you hear a repeating drumbeat pattern, you can figure out the rhythm (period) even in a noisy room. A classical computer would have to listen to each beat one at a time, potentially for billions of beats. A quantum computer can use the Quantum Fourier Transform to "hear" all the beats simultaneously and identify the rhythm almost instantly like having perfect pitch for mathematical patterns.
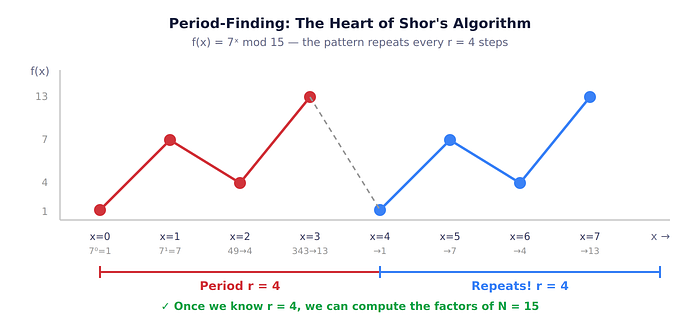
Step 2: The Quantum Fourier Transform (QFT)
Here's where quantum mechanics enters. Finding the period of f(x) = aˣ mod N classically is essentially as hard as factoring N itself you'd have to compute the function for a huge number of values of x and look for the pattern. But a quantum computer can evaluate f(x) for all values of x simultaneously using superposition, then apply the Quantum Fourier Transform to extract the period in a single operation.
The QFT is the quantum analog of the classical Discrete Fourier Transform. In classical signal processing, the Fourier Transform decomposes a signal into its constituent frequencies. The QFT does the same thing to a quantum state: it transforms a superposition of computational basis states into a superposition of frequency components, making the period of the underlying function "pop out" as a peak in the frequency domain.
Step 3: From Period to Factors
Once we know the period r, classical math takes over. If r is even (which it is with high probability), then we compute a^(r/2) − 1 and a^(r/2) + 1, and the factors of N are found by taking the greatest common divisor (GCD) of these values with N. In our example: a = 7, r = 4, so we compute GCD(⁷² − 1, 15) = GCD(48, 15) = 3, and GCD(⁷² + 1, 15) = GCD(50, 15) = 5. The factors of 15 are 3 and 5. Done.

Why It's So Devastating for RSA and ECC
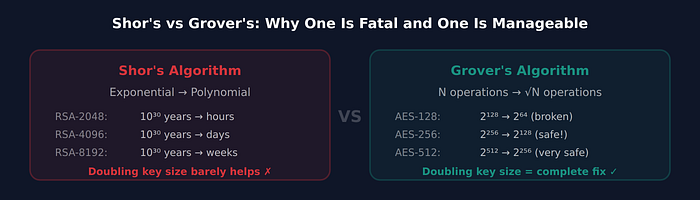
The key mathematical insight is that Shor's algorithm converts factoring from an exponential-time problem (2ⁿ operations on classical hardware) to a polynomial-time problem (roughly n³ operations on quantum hardware). For RSA-2048, that's the difference between 1⁰³⁰ years and a few hours. The same period-finding approach, when applied to the discrete logarithm problem over elliptic curves, breaks ECC with similar efficiency.
The critical takeaway: Shor's algorithm isn't a brute-force attack. It's a fundamentally different approach that exploits quantum parallelism to find hidden mathematical structure. There is no way to "patch" RSA or ECC against it doubling the key size doesn't help, because Shor's algorithm scales polynomially. RSA-4096 offers only marginally more resistance than RSA-2048 against a quantum adversary.
Complete Quantum Factoring Process
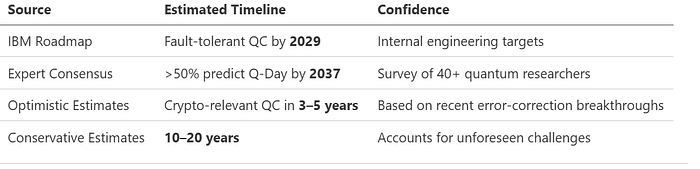
When Will It Happen? The Q-Day Timeline
The critical question: when will a quantum computer be powerful enough to actually run Shor's algorithm against real-world key sizes? Current quantum computers have reached roughly 1,000+ physical qubits (IBM's Condor), but they're extremely error-prone. Breaking RSA-2048 requires approximately 4,000 logical qubits and each logical qubit may need thousands of physical qubits for error correction.
Grover's Algorithm: The Universal Search Accelerator
While Shor's algorithm is a precision weapon against asymmetric cryptography (RSA, ECC), Grover's algorithm (1996, by Lov Grover at Bell Labs) is more of a universal power tool. It doesn't target any specific mathematical structure instead, it accelerates any unstructured search problem with a quadratic speedup. That might sound less dramatic than Shor's exponential speedup, but it has profound implications for symmetric encryption like AES.
The Core Idea: Searching a Haystack Faster
The Phone Book Analogy: Imagine you have a phonebook with 1 million entries, and you need to find the one person with a specific phone number (not name so the book's alphabetical order doesn't help). A classical computer would have to check entries one by one — on average 500,000 checks, worst case 1,000,000. Grover's algorithm on a quantum computer can find the entry in roughly √1,000,000 = 1,000 checks. That's a 1,000× speedup. Now apply this to cryptographic keys, where the "phonebook" has ²¹²⁸ or ²²⁵⁶ entries.
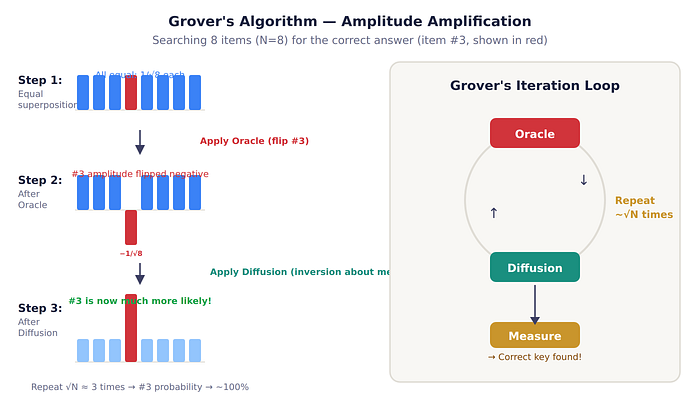
How Grover's Algorithm Works Step by Step
Grover's algorithm is built on two elegant quantum operations repeated in a loop: the Oracle (which marks the correct answer) and the Diffusion Operator (which amplifies the probability of measuring that answer). Together, they gradually "rotate" the quantum state toward the solution.
Step 1: Start with Equal Superposition. We begin by putting all n qubits into an equal superposition using Hadamard gates giving every possible key in the search space an equal probability of being measured. If we're attacking AES-128, this means all ²¹²⁸ possible keys are represented simultaneously. At this point, the probability of measuring the correct key is 1/²¹²⁸ — essentially zero.
Step 2: Apply the Oracle (Mark the Solution). The Oracle is a quantum operation that recognizes the correct answer and flips its amplitude (think of amplitude as the "weight" of that possibility) from positive to negative. It doesn't tell us what the answer is it just quietly tags it with a minus sign. Critically, the Oracle can evaluate all entries simultaneously thanks to superposition.
Step 3: Apply the Diffusion Operator (Amplify the Solution). The Diffusion Operator (also called "inversion about the mean") reflects all amplitudes around their average value. Since the correct answer now has a negative amplitude (making the average slightly lower), this reflection boosts the correct answer's amplitude while slightly reducing every wrong answer's amplitude.
Step 4: Repeat √N Times, Then Measure. Steps 2 and 3 are repeated approximately √N times. With each iteration, the correct answer's probability amplitude grows while all wrong answers shrink. After about √N iterations, the correct answer's probability is close to 100%, and measuring the qubits reveals the key.
The Mathematics of the Quadratic Speedup
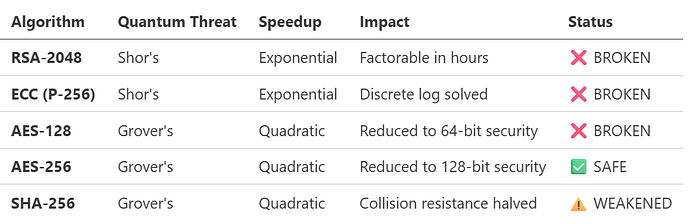
Let's make the speedup concrete. If you're searching a keyspace of size N (for example, all possible AES-128 keys, where N = ²¹²⁸), a classical brute-force attack requires on average N/2 operations. Grover's algorithm requires only about √N operations. Here's what that means in practice for AES:
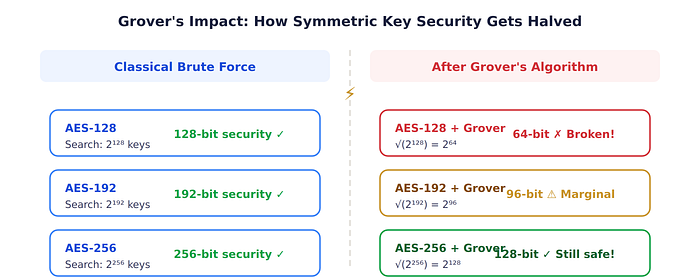
The practical takeaway is clear: AES-256 survives the quantum era, while AES-128 does not. The fix for symmetric encryption is straightforward just use a larger key.
Why Grover's Quadratic Speedup Is Fundamentally Different from Shor's Exponential Speedup
It's important to understand why Grover's threat is manageable while Shor's is catastrophic. With RSA, doubling the key size barely inconveniences Shor's algorithm going from RSA-2048 to RSA-4096 only changes the quantum computation from a few hours to perhaps a few days. But doubling an AES key from 128 to 256 bits means Grover's algorithm now needs ²¹²⁸ operations instead of ²⁶⁴ an increase from feasible to completely impossible even with a quantum computer. This asymmetry is why asymmetric cryptography (RSA, ECC) must be entirely replaced, while symmetric cryptography (AES) just needs a key size bump.
Summary: The Complete Quantum Threat Matrix
The "Harvest Now, Decrypt Later" Threat
The clock isn't ticking from when quantum computers arrive it's ticking from when your data was first encrypted.
Here's the nightmare scenario that keeps cybersecurity professionals awake at night. Right now, sophisticated adversaries nation-states, organized crime syndicates, corporate espionage units are capturing and storing encrypted internet traffic at scale. They can't read it today, but they're betting that in 10–15 years, quantum computers will hand them the decryption keys for free.
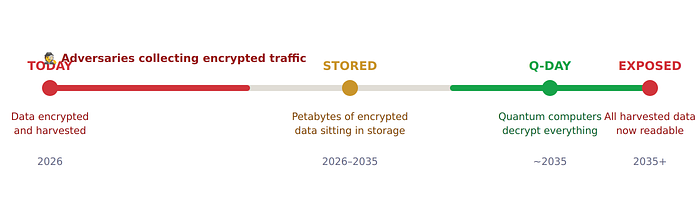
This means medical records transmitted today could be decrypted in 2035. Trade secrets sent via encrypted email could be exposed retroactively. Government and military communications are being harvested right now. Data that needs to remain confidential for decades healthcare records, legal contracts, intellectual property is the most vulnerable.
Think about it this way: If your data needs to stay secret for 10+ years, and a quantum computer capable of breaking RSA arrives in 10 years, then your data is already not secure even though no one can read it today.
Post-Quantum Cryptography: The New Mathematical Shields
The good news? Mathematicians and cryptographers have been working on this problem for years, and solutions are finalized. In August 2024, NIST published the first three post-quantum cryptography standards after an 8-year global competition.
1. CRYSTALS-Kyber → ML-KEM (FIPS 203)
Module-Lattice-Based Key-Encapsulation Mechanism the primary standard for encrypting data and exchanging keys. Based on lattice mathematics specifically, the hardness of finding the closest vector in a high-dimensional lattice (the Closest Vector Problem). Think of a massive multi-dimensional grid of points: finding the nearest point in 2D is trivial, but in hundreds of dimensions with millions of points, it's computationally impossible even for quantum computers. ML-KEM features small keys (768–1024 bytes), fast operations, and works efficiently on everything from servers to smartphones. Used for HTTPS/TLS, VPN, and messaging app key exchange.
2. CRYSTALS-Dilithium → ML-DSA (FIPS 204)
Module-Lattice-Based Digital Signature Algorithm the standard for digital signatures. Proves a message is authentically from you (authentication), hasn't been tampered with (integrity), and can't be denied later (non-repudiation). Also built on lattice problems. Powers software signing, TLS certificates, blockchain transactions, and digital contracts.
3. SPHINCS+ → SLH-DSA (FIPS 205)
Stateless Hash-Based Digital Signature Algorithm the backup plan using a completely different mathematical foundation: hash functions. If lattice-based crypto is ever broken by an unforeseen breakthrough, SLH-DSA provides a safety net. Larger signatures (7–50 KB) and slower, but extremely conservative and safe.
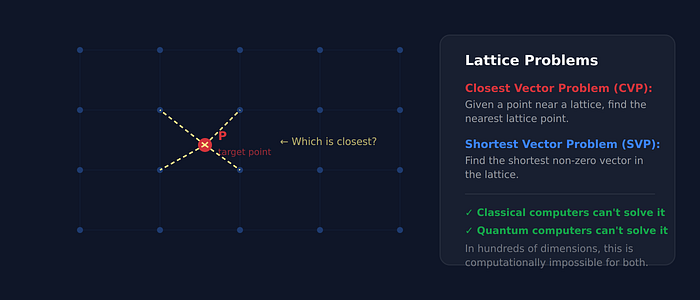
Why These New Algorithms Resist Quantum Attacks
The critical difference is the underlying mathematical structure. Shor's algorithm exploits a specific algebraic pattern present in integer factorization and discrete logarithms which is why it demolishes RSA and ECC. But lattice problems like the Shortest Vector Problem simply don't have that algebraic structure. The best known quantum algorithms for lattice problems are only marginally faster than classical ones nowhere near the exponential speedup Shor achieves.
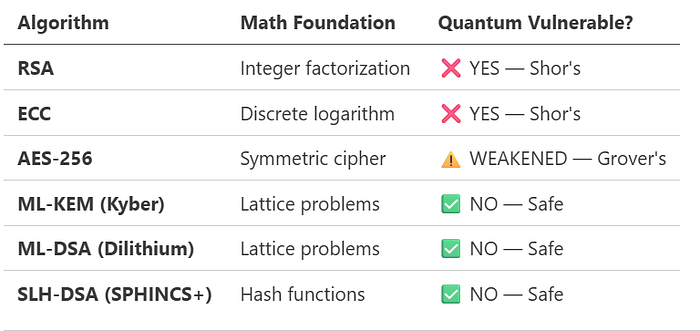
Algorithm Math Foundation Quantum Vulnerable?
Real-World Adoption: Who's Already Using PQC?
The transition isn't a distant future it's happening right now.
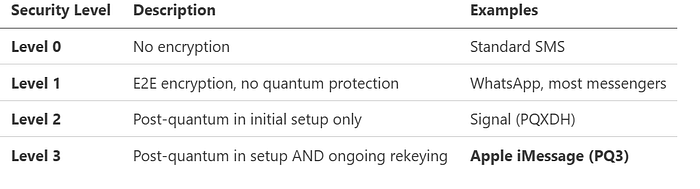
Apple iMessage — PQ3 Protocol (Level 3 Security). Deployed February 2024. Uses a hybrid approach combining classical ECC with post-quantum Kyber-1024. Performs "quantum rekeying" every 50 messages or at least every 7 days, providing a "self-healing" property.
Signal — PQXDH Protocol (Level 2 Security). Implemented late 2023, incorporating CRYSTALS-Kyber into its key agreement protocol. Post-quantum protection during initial key establishment, though without periodic rekeying.
Google Chrome — X25519Kyber768 in TLS. Rolled out starting mid-2023 using hybrid key exchange. By early 2024, Chrome accounted for over 99% of all post-quantum TLS connections with Cloudflare.
Cloudflare & Zoom. Cloudflare enabled PQC across all servers automatically. Zoom announced post-quantum E2E encryption for meetings in 2024.
The Migration Timeline

The Migration Challenge: Not as Easy as Flipping a Switch
While the algorithms are ready, migrating the entire internet's cryptographic infrastructure is monumental. Post-quantum keys and signatures are substantially larger ML-KEM-768 adds 1,568 bytes per handshake versus 64 bytes for X25519 (ECC), and ML-DSA adds roughly 17 KB of handshake overhead.
The deeper problem is crypto agility the ability to swap out cryptographic algorithms without breaking your entire system. Most production systems are decidedly not crypto-agile. Encryption is often hardcoded deep in the stack, poorly documented, and embedded in legacy hardware.
The supply chain factor: Your security depends on OS vendors, browser developers, hardware manufacturers, cloud providers, third-party libraries, and open-source dependencies all upgrading together. One weak link compromises everything.
What You Can Do Right Now
For Individuals
Keep your software updated. Apple's iMessage PQ3 shipped in iOS 17.4+. Chrome and Edge already support hybrid post-quantum TLS. Signal provides PQXDH protection. Simply keeping your devices current gives you meaningful protection today.
Use strong, unique passwords with a password manager. Even with quantum threats, password hygiene matters. Think about the "Harvest Now, Decrypt Later" risk for your most sensitive long-term secrets.
Prefer services that announce PQC support. When choosing messaging apps, email providers, and cloud services, factor in their approach to quantum-resistant encryption.
For Organizations and Architects
1. Inventory your cryptography. Document where encryption is used across your entire stack. Identify every RSA certificate, every ECC key exchange, every TLS endpoint. Pay special attention to legacy systems and embedded devices.
2. Assess your quantum risk. Ask: how long does our data need to remain confidential? Are we a target for "Harvest Now, Decrypt Later"? Healthcare, finance, government, and education organizations should treat this as urgent.
3. Plan your migration. Prioritize TLS key exchange (ML-KEM), then certificate signatures (ML-DSA). Evaluate vendor readiness. Budget for testing and gradual rollout.
4. Build crypto agility into all new systems. Design architecture so cryptographic algorithms can be swapped without rewriting application code. Abstract your crypto layer. Avoid hardcoding algorithm choices.
5. Start testing now. Deploy hybrid post-quantum TLS in staging environments. Measure performance impact. Identify compatibility issues.
Conclusion: The Encryption Revolution Is Here
Post-quantum cryptography represents the most significant change in information security since the invention of public-key cryptography in the 1970s. The reality is stark: quantum computers will break RSA and ECC, the timeline is uncertain but likely within 10–20 years, encrypted data is being harvested right now for future decryption, and the solutions exist and are being deployed today.
The silver lining is extraordinary: unlike previous cryptographic disasters, we're not waiting for the attack to happen before responding. For the first time, we're proactively upgrading our infrastructure before it's broken. CRYSTALS-Kyber, CRYSTALS-Dilithium, and SPHINCS+ aren't academic curiosities they're running in production at Apple, Google, Signal, Cloudflare, and hundreds of other organizations.
The question isn't whether we'll transition to post-quantum cryptography. The question is: will we do it fast enough?
Every day you delay is another day adversaries can harvest your encrypted data for future decryption. Every system left unprotected is a vulnerability waiting to be exploited. The quantum era is coming. The encryption apocalypse is real. But for the first time, we have the mathematical shields to protect us.
The race is on. Are you ready?
About This Article: Researched and written using the latest information from NIST, major technology companies, and cryptographic research as of February 2026.This article was inspired in part by the research work of Jack van Schelven, a recent graduate whose work explores quantum threats to modern encryption.
