I know I've been a bit inactive, but now I'm planning to stay consistent and keep sharing whatever I find during my testing journey. Recently, I got back into testing and while casually exploring a fintech application, something small felt off.
Nothing fancy. No tools. Just curiosity. (off cause)
🌐 How the Website Works
The application had a pretty common signup system. Nothing unusual at first glance.
There were two ways to create an account:
1. Traditional Signup
- Enter username
- Enter email
- Create account
2. OAuth Signup
- Continue with Google
- Continue with LinkedIn
So basically, either sign up manually or just use a third-party account.
🚫 Email Restriction (Interesting Part)
While testing the normal signup flow, I noticed something interesting.
The application does not allow Gmail alias emails.
For example:
jinx+1@gmail.com❌jin.x@gmail.com❌
If you try to sign up using these, the website blocks you. At that moment, I thought:
"Okay… maybe because it's a fintech platform, they want strict control over user identities."
🔍 The Bug
Instead of trying to bypass the normal signup, I tried a different approach.
I created a LinkedIn account using a Gmail alias:
- test+1@gmail.com
The email was verified successfully. Everything looked normal. Then I came back to the target website and clicked:
👉 Continue with LinkedIn
And… it worked.
The account was created successfully using:
- test+1@gmail.com
After signup:
- Login worked perfectly ✅
- Forgot password worked ✅
- Account access was normal ✅
Also:
- The website does not allow editing email later
- And still, it accepted an email that is explicitly blocked in normal signup
Initially, I thought this was not a bug but just a small security gap. Later, I realized that if something violates the company's own enforced policy, it qualifies as a valid issue — even when the direct impact is not obvious.
Final Thought
Sometimes bugs are not about breaking the system. They are about breaking the rules the system tries to enforce.
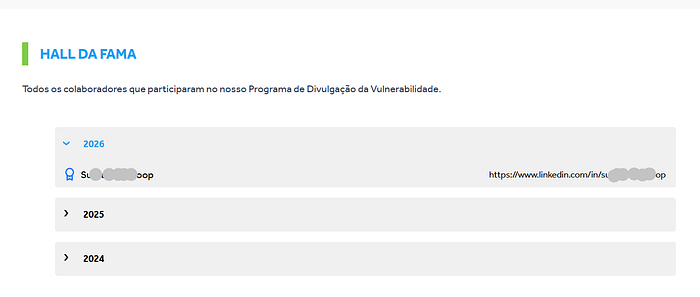
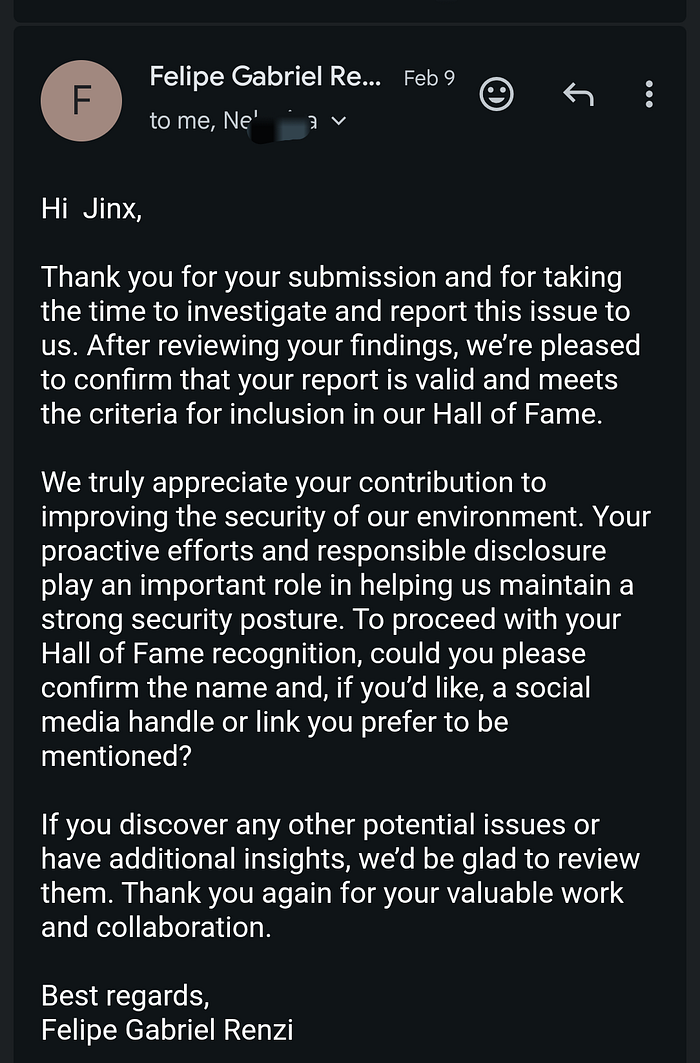
If a restriction exists but can be bypassed, that's still a valid security issue.
👀 Stay tuned for more "No-Tool Bug Bounty" write-ups! Got questions? Email me: strangerwhite9@gmail.com or reach out on
Twitter: @StrangeRwhite9
by StrangeRwhite | Series: Finding Bugs Without Tools