Some vulnerabilities are annoying, and some slow the system down; but Remote Code Execution (RCE) hands over the keys to the kingdom. It allows an attacker to execute code on a system they have no physical access to, just as if they were sitting right in front of the keyboard.
In this post, we'll dissect the anatomy of RCE — one of the most dangerous exploits out there — covering how it goes down, real-world scenarios, and mitigation strategies in technical detail.
What is Remote Code Execution (RCE)?
In its simplest terms, RCE is a security flaw that allows an attacker to execute malicious code remotely on a target system or network. This vulnerability enables the attacker, regardless of their geographic location, to send commands to the target server over the internet and have the server process them as if they were its own native code.
RCE is generally considered the most severe flavor of the Arbitrary Code Execution (ACE) class. Why? Because the attacker doesn't need prior access to the system; the vulnerability itself is the initial foothold.
How Does RCE Work?
RCE attacks typically stem from a lack of proper "input validation" in web apps or network infrastructure. Modern apps are constantly ingesting user data; forms, URL parameters, file uploads, etc. If the app doesn't sanitize this input before passing it straight to an interpreter, that's when the nightmare scenario kicks in.
Fundamentally, there are two methods of Code Evaluation:
1. Remote Code Evaluation (Dynamic Code Execution)
In this scenario, the application contains dangerous functions like eval() that process user-supplied data.
Example Scenario (PHP): Imagine a developer writes insecure code to assign user registration dates to variables:
// Unsafe code example
eval("\$$user = '$regdate';");Normally, the $user variable should just represent a username. However, if the attacker sends the following value as the username (input):
px = 'y';phpinfo();//
The PHP interpreter combines and runs the code within the eval function like this:
$x = 'y';phpinfo();// = '2016';The Result? The attacker runs the phpinfo() function and dumps the server configurations. Imagine if they typed system('rm -rf /') here—the whole server would be wiped clean.
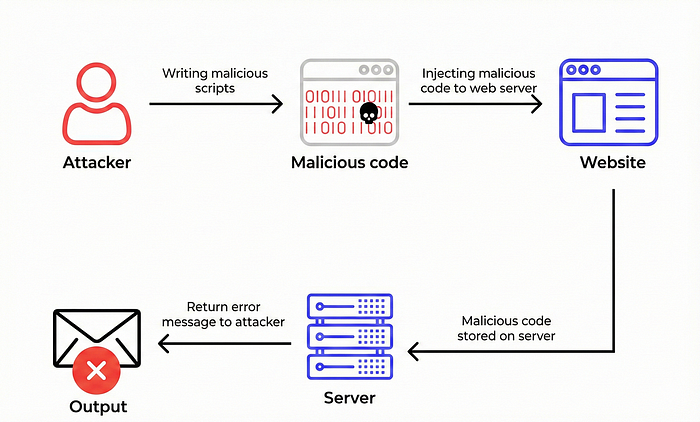
2. Stored Code Evaluation
This method relies on injecting code into server configuration files rather than triggering an immediate function call.
Example Scenario: Let's assume a web app stores language settings in a file. The expected URL request is: ?language=de
This request is written to the file on the server as $lan = 'de';.
However, if the attacker manipulates the input like this: de';system('cat /etc/passwd');//
The code written to the file becomes:
$lan = 'de';system('cat /etc/passwd');//';Every time the application calls (includes) this settings file, the attacker's command executes, and the system's password file is exposed.
Common RCE Vectors
RCE isn't done via a single method; it's a result. The paths leading to this result include:
- Injection Flaws: Vulnerabilities like SQL Injection or Command Injection can lead to the execution of database or operating system commands.
- Insecure Deserialization: This involves manipulating the data structure during serialization (transfer) and deserialization to create malicious objects. It is frequently seen in Java applications (See: Log4j).
- Out-of-Bounds Write (Buffer Overflow): In languages with manual memory management (C/C++), this involves the attacker writing data outside the allocated memory buffer to alter the program flow and execute their own code (shellcode).
- File Management Errors: An attacker uploads a malicious file (web shell) with extensions like
.php,.jsp, or.aspto the server and triggers it via the browser.
Real-World RCE Examples: Attacks That Made History
Let's put the theory aside and look at how this vulnerability impacted the world.
WannaCry and EternalBlue
In 2017, the WannaCry ransomware locked up over 150,000 computers. At the heart of this attack was an RCE vulnerability. Attackers exploited a flaw in Windows' SMB protocol (EternalBlue) to infiltrate systems and execute code remotely without users having to click a single thing.
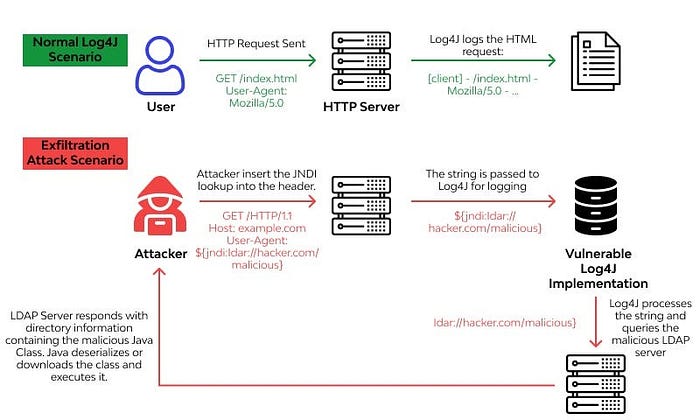
Log4Shell (CVE-2021–44228)
One of the biggest catastrophes in recent history. It was an RCE vulnerability in the Java-based logging library, Log4j. Attackers could simply send a specific string (${jndi:ldap://...}) to a log file (like a Minecraft chat box or a username field on a login screen), forcing the server to redirect to an address they controlled and execute code.
What Can an Attacker Do with RCE?
For an attacker who achieves RCE, the limit is usually just their imagination:
- Full System Control: They can gain root/admin privileges on the server.
- Data Theft: They can steal databases, customer info, and trade secrets.
- Ransomware: They can encrypt all files and demand a ransom.
- Cryptojacking: They can mine cryptocurrency using the server's resources.
- Pivoting (Lateral Movement): They can use the compromised server as a jump box to attack other secure systems within the internal network.
How to Protect Against RCE Attacks?
Stopping RCE isn't a one-click fix; it requires a layered security architecture.
- Input Sanitization: Never trust user data. Validate all inputs (using a whitelist method) and scrub special characters.
- Avoid Dangerous Functions: Avoid using functions like
eval(),system(), andexec()in your code. If you must use them, filter inputs strictly. - Patch Management: Keep operating systems, web servers, and third-party libraries (dependencies) up to date. Vulnerabilities like Log4Shell spread due to outdated libraries.
- WAF (Web Application Firewall): Use a WAF to monitor network traffic and block known RCE signatures.
- Least Privilege: Never give "root" or "administrator" privileges to the service running your web app. Even if the app gets hacked, the attacker's scope should remain limited.
Conclusion
Remote Code Execution is the most devastating scenario a web application can face. As developers, with every line of code we write, we have to consider where that data is coming from and how it's being interpreted. In cybersecurity, a chain is only as strong as its weakest link; RCE snaps that chain completely.

Halil İbrahim Eroğlu
