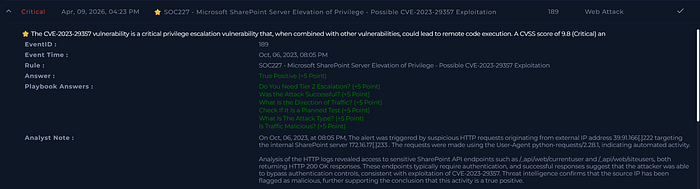
Understanding the Alert
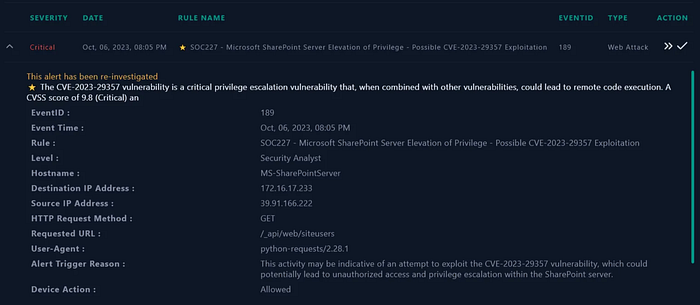
The rule SOC227 was triggered due to activity consistent with exploitation of CVE-2023–29357, a critical authentication bypass vulnerability in Microsoft SharePoint Server 2019. The alert was generated because an external IP sent automated HTTP requests to sensitive SharePoint API endpoints using a scripted User-Agent, matching known post-exploitation enumeration patterns.
Traffic Direction: Internet → Internal Network (39.91.166[.]222 → 172.16.17[.]233)
What Is CVE-2023–29357?
CVE-2023–29357 is a critical authentication bypass via JWT (JSON Web Token) manipulation in Microsoft SharePoint Server. An unauthenticated attacker can:
- Craft a forged JWT token with the algorithm set to
none - Send it to the SharePoint server
- SharePoint fails to validate the signature
- The attacker is treated as a legitimate — or even admin — user
This vulnerability becomes especially dangerous when chained with CVE-2023–24955 (Remote Code Execution), creating a full unauthenticated RCE attack chain. It has been added to the CISA Known Exploited Vulnerabilities (KEV) list and is actively exploited in the wild.
MITRE ATT&CK mapping: T1210 — Exploitation of Remote Services, Privilege Escalation, Lateral Movement.
Threat Intelligence — Source IP Analysis
IP: 39.91.166[.]222
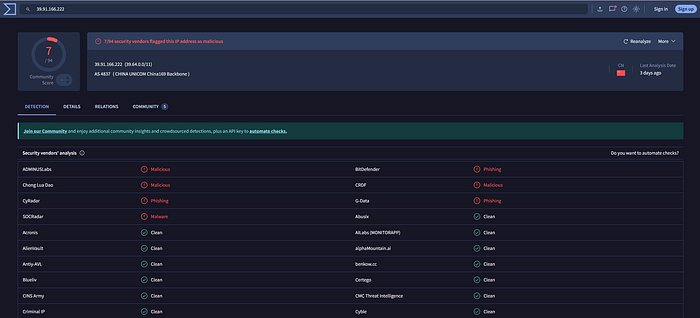
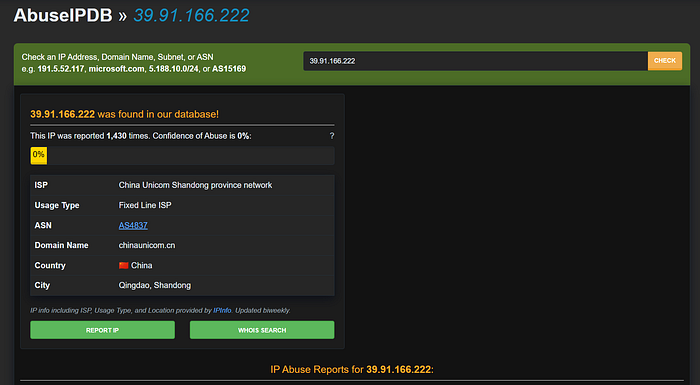
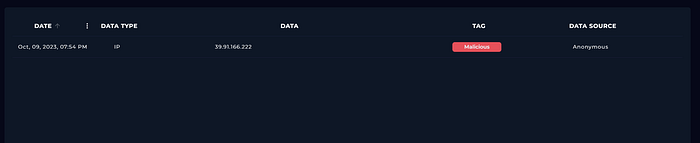
The IP is external, has no legitimate business relationship with the organization, and is confirmed malicious across multiple threat intelligence platforms.
HTTP Traffic Analysis
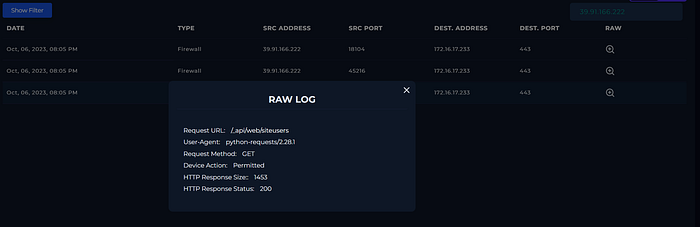
Examining the IIS and HTTP logs revealed the following requests from the attacker:
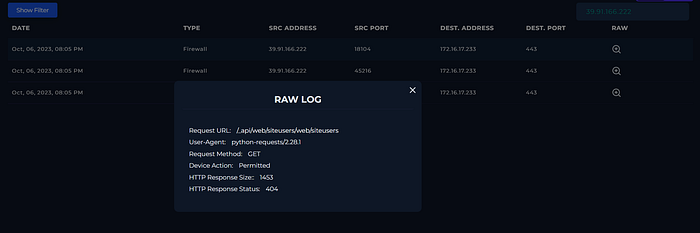
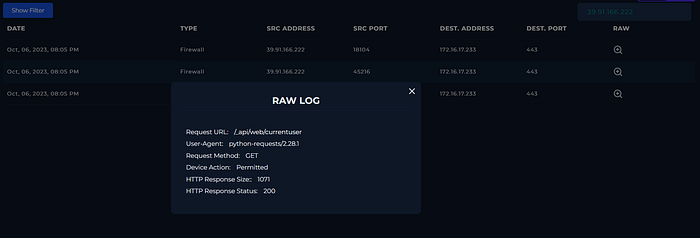
GET /_api/web/currentuser → HTTP 200 OK
GET /_api/web/siteusers → HTTP 200 OK
User-Agent: python-requests/2.28.1Several things stand out immediately. The python-requests User-Agent is a strong indicator of automated, scripted activity — not a legitimate browser session. In an enterprise environment, this is inherently suspicious.
The endpoints targeted are significant: /_api/web/currentuser is typically used to verify the identity of the authenticated session, and /_api/web/siteusers is used to enumerate all users on the SharePoint site. Both require authentication under normal circumstances.
The HTTP 200 OK responses on both endpoints confirm that the requests were processed successfully and returned data — meaning the attacker was not rejected.
What the Attacker Was Doing — Step by Step
Step 1: GET /_api/web/currentuser → 200 OK
"Who am I? Verify the bypass worked."
Step 2: GET /_api/web/siteusers → 200 OK
"Dump all users. Find admins and targets."This is a classic post-exploitation enumeration flow following a successful authentication bypass. The attacker confirmed the exploit worked and then moved to gather intelligence for further lateral movement or privilege escalation.
Endpoint Investigation
Endpoint logs for MS-SharePointServer (172.16.17.233) were reviewed, including process history, command execution, and persistence mechanisms. No suspicious endpoint artifacts were found — no unusual processes, no dropped files, no persistence entries.
This is expected behavior for CVE-2023–29357. Unlike malware-based attacks, this vulnerability operates entirely at the HTTP/API layer. There is no code execution on the host, no files dropped, and no processes spawned. The compromise is invisible at the endpoint level, which is exactly what makes it dangerous and easy to miss.
The evidence of success comes from the HTTP response, not the endpoint. Both targeted API endpoints returned 200 OK, which means the SharePoint server accepted the requests and returned protected data — confirming authentication was bypassed.
Attack Type
This attack does not fall under common injection categories (SQL Injection, XSS, Command Injection, LFI/RFI, IDOR, or XML Injection). It is based on:
- JWT token forgery
- Improper cryptographic validation
- API abuse and user enumeration
Attack Type: Other (Authentication Bypass / Broken Access Control)
Final Verdict: True Positive
Artifacts Added
1. Attacker IP
- Value:
39.91.166[.]222 - Type: IP Address
- Comment: External malicious IP exploiting SharePoint vulnerability
2. Destination IP
- Value:
172.16.17[.]233 - Type: IP Address
- Comment: Target SharePoint server
3. URL
- Value:
/api/web/currentuser - Type: URL Address
- Comment: Successful API access (HTTP 200)
4. URL
- Value:
/api/web/siteusers - Type: URL Address
- Comment: User enumeration endpoint accessed
Analyst Notes
On Oct 06, 2023, at 08:05 PM, the alert was triggered by suspicious HTTP requests originating from external IP address 39.91.166[.]222 targeting the internal SharePoint server 172.16.17[.]233. The requests were made using the User-Agent python-requests/2.28.1, indicating automated activity.
Analysis of the HTTP logs revealed access to sensitive SharePoint API endpoints /_api/web/currentuser and /_api/web/siteusers, both returning HTTP 200 OK responses. These endpoints typically require authentication, and successful responses indicate the attacker was able to bypass authentication controls, consistent with exploitation of CVE-2023-29357. Threat intelligence confirms the source IP is flagged as malicious across multiple platforms, further supporting the conclusion that this activity is a True Positive.
The successful access to protected SharePoint API endpoints indicates the attacker performed unauthorized user enumeration, confirming the attack was successful. Although no suspicious activity was observed at the endpoint level (such as process execution or persistence), this is expected for this vulnerability, as exploitation occurs entirely via web requests without requiring code execution on the host. Given the confirmed exploitation and unauthorized access, containment of the affected SharePoint server is recommended to prevent further attacker activity, including a possible RCE chain via CVE-2023–24955. Additional actions such as reviewing SharePoint logs, applying the June 2023 Microsoft Patch Tuesday security updates, and monitoring for further suspicious API activity are also advised. Due to the confirmed successful exploitation, this incident requires Tier 2 escalation for deeper investigation and remediation.