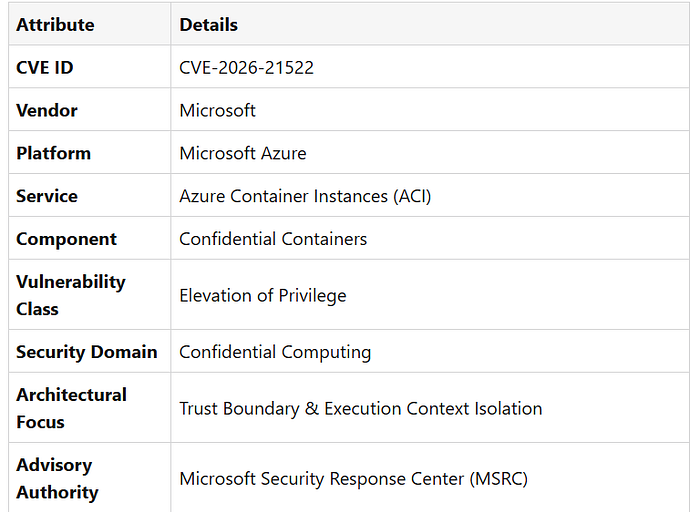
CVE-2026–21522 | Microsoft ACI Confidential Containers Elevation of Privilege Vulnerability is not noise in the Azure ecosystem — it is a precise lesson in how trust boundaries, execution context, and confidential workload isolation are designed to operate at scale.
Vulnerability Overview
Read the Complete Technical Analysis | CVE-2026–21522 | Microsoft ACI Confidential Containers Elevation of Privilege Vulnerability
Within Azure Container Instances, Confidential Containers represent Microsoft's commitment to:
- Hardware-backed isolation
- Secure enclave execution
- Cryptographic workload protection
- Deterministic privilege enforcement
CVE-2026–21522 invites us to look deeper — not at what "went wrong" — but at how execution context separation behaves under specific privilege conditions, and how elevation pathways are methodically constrained through Microsoft's security architecture.
This is about understanding the subtle mechanics of:
- Container privilege models
- Boundary enforcement
- Identity propagation
- Isolation guarantees in practice
Quietly.
Precisely.
By design.
The Azure world does not move through noise — it evolves through clarity.
And clarity comes from understanding architecture at its edges.
Architectural Context
Azure Confidential Containers are engineered to enforce strict separation between:
- Host and container execution contexts
- Tenant workloads
- Identity boundaries
- Privileged and non-privileged operations
The confidential computing stack in ACI leverages:
- Hardware-backed trusted execution environments
- Memory encryption
- Attestation mechanisms
- Policy-driven workload isolation
CVE-2026–21522 provides insight into how privilege elevation conditions are evaluated within this model — and how Azure's security architecture methodically governs execution pathways.
Why This Matters
Understanding this advisory is not about identifying weakness.
It is about studying:
- How trust boundaries are defined
- How privilege transitions are evaluated
- How isolation guarantees are honored
- How secure design behaves under edge conditions
Security maturity is not built at the center of architecture.
It is built at its boundaries.