Assets, threat actors, vulnerabilities, exposure, control selection, and the management judgment that turns risk theory into security decisions.
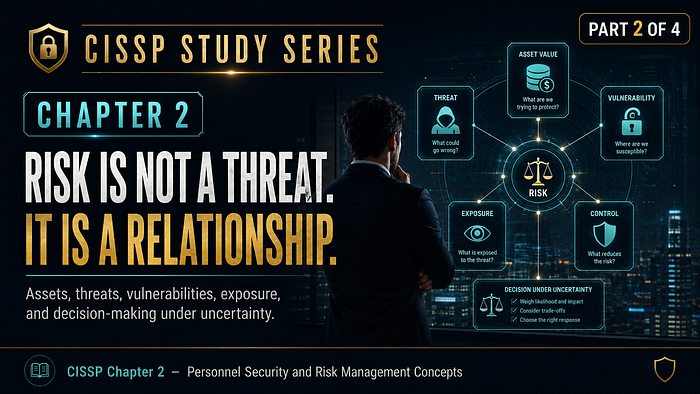
Many security conversations collapse risk into a single word: threat. That shortcut is understandable, but it is incomplete. A threat is not the same as risk, and treating them as synonyms often leads organizations to respond to noise, underinvest in fundamentals, or buy controls that look impressive without solving the actual problem.
Why CISSP insists on precision in risk language
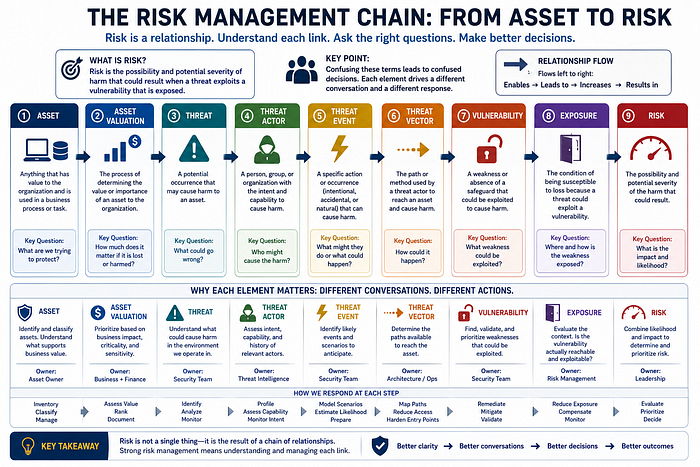
The chapter's risk management section defines a chain of terms that are easy to memorize but much harder to apply well: asset, asset valuation, threat, threat actor, threat event, threat vector, vulnerability, exposure, and risk. The reason CISSP spends time on these distinctions is not academic elegance. It is operational clarity. If leaders confuse these terms, their decisions become confused as well.
An asset is anything used in a business process or task. A threat is a potential occurrence that may cause harm. A vulnerability is a weakness or absence of a safeguard. Exposure is the condition of being susceptible to loss because a threat could exploit that weakness. Risk is the possibility and potential severity of the harm that could result. Each element matters because each leads to a different conversation. You do not value a threat the way you value an asset. You do not fix exposure the way you fix a vulnerability. You do not treat a threat actor the same way you treat a threat event.
That is why the chapter's framing is so useful. It teaches that risk is not a standalone object. It is a relationship. Until those relationships are understood, organizations tend to oversimplify decisions and rely on intuition when they should be using disciplined judgment.
Start with the asset, or everything else becomes abstract
In the healthcare portal scenario, the legacy application matters because the asset matters. It supports patient access, operational continuity, and organizational credibility. Asset valuation is therefore not only about direct replacement cost. It also includes business criticality, process dependence, time, productivity, customer trust, and potential downstream disruption.
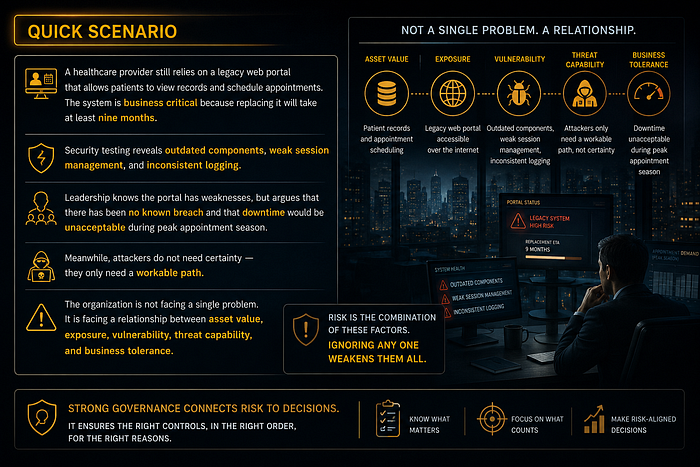
One reason security teams struggle to win investment conversations is that they begin with threat language instead of asset language. Leaders are often more prepared to discuss mission interruption, revenue impact, patient safety, customer trust, or regulatory consequences than CVE counts alone. When the value of the asset is not articulated clearly, the risk conversation becomes technical too early.
CISSP thinking encourages a different sequence. First, establish why the asset matters. Then map what could harm it. Then identify which weaknesses make that harm plausible. Then ask whether current controls reduce the likelihood or impact to an acceptable level. That order gives risk analysis business context before technical detail.
Threats, actors, events, and vectors are not interchangeable
The chapter carefully distinguishes threats, threat agents or actors, threat events, and threat vectors. That distinction is not trivial. A threat is the possibility of undesirable harm. A threat actor is the person or entity intentionally exploiting weaknesses. A threat event may be accidental, natural, or intentional. A vector is the path used to reach the target. These elements are related, but they do not answer the same question.
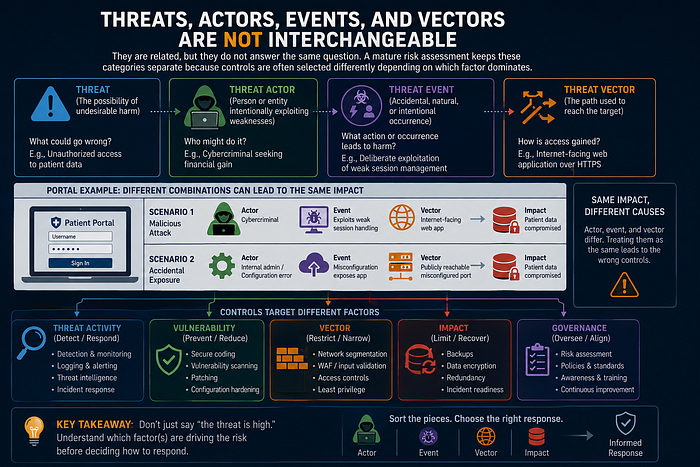
Consider the portal example. A malicious actor exploiting weak session management is different from a configuration error causing unplanned exposure, even if both result in compromised data. The actor, the event, and the vector differ. A mature risk assessment keeps those categories separate because controls are often selected differently depending on which factor dominates. Detection and logging may help identify threat activity. Secure coding and patching reduce vulnerability. Segmentation or WAF logic may narrow the vector. Backups and incident readiness can reduce impact.
When organizations say, "The threat is high," they often mean several different things at once. They may mean the asset is attractive, the vulnerability is obvious, the actor capability is credible, the vector is accessible, or the consequences would be severe. CISSP expects you to sort those pieces out before judging response.
Exposure is where theoretical weakness becomes business concern
Exposure is one of the most useful but underappreciated words in the chapter. A vulnerability can exist without creating the same level of concern in every context. Exposure asks whether the environment allows that weakness to matter. Is the system reachable? Is the function enabled? Is the data valuable? Are attackers likely to care? Does the business depend on the system heavily enough that disruption matters?

In the portal scenario, weak session handling is not just a coding issue. It becomes exposure because the application is internet-facing, patient-accessible, business critical, and difficult to replace quickly. The context magnifies the weakness. That means the organization is not merely dealing with a flaw. It is dealing with an exploitable business condition.
This is where risk conversations become more honest. Teams can no longer hide behind generic language such as "we know it is old but it is stable." Stability and exposure are not the same thing. A stable but exposed system may still carry serious risk if the wrong relationships are in place.
Qualitative and quantitative analysis are tools, not ideologies
The chapter also introduces comparison between quantitative and qualitative risk analysis. This is an area where practitioners sometimes become overly rigid. Some leaders want numbers for everything. Others distrust numbers because assumptions can be wrong. The real lesson is that both methods are useful when used with discipline.
Quantitative approaches try to express risk in numeric or monetary terms, which can be helpful for prioritization, budgeting, and cost comparison. Qualitative approaches use rankings such as low, medium, and high, which can be more practical when data is incomplete or impact spans financial and nonfinancial dimensions. Neither method is automatically superior. What matters is whether the analysis is credible enough to support a better decision than guesswork.
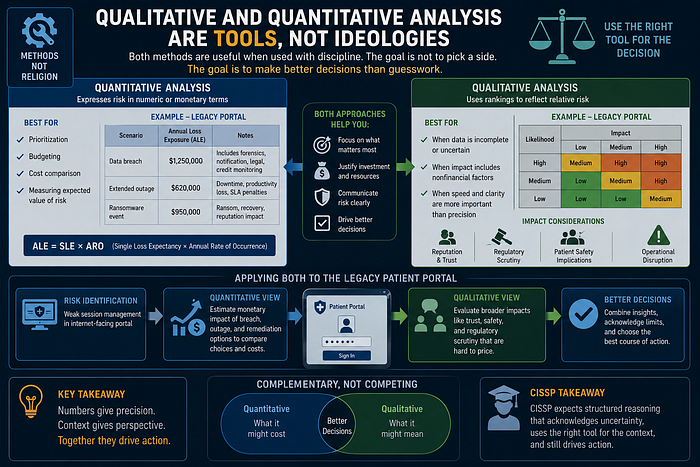
For the legacy portal, a quantitative estimate may help compare remediation options, downtime scenarios, or compensating control costs. A qualitative view may better capture reputational damage, patient trust concerns, or regulatory scrutiny. CISSP does not reward blind devotion to one method. It rewards structured reasoning that acknowledges limits and still drives action.
A simple visual model for risk relationships
One of the easiest ways to strengthen risk conversations is to visualize the chain instead of discussing isolated terms. Start with the asset in the center. Around it, identify which business processes depend on it. Then map the threat sources that might cause harm, the vectors available to them, the vulnerabilities that make success more plausible, and the existing controls that narrow likelihood or impact. Finally, mark the remaining exposure and ask who owns the decision if residual risk remains.
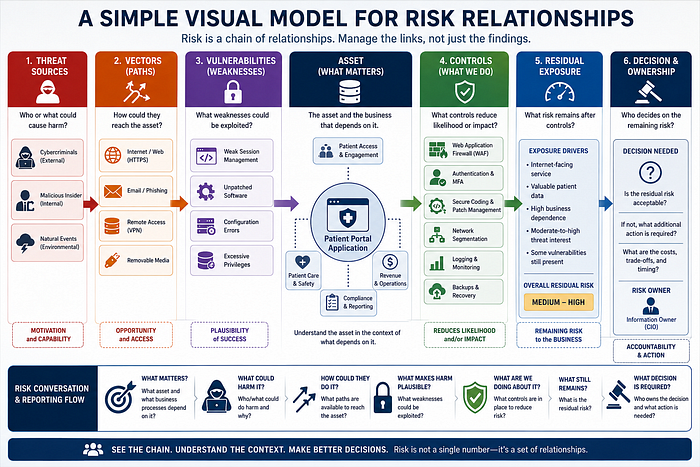
This kind of diagram may look simple, but it changes the conversation. Teams stop arguing over single findings and start seeing how the system behaves as a whole. A vulnerability without reachability looks different from the same vulnerability on an internet-facing service tied to customer trust. A powerful attacker with weak opportunity looks different from an ordinary attacker with a frictionless path. Risk becomes easier to explain because relationships are visible rather than implied.
That is also why Chapter 2 should influence reporting style. Good risk communication does not drown leadership in disconnected technical facts. It presents a structured chain: what matters, what could harm it, what makes harm plausible, what we are doing about it, what still remains, and what decision is required.
Selecting controls is a management judgment, not a shopping exercise
One of the strongest practical sections in the chapter is the guidance on countermeasure selection. Controls should cost less than the value they protect and less than the benefit they provide. They should solve real problems, withstand scrutiny even if publicly known, be testable, offer consistent protection, minimize dependencies, resist tampering, provide privileged overrides, and support fail-safe or fail-secure behavior where appropriate. This is a remarkably sober set of criteria because it cuts through marketing.
In the portal scenario, the wrong move would be to deploy a highly visible control that does not reduce the relevant exposure. Buying a new product is emotionally satisfying because it creates the sense of progress. But CISSP thinking asks a better question: does this control materially change the relationship between the vulnerable asset and plausible harm? If not, the organization may be spending money without reducing risk.
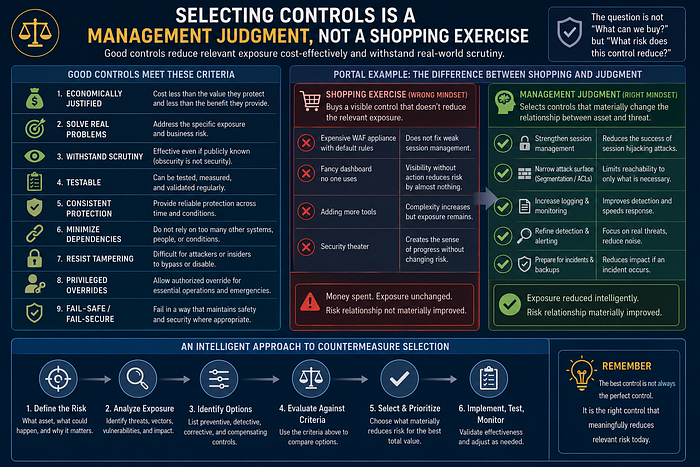
Sometimes the best control is compensating rather than perfect. Maybe the application cannot be rewritten immediately, but session protections can be improved, logging strengthened, attack surface narrowed, segmentation tightened, monitoring refined, and incident response prepared. Mature risk management often means reducing exposure intelligently while longer-term remediation continues.
Residual risk and tolerance are executive choices
No control strategy eliminates all risk. Once reasonable safeguards are selected and implemented, some residual risk remains. The organization must then decide whether that remaining risk is acceptable, transferable, avoidable, or still in need of further reduction. This is not just a security team call. It is a leadership decision informed by security analysis.
The healthcare example makes this plain. Because the portal cannot be replaced immediately, leadership may choose to accept some residual risk temporarily. But acceptance is not the same as neglect. Responsible acceptance requires explicit ownership, documented rationale, known compensating controls, review dates, and triggers for reassessment. Otherwise, what looks like acceptance is really drift.
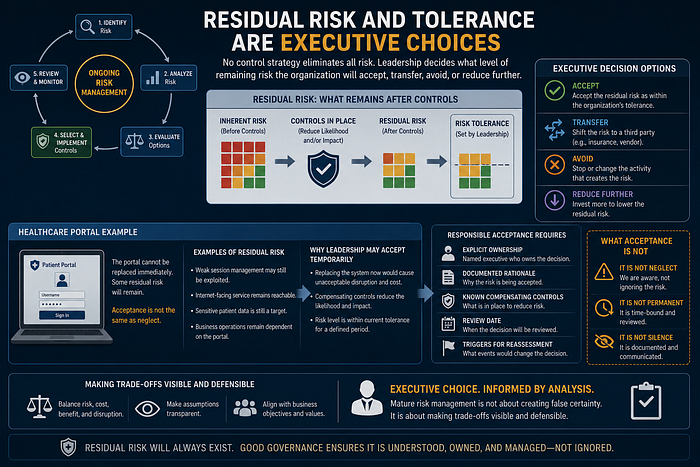
This is where Chapter 2 becomes especially relevant for experienced professionals. Mature risk management is not about creating false certainty. It is about making trade-offs visible and defensible.
Practical management trade-offs in the real world
Real organizations almost never manage risk in a perfectly clean environment. Budgets are constrained, systems are inherited, business cycles create urgency, and not every dependency can be modernized on demand. That is precisely why a relationship-based view of risk is so useful. It allows leaders to ask what can be changed now, what must be monitored closely, what can be compensated for temporarily, and what requires strategic replacement.
For the healthcare portal, management may decide to reduce session exposure immediately, restrict administrative reachability, tighten logging, increase anomaly detection, improve incident preparation, and define a firm modernization roadmap. None of these decisions alone solves the entire problem. Together, however, they reshape the risk relationship enough to move the organization from blind tolerance to managed tolerance.

This is a mature posture because it acknowledges reality without surrendering to it. CISSP is not asking you to imagine ideal environments. It is asking you to make sound decisions in imperfect ones.
The final nuance is this: accepted risk ages. A risk decision made six months ago may no longer be wise if the asset becomes more important, the threat landscape shifts, the business dependence increases, or the control environment weakens. Risk management therefore requires periodic re-evaluation, not just initial classification. That cyclical discipline is one of the reasons the chapter remains so relevant in practice.
Question set — aligned with the scenario
Question 1: A healthcare provider continues to rely on a legacy patient portal that is internet-facing, business critical, and difficult to replace quickly. Security testing identifies outdated components, weak session management, and inconsistent logging. Leadership argues that there has been no known breach and that downtime during peak appointment season would be unacceptable. Why should leadership be concerned now rather than later?
A. The portal uses older technology B. The organization has no confirmed evidence of exploitation yet C. Business-critical patient services depend on a vulnerable and exposed system D. Risk becomes real only after a successful attack is verified
This question tests a core CISSP principle: risk exists before an incident is confirmed. In the scenario, the portal is not merely old. It is a high-value asset tied to patient services and business continuity, and it is also exposed through reachable weaknesses such as poor session management and inconsistent logging. That combination is what makes leadership attention necessary now. Part 2 emphasizes that risk is a relationship among asset value, vulnerability, exposure, threat plausibility, and business consequence. C is the correct answer because this answer captures the full risk relationship. The portal matters to the business, it has meaningful weaknesses, and those weaknesses are exposed in a way that could lead to harm.
Question 2: The security team proposes a new control for the legacy portal. The product is expensive, highly visible, and popular in the market, but it does not clearly address the identified weaknesses in session handling, logging, or internet exposure. What is the strongest reason to reject the control?
A. It is expensive and difficult for executives to understand B. It is popular in the market but does not materially reduce the identified exposure C. The vendor's protection claims are too ambitious D. The team may not use all of the advanced features immediately
This question goes to the heart of control selection. Part 2 stresses that controls should not be chosen because they are fashionable, reassuring, or feature-rich. They should be selected because they reduce the real risk relationship. If the identified exposure is tied to weak session management, logging gaps, and reachable attack paths, then a control that does not materially change those conditions is not a good investment, regardless of its popularity. B is the correct answer because a strong control must address the actual risk drivers. If it does not reduce likelihood or impact in a meaningful way, it is security theater rather than risk treatment.
Question 3: Because the portal cannot be replaced for at least nine months, leadership decides to continue operating it with strengthened session protections, tighter logging, narrowed administrative reachability, and improved monitoring. Some residual risk remains. Which approach best reflects mature risk acceptance?
A. Continue operating the portal and avoid documenting the remaining risk to reduce concern B. Accept the remaining risk informally because the system is business critical C. Document ownership, rationale, compensating controls, review dates, and reassessment triggers D. Transfer the risk completely to the IT department until modernization is complete
Part 2 makes an important distinction: risk acceptance is not the same as neglect. If the organization must continue operating the portal temporarily, mature governance requires that residual risk be explicitly owned, documented, bounded, and revisited. Without ownership, rationale, compensating controls, review dates, and reassessment triggers, what looks like acceptance is really unmanaged drift. C is the correct answer because this is what responsible, defensible risk acceptance looks like. It acknowledges business reality without abandoning governance discipline.
What this part should make you question
This chapter segment should make the reader think beyond labels. Are we talking about threats when the real issue is exposure? Are we patching symptoms without understanding asset value? Are we using numbers to create confidence or to hide uncertainty? Are we evaluating controls for reduction of real risk, or for their ability to reassure an anxious audience? Do we know which risks are truly accepted and by whom?
When those questions are answered clearly, risk management becomes less theatrical and more strategic. The organization can stop reacting to isolated findings and start managing relationships that actually determine security outcomes.
Scenario debrief: what mature review would change
A mature review of the healthcare portal scenario would begin by separating labels that are often blurred together. The exposed customer records are assets. The outdated internet-facing application and weak session controls are vulnerabilities. The attacker or botnet is the threat agent. The reachable attack path is the exposure. The actual business concern is risk: the combination of likelihood and impact if those conditions are exploited.
That review would then ask what should change first. Mature teams would reduce exposure quickly, strengthen authentication and session management, limit administrative reachability, and confirm whether the proposed controls actually reduce the specific risk rather than merely creating the appearance of action. They would also document any residual risk honestly, because unrecorded accepted risk is not governance. It is avoidance.
CISSP mindset check
The CISSP mindset here is to resist collapsing all uncertainty into the word threat. Risk is relational. It exists because valuable assets, exploitable weaknesses, realistic threat paths, and business consequences intersect. The strongest answer in an exam scenario is often the one that clarifies those relationships and chooses a control response that is proportionate, testable, and economically defensible.
In other words, a mature practitioner does not ask only, 'What could go wrong?' A mature practitioner also asks, 'What are we protecting, why is it exposed, how much does the exposure matter, and what response changes the equation most effectively?'
Questions to carry forward
Carry these questions into every later domain. Are we discussing the asset with enough precision to understand why it matters? Are we naming the real vulnerability, or just describing the resulting anxiety? Is a proposed safeguard actually reducing likelihood or impact, or is it simply expensive? And if we say the risk is accepted, who accepted it, for how long, and under what assumptions?
Why reassessment matters
Risk decisions expire even when nobody formally retires them. Asset value changes. Threat actors adapt. Exposure expands through cloud connectivity, vendor relationships, new business features, and operational shortcuts. Controls that were once sufficient may become brittle under scale or outdated against new tactics.
That is why reassessment matters. Risk management is not a ceremony performed once to satisfy governance language. It is a living process. The portal that was tolerable last quarter may be unacceptable today if the application now stores more sensitive data, is integrated with additional services, or has become central to revenue and customer trust.
A final operational reminder
Operationally, always tie the control discussion back to business reality. Choose safeguards that address identified conditions, can be tested, and cost less than the harm they meaningfully reduce. Record assumptions. Name residual risk plainly. And revisit accepted risk before the environment forces the reassessment for you.
Final perspective
The strongest lesson in this part of Chapter 2 is that risk cannot be managed as a headline. It has to be mapped as a relationship among business value, weakness, plausibility, exposure, and consequence. The more precisely those relationships are understood, the less likely an organization is to confuse activity with protection.
Closing thought
In Part 3, I will shift from structured risk reasoning to one of the most effective real-world attack paths: social engineering, where the decisive weakness is often not code or infrastructure but human judgment under pressure.