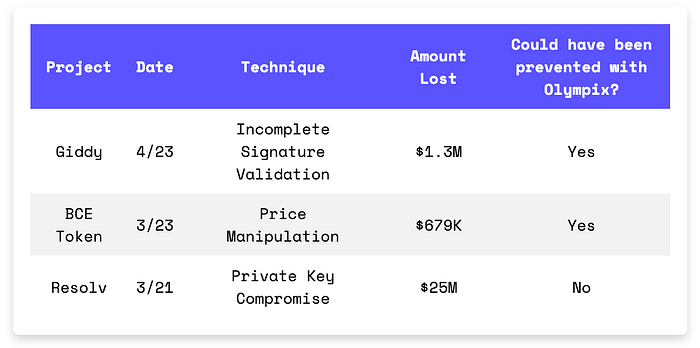
A breakdown of three recent exploits across Ethereum and BSC that together resulted in $27M in losses. Giddy was drained for $1.3M through incomplete signature validation in its vault contract, where unsigned fields allowed an attacker to reuse a valid signature with modified swap parameters. BCE Token lost $679K when a burn flaw enabled an attacker to manipulate the PancakeSwap pool price using a flash loan from Venus. Resolv suffered a $25M loss after off-chain signing infrastructure was compromised, allowing unauthorized minting of 80M USR stablecoins without collateral deposits.
In Brief
- Giddy lost $1.3M due to incomplete signature validation.
- BCE Token lost $679K due to a burn flaw that allowed price manipulation.
- Resolv lost $25M due to compromised signing keys enabling unauthorized minting.
Hacks Analysis
Giddy | Amount Lost: $1.3M
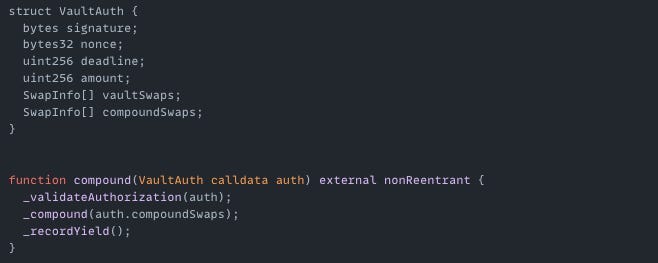
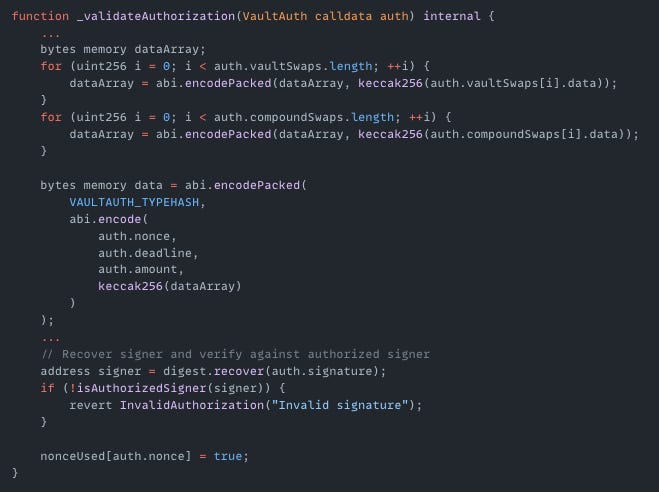
On April 23rd, the Giddy exploit on the Ethereum mainnet resulted in a $1.3M loss. The root cause of the exploit was an incomplete signature validation in giddyVaultV3's struct VaultAuth. The protocol required a valid signature to approve swaps but the signature only covered part of the swap data. Critical fields such as fromToken, toToken, amount, and aggregator were not included in the signed message. This allowed the attacker to reuse a valid signature while changing the unsigned fields. The attacker modified token approvals, swap targets, and amounts, then redirected funds to their own address.
Exploited Contract: 0x5f0ad32c00641d1d2bb628ff341e0d4bb4494318
Transaction: 0x5edb66a4c2ea55bba95d36d27713e3bb1c67c3c4199a8a1759e754c6f25482e5
BCE Token | Amount Lost: $679K
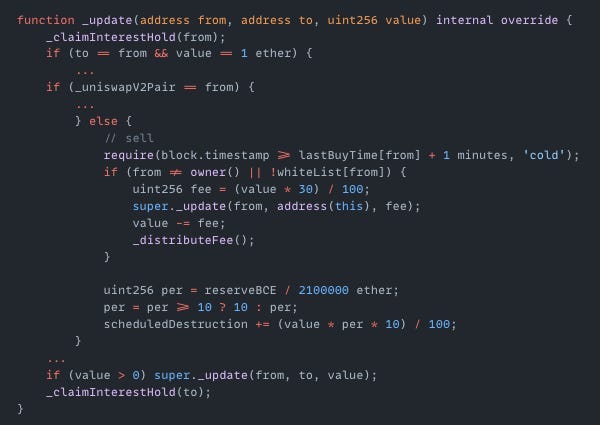
On March 23rd, the BCE Token exploit on BSC resulted in a $679K loss. The root cause was a flaw in BCE's token contract that allowed an attacker to burn tokens directly from the PancakeSwap liquidity pool, manipulating the token price. The attacker took a flash loan from Venus, bought and sold BCE to trigger a burn that removed nearly all BCE from the pool. Once the BCE token price was artificially increased, the attacker sold the remaining BCE tokens and made a profit.
Exploited Contract (on BSC): 0xcdb189d377ac1cf9d7b1d1a988f2025b99999999
Transaction: 0x85ac5d15f16d49ae08f90ab0e554ebfcb145712342c5b7704e305d602146d452
Resolv | Amount Lost: $25M
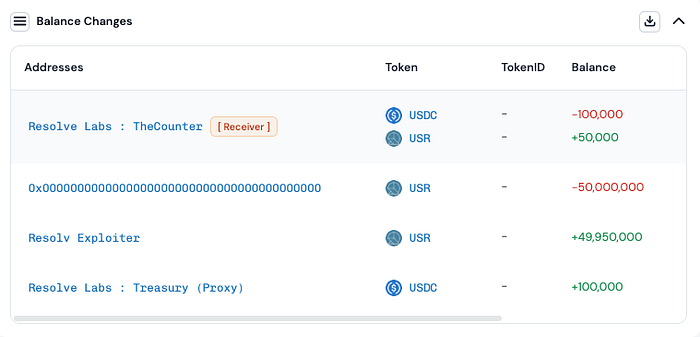
On March 22nd, the Resolv exploit on the Ethereum mainnet resulted in a $25M loss. The root cause was a compromise of off-chain signing infrastructure that resulted in authorized minting of $80M USR stablecoins. The attacker gained access to the signing key by compromising infrastructure credentials and modifying access policies. With signing authority, the attacker executed two transactions minting 80M USR tokens without depositing collateral.
Transaction: 0xfe37f25efd67d0a4da4afe48509b258df48757b97810b28ce4c649658dc33743
Olympix: Your Partner in Secure Smart Contracts
Olympix provides advanced analysis tools to help developers identify and fix vulnerabilities before they become critical exploits.
Get started today to fortify your smart contracts and proactively shield them from exploits in the evolving Web3 security landscape.
Connect with us on:
Twitter | LinkedIn | Medium | Newsletter
